Cyber Liability
Cyber Liability. What School Districts Need to Know. Data Breaches – Growing In Number. Between January 1, 2008 and April 4, 2012 314,216,842 reported records containing “sensitive personal information” have been involved in security breaches!. Source: Privacy Rights Clearinghouse


Cyber Liability
E N D
Presentation Transcript
Cyber Liability What School Districts Need to Know
Data Breaches – Growing In Number Between January 1, 2008 and April 4, 2012 314,216,842 reported records containing “sensitive personal information” have been involved in security breaches! Source: Privacy Rights Clearinghouse A Chronology of Data Breaches Updated as of April 4, 2012 www.privacyrights.org 2
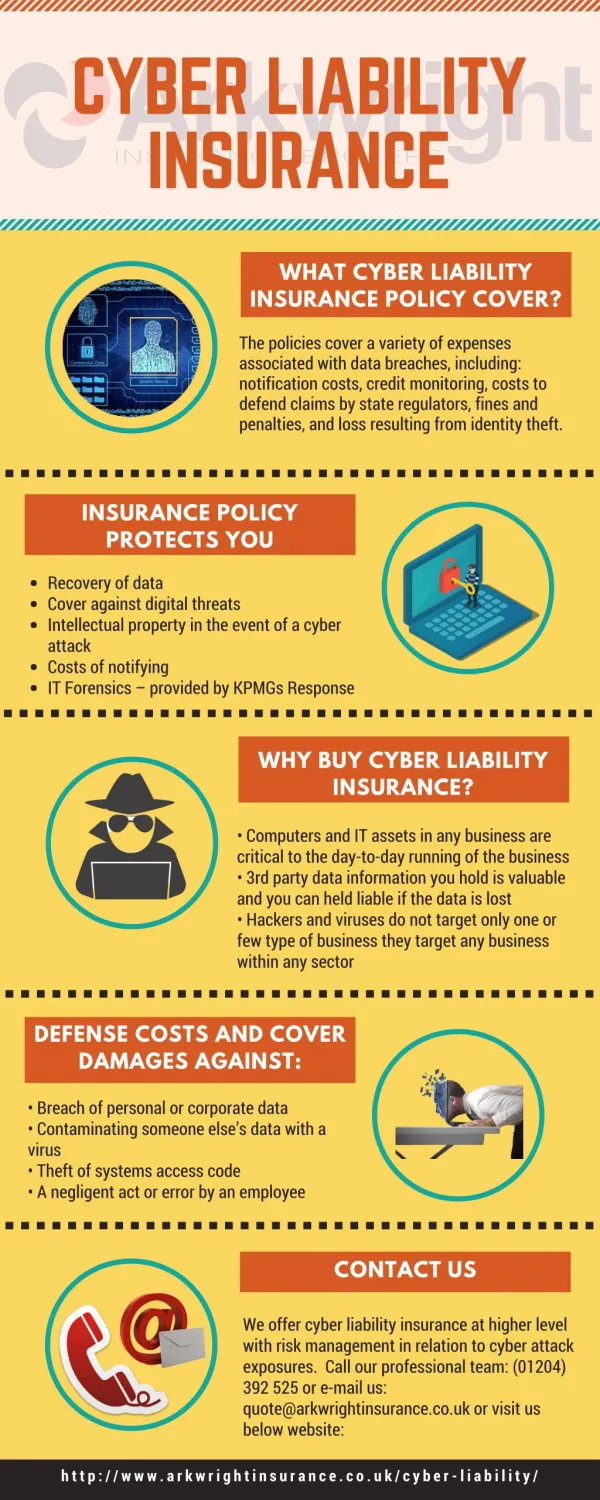
Data Breaches Categories • Lost or stolen laptops, computers, flash drives or other computer storage devices • Backup tapes misplaced or lost in transit • Hackers • Rogue employees • Poor business practices • Internal security failures • Viruses, malware • Information in dumpsters 3
Sources of Data Breaches Privacy Rights Clearinghouse – Chronology of Data Breaches 1/1/08-4/4/12 4
Breaches – Education Sector • In the First half of 2012 • 16% of reported breaches were in the education sector and exposed 1,676,901 records. • Source: Ponemon Institute and Symantec 5
Causes of Breaches • Negligence – 39% • Employees • Contractors • Malicious/Criminal Attacks – 37% • External and internal • System Glitches – 24% • Including a combination of both IT and business process failures Source: Ponemon Institute, LLC – “2011 Annual Study: U.S. Cost of a Data Breach” 6
Office Computers Stolen October 2010 • Farmers Insurance - San Diego, CA. Theft of office computers compromised policyholder information: names, addresses, social security numbers, telephone numbers, and drivers license numbers. 7
Documents in Dumpster January 2011 • Thousands of MetLife client documents with names, addresses, social security numbers, birth dates, and account balances were disposed of into dumpsters when an office was moving locations. • MetLife has been ordered to provide credit fraud protection for everyone affected. They were also required to pay $75,000 to the State of Illinois Director of Insurance. • The error was caused by a printer malfunction. At least 50 customers reported a problem with their accounts. 8
Custodial Renegade December 2011 • An owner of a cleaning company was arrested for stealing personal information from Eagle Harbor Country Club members. • Stolen information was used to open fraudulent credit cards and bank accounts. 9
Hackers February 2012 • DHI Mortgage of Dallas, TX became aware of a software security breach that occurred on its internet loan prequalification system. Individuals who provided their information online may have had their names, social security numbers, dates of birth, employment, and income/asset information exposed. 10
A Simple Mistake January 31, 2012 • Ernst & Young auditor mailed a flash drive and decryption code containing information of current and former Regions Financial employees. The envelope arrived with the decryption code, but no flash drive. The data included names, info regarding 401K retirement plans, social security numbers, and possible birthdates. Regions employs about 27,000 people. 11
Robin Hood Hacktivists December 24, 2011 • Global intelligence company Stratfor was targeted by hacktivist collective “Anonymous.” • Data stolen included 68,000 credit card numbers (36,000 were not expired), 860,000 usernames and passwords, and 5 million emails that could contain information on Fortune 500 companies who subscribe to Stratfor. • Hackers claim to have made $1M in donations to charities. 12
Sneaky Student Evergreen Public Schools • Had a data breach that cost the school district $62,000 when a former student was able to obtain an administrative login and password to the district’s system. Upon obtaining these he gained access to the teach payroll system and used the bank account information it contained in order to make fraudulent charges and sign up for credit cards. 13
Intruder Beverton School District • Lost 1,600 current and former employees’ personal information when an intruder stole overtime payment receipts from the district’s storage sheds. In response, the district contracted a security firm who advised them to offer a years worth of credit monitoring to the affected teachers. 14
