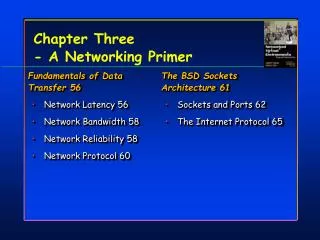
Lecture 21: Network Primer
This lecture covers the fundamental concepts of IP header fields, including the Time To Live (TTL), Type of Service, and fragmentation details. It explains how the TTL works to prevent packets from traversing the network indefinitely and discusses various addressing classes (A, B, C) along with network and host identification. The role of subnet masks in partitioning networks, as well as variable-length network masks, is also explained. This session is vital for students of computer networks aiming to grasp packet structure and routing principles.

Lecture 21: Network Primer
E N D
Presentation Transcript
Lecture 21: Network Primer 7/9/2003 CSCE 590 Summer 2003
Version Hdr Len Type of Service Total Length in Bytes IP Identification Number (Frag ID) DF MF Fragment Offset (13 bits) R TTL IP Protocol Header Checksum Source IP Address Destination IP Address Options (Variable Length 0-40 bytes, padded with 0’s) 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 20 16 12 8 4 0 17 5 21 9 1 13 2 22 18 14 6 10 7 19 3 15 23 11 IP Header
IP Header Fields: TTL • TTL: Time To Live, 8 bits, maximum number of hops a packet can take. • Each router along the way decrements it • If it reaches zero, that router returns an ICMP time-exceeded packet to the source • This keeps lost and looping packets from wandering the Internet forever • Can be used for evasion and reconnaissance • Insert a packet with a TTL that expires into a stream to break up signature an IDS may see, but it times out before it ever gets to the host
TTL Example 10/01-12:45:07.501646 210.181.246.201:1310 -> 129.252.243.173:80 TCPTTL:111 TOS:0x0 ID:51149 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK =+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+= 10/01-12:45:07.501804 210.181.246.201:1310 -> 129.252.243.173:80 TCP TTL:109 TOS:0x0 ID:51149 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK =+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+= 10/01-12:45:07.502067 210.181.246.201:1310 -> 129.252.243.173:80 TCP TTL:107 TOS:0x0 ID:51149 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK =+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+= 10/01-12:45:07.502089 210.181.246.201:1310 -> 129.252.243.173:80 TCP TTL:105 TOS:0x0 ID:51149 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK
TTL Example 10/01-12:45:07.502751 210.181.246.201:1310 -> 129.252.243.173:80 TCPTTL:3 TOS:0x0 ID:51149 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK =+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+= 10/01-12:45:07.502757 210.181.246.201:1310 -> 129.252.243.173:80 TCPTTL:1 TOS:0x0 ID:51149 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK =+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+= 10/01-12:45:10.467907 210.181.246.201:1310 -> 129.252.243.173:80 TCPTTL:111 TOS:0x0 ID:51332 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK =+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+= 10/01-12:45:10.467940 210.181.246.201:1310 -> 129.252.243.173:80 TCPTTL:109 TOS:0x0 ID:51332 IpLen:20 DgmLen:48 DF ******S* Seq: 0xDAE61E12 Ack: 0x0 Win: 0x4000 TcpLen: 28 TCP Options (4) => MSS: 1460 NOP NOP SackOK
IP Header Fields • IP Protocol: 8 bits, what type of header follow the IP header (which IP protocol is being used) • ICMP = 1 • TCP = 6 • UDP = 17 • And others • Header Checksum: 16 bits, checksum of the IP header
IP Header Fields: Addresses • Source IP address: 32 bits, IP address of the sending system – can be spoofed (faked) • Destination IP address: 32 bits, IP address of the destination machine • Addresses typically represented in dotted decimal notation • A decimal number between 0-255 for each byte of the 4 byte address • 0 and 255 are broadcast addresses (0 is legacy) • Ex: 129.252.49.4
IP Addressing • Classes of addresses • Splits an address into a network ID and a host ID • Class A: (24 bits for the host ID) >16 million hosts. 0.0.0.0 -> 127.255.255.255 • Class B: (16 bits for the host ID) 65535 hosts, 128.0.0.0 -> 191.255.255.255 • Class C: (8 bits for the host ID) 255 hosts, 192.0.0.0 – 223.255.255.255 • USC has a Class B network • Network ID =129.252.0.0 • Host IDs range from 129.252.0.0 -> 129.252.255.255
Network Masks • We don’t want to just enumerate all of the 65535 hosts of 129.252.0.0 • Use netmasks (subnet masks) to carve it up into smaller networks • Netmasks tell hosts how much of the address to mask off as the Network ID • Ex. 255.255.255.0 = first 24 bits are 1s. Given 129.252.49.0, it masks off 129.252.49 and leaves the last byte for host Ids between 0-255 (really 1-254)
Variable Length Network Masks • Common masks are 16 (255.255.0.0) and 24 (255.255.255.0) bits • Variable length masks are like 25 bits = 255.255.255.128 and splits a Class C in half. • For a network ID of 129.252.49.0/25, addresses range from 129.252.49.0-129.252.49.127. Broadcast addresses = 129.252.49.0 and 129.252.49.127 • The other half is represented 129.252.49.128/25 and addresses range from 129.252.49.128-129.252.49.255. Broadcast addresses = 129.252.49.128 and 129.252.49.255 • The more you split it, the more addresses you lose to broadcast and network addresses.
