Assembly Code Verification Using Model Checking at SUTD
Explore how assembly code verification using model checking at Singapore University of Technology and Design offers reliability, circumvents compiler issues, and achieves CPU-similar targets with accuracy, extensibility, and ease. Challenges like complexity and scalability are addressed with design goals for efficiency and usability.


Assembly Code Verification Using Model Checking at SUTD
E N D
Presentation Transcript
Assembly Code Verification Using Model Checking Hao XIAO Singapore University of Technology and Design
Outline • Motivation • Approach overview • ILA module @ PAT • On-going & future work
Benefits • Achieve more reliability. • More software components can be verified. • Circumvent problems caused by compiler. • The verification target is most close to what is running on a CPU than the source code. • Easy to verify. • Binaries have more elegant syntax and well defined semantics than source code.
Challenges • Instruction complexity. • Lack of high level semantic information. • Dynamic jump and call, no clear boundaries for “function”. • How to specify properties for assembly code. • Scalability. • Assembly code is much longer than source code.
Design Goals • Accuracy: Faithfully handle the complex instructions in some ISA. • Extensibility: Easy extensible to handle different Instruction Set of various architecture. • Ease of Use: Those who are not familiar with temporal logic or assembly language should also find it is useful. • High Efficiency: Scalable to large programs.
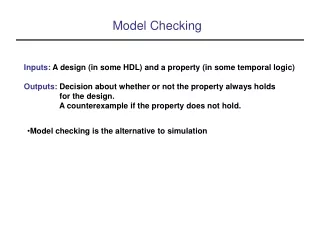
Approach Overview (1) Parser Properties User & Built in properties Static Analyzer Model Checker Counter Example Vine Parser ELF Emulator Vine IL
Approach Overview (2) • Accuracy and Extensibility: Vine IL. • Ease of Use: Built in properties, if source is available, link counter examples back to source. • High Efficiency: property guided abstractions techniques for state space reduction; Function abstraction.
ILA @ PAT • Vine IL • Emulator • Static Analyses • Built in properties • Example-buffer overflow checking
Vine IL Binary file Assembly VEX IR Vine IL Libbfd LibVex Vine
Emulator(State builder) • Emulator is used to generate the successor states based on the current state. • A state consists of CPU registers, PC, memory. • Separate global states from local states. • Byte precision memory model.
Static Analyses for Space Reduction • Stack Analysis • Dead Variable Analysis. • Value Set Analysis • Interrupt Flag Analysis. • Path Reduction
Built-in Properties • Stack overflow checking • Integer overflow checking • Null