A Costly Oops! Seattle School District • Accidentally disclosed half of their workforce’s information when it included Social security numbers and home addresses in information it sent to a local teacher’s union. As a result it agreed to pay for credit monitoring services to the 5,000 individuals who were affected. 15
Cyber Crackdown Houston School District • Involved the FBI when they discovered a hacker had compromised their network and gained access to employee bank account numbers as well as student grades. After the incident the superintendent realized the serious threat that hackers pose to their information systems and put forward a plan to spend $10-$15 million dollars in order to enhance their cyber security systems. 16
Snatched Laptop Reynoldsburg City School District • Had a laptop stolen from a network technician’s car, resulting in 4,200 students’ personal information, including Social Security numbers, being stolen. In response, the district negotiated a contact with a credit monitoring services to provide credit monitoring for a year to all the affected students. This had an approximate cost of $46,200. 17
What is the Average Direct Cost After a Breach Occurs? • Notification Costs • Detection and Escalation Costs • Other Costs • Direct Cost = $59 per record • Total costs average $194 per record for all industry classes Source: Ponemon Institute, LLC – “2011 Annual Study: U.S. Cost of a Data Breach” 18
First Party Third Party Breach = Potential Cascade of Losses • Loss of Private Data • Notification Costs • Cost to Change Account Numbers • Publicity Costs • Customer Suits • Suits from Customers alleging invasion of privacy and other causes of action • Cyber Extortion • Ransom Payment • Other Expenses, including fees of an independent negotiator or consultant • Other Suits • Suits from prospective customers alleging invasion of privacy. 19
Where’s The Coverage • Commercial Crime Form? • General Liability? • Professional Liability Policy? • D&O Liability Policy? 20
Surety Association Computer Crime Computer Crime Policy has three (3) major exclusions: • Loss resulting directly or indirectly from theft of confidential information; • Indirect or consequential loss of any nature; • Potential income, including but not limited to interest and dividends. 21
ISO Commercial Crime Policy Computer Fraud - We will pay for loss of or damage to “money”, “securities” and “other property” resulting directly from the use of any computer to fraudulently cause a transfer of that property from inside the “premises” or “banking premises”: • To a person (other than a “messenger”) outside those “premises”; or • To a place outside those “premises.” 22
ISO Commercial Crime Policy, cont. Other Property Any tangible property other than “money” and “securities” that has intrinsic value but does not include any property excluded under this policy. Exclusion – Indirect Costs Loss that is an indirect result of any act or “occurrence” covered by this policy including, but not limited to, loss resulting from: • Your inability to realize income that you would have realized had there been no loss of or damage to “money”, “securities” or “other property. • Payment of damages of any type for which you are legally liable. But, we will pay compensatory damages arising directly from a loss covered under this policy. • Payment of costs, fees or other expenses you incur in establishing either the existence or the amount of loss under this policy. 23
General Liability – Personal Injury Coverage B Personal and Advertising Injury Liability • Insuring Agreement • We will pay those sums that the insured becomes legally obligated to pay as damages because of “personal and advertising injury” to which this insurance applies. We will have the right and duty to defend the insured against any “suit” seeking those damages. • “Personal and advertising injury” means, oral or written publication, in any manner, of material that violates a person’s right of privacy; Source: ISO CG 00 01 12 04 24
GL Insurers Seek to Avoid Cyberliability In a move to eliminate exposure to data breaches, insurers of general liability coverage have been excluding advertising injury and personal injury on policies of insureds who maintain a significant amount of personal and/or financial data. 25
D&O Liability Insurance • Data breach is predominantly a corporate liability exposure. • Invasion of privacy is typically excluded. • Coverage for mental anguish/emotional distress is limited to employment practices claims. • Public company D&O only protects the entity against claims relating to the company’s securities. 26