Directed Broadcasts • Ping either the network (.0) or broadcast address (.255) and a router amplifies (broadcasts) the ping out to every machine on that network • Pinging 129.252.49.255 will send a ping to all the hosts in 129.2522.49.0-129.252.49.255 • This capability should be turned off on routers • Smurf (ICMP) • Spoof your source address to be your victims address, send an ICMP echo request to a bunch of broadcast addresses, and the victim is flooded with the echo replies • Fraggle (UDP) • Same idea, but with UDP port 7 (echo port) • http://www.netscan.org/
IP Header Fields: Options • Rarely used • Security - IPSec • Stream identification • Internet Timestamp (records timestamp at each hop) • Record Route • Loose Source Routing • Strict Source Routing
code length ptr IP address 1 IP address 2 … IP address 5 IP Route Options • Codes: • 0x07 = Record Route Option • 0x83 = Loose Source Routing • 0x89 = Strict Source Routing • Length = determone # of IP addresses in list • Pointer (ptr) = pointer to current IP address in option list
Record Route Option • Like a one packet traceroute except it really does say the route it took • Records addresses of all routers packet travels through • Source must set the option, and destination must process the list to extract the data • Source makes an empty list of IP addresses, so it must allocated enough space for the entire path • Could be used for reconnaissance
A 1 2 3 B 4 Loose Source Routing • Gives a list of required nodes a packet must travel through in its route • It is loose because it can go through other nodes than the ones in the list • Example: Loose Source Route through 4.
Strict Source Routing • Specifies the exact path a packet must go for up to the first 9 hops • It is strict because it must go through this path or not at all. • Ex: Strict Source Route through 1,4,3 A 1 2 3 B 4
Source Routing Bad? • Could redirect packets to an eavesdroppers machine • Could be used to bypass ACL (Access Control Lists), firewalls, or IDSs
Internet Control Message Protocol • ICMP used to relay problems and for testing • No port number like TCP or UDP • Message Types and Codes instead • No concept of client or server (no ICMP services listening on a machine) • Like UDP, delivery isn’t guaranteed • Most ICMP messages do not expect a response • Broadcast ICMP traffic possible
ICMP Queries • Ping • Echo Request (8,0) (type,code) • Echo Reply (0,0) • Timestamp • Timestamp request (13,0) • Timestamp reply (14,0) • Information: Obsoleted by bootp, RARP, DHCP • Information Request (15,0) • Information Reply (16,0) • Address Mask • Address Mask Request (17,0) • Address Mask Reply (18,0)
ICMP Error Messages • Destination Unreachables (Type 3) • Network Unreachable (Code 0) – routers return this when a machine tries to access a network that isn’t available • Host Unreachable (Code 1) - routers return this when a machine tries to access a host that isn’t available • Protocol Unreachable (Code 2) – host can return this when a remote machine tries to access a protocol that isn’t active • Port Unreachable (Code 3) - host can return this when a remote machine tries to access a port that isn’t active • Fragmentation Required, DF flag set (Code 4) – router sends this when fragmentation is needed and DF bit is set
ICMP Error Messages • More Destination Unreachables (Type 3) • Source Route Failed (Code 5) - router sends this router when a packet can’t be forwarded to the next hop specified in the its Source Route option • Destination Network Unknown (Code 6) - Should use Network Unreachable instead • Destination Host Unknown (Code 7) – if router can verify destination host does not exist, else use Host Unreachable • Source Host Isolated (Code 8) – Use Network Unreachable or Host Unreachable instead
ICMP Error Messages • More Destination Unreachables (Type 3) • Network Administratively Prohibited (Code 9) – routers, firewalls may send if packets aren’t allowed to that network • Host Administratively Prohibited (Code 10) – routers, firewalls may send if packets aren’t allowed to that host • Network Unreachable for TOS (Code 11) – if route to a destination network is not available for the Type of Service specified in packet • Host Unreachable for TOS (Code 12) - if route to the destination host is not available for the Type of Service specified in the packet • Communication Administratively Prohibited (Code 13) - routers, firewalls may (optional) send if packets aren’t allowed by filtering policy
ICMP Error Messages • Source Quench (4,0) – If a router or host does not have enough resources to handle packets, sends this to get sender to back off a bit • Time Exceeded (Type 11) • Time to Live Exceeded in Transit (Code 0) – the TTL field has reached zero • Fragment Reassembly Time Exceeded (Code 1) – took too long getting all fragments • Parameter Problem (Type 12) - problem with the parameters of a packet header • Pointer Indicates the Error (Code 0) – pointer to problem byte • Missing a Required Option (Type 1) • Bad Length (Type 2)
ICMP Error Messages • Redirect (type 5) • Redirect Datagram for the Network (Code 0) • Redirect Datagram for the Host (Code 1) • Redirect Datagram for the TOS & Network (Code 2) • Redirect Datagram for the TOS & Host (Code 3) • A router receives a packet from a host and it identifies from its routing tables that the next hop to the packet’s destination is on the same network that the packet just came from, then a redirect message is sent to the source host • Router forwards packet to the correct next hop • When source gets the redirect, it modifies its route table accordingly
ICMP Routing • Router Advertisement (9,0) – routers can advertise their interfaces for hosts updating their route tables dynamically • Router Solicitation (10,0) – hosts broadcasting, looking for routers on their subnet
Message Type Checksum Message Code 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 0 1 2 3 ICMP Header
References • Chapter 6