Cyber Liability Insurance Coverage • A risk management option that mitigates exposure to data breaches • First party coverage • Third party (liability) coverage 27
First Party Coverage • Computer forensic costs • Legal costs to determine legal compliance requirements • Privacy notification of data breach, including credit monitoring expenses required by applicable law • Crisis Management expense, including law firm and public relations firm • Extortion payment and expenses • E-vandalism – cost of blank media and cost of reproduction • Business interruption coverage – loss of business income during impairment of operations due to fraudulent access or transmission as to the insured’s system 28
Computer Forensic Experts • Critical to helping determine the extent of a breach and leaving breach evidence intact • Computer evidence has been the smoking gun in many high profile cases • Surveys show that insureds who proceed with notification prior to having forensic validation of scope of breach pay 54% more in notification costs • Average fees run from $250 to $350 per hour, and time incurred depends on scope of breach 29
Legal Representation to Determine Compliance Requirements • Notification and consumer protection laws vary from state to state as to who must be notified and the manner of notification • 46 states have breach laws in place as of 2/6/2012 • It is critical to have experienced counsel to review the forensic expert results, and determine appropriate notification and breach remediation actions • Counsel may also be required to negotiate with regulators and state attorneys general • Credit monitoring may be required by applicable state law 30
South Carolina Code Ann § 39-1-90 • Applies to breaches of encrypted personal indentifying information in both paper and electronic records. • First name or last name plus social security number, drivers license, financial account number, credit card or debit card number in combination with any required code, access code or password. • Law does not require notification in the event of an unauthorized but good-faith acquisition of personal indentifying information by an employee of the entity for the purposes of it’s business if the personal identifying information is not used or subject to further unauthorized disclosure. 31
Notification Costs • Maximizing coverage for notification costs is a priority, and these costs are a primary reason that organizations purchase cyber coverage • There are two options for this coverage that are available: • Specified dollar limit • Maximum number of individuals to be notified 32
Claims Arising from Rogue Employees and Independent Contractors • Most policies include coverage that extends to loss resulting from a breach of data that is held or processed by an independent contractor. • Malicious insider breaches by employees tend to be harder to detect and remediate. The average time to contain such breaches is more than 45 days.* *Experian Data Breach Resolution Blog 33
Privacy and Security Insurance Coverage Third Party Coverage • Broad definition of claim to include demands for monetary and non-monetary relief; civil, regulatory and criminal proceedings. • Coverage for loss, defense costs, punitive damages, and fines/penalties. • Require coverage that extends to mental anguish and emotional distress allegations. 34
Cyber Liability Polices Vary Significantly • Discuss your operations and all privacy and security exposures with your insurance professional. • Seek broad coverage for all of your operations, including those that are decentralized. • Purchase coverage that extends to your paper files, website, computers, laptops, and other peripheral devices. • Consider policy limits on first party coverages, regulatory actions, fines/penalties. 35
Make Informed Decisions as to Risk Management Options • Review technology, best practices and insurance for your optimal defense and protection. • Assess your exposures, including employees, vendors, independent contractors and clients. • Assess your potential costs and liabilities in connection with a breach. • Understand that poor economic conditions may increase your exposure. 36
Contact Info Tommy Suggs President & CEO 803.227.4797 tsuggs@keenansuggs.com www.keenansuggs.com www.theksblog.com Visit Us At Booth #8 www.facebook.com/keenansuggs KeenanSuggsSC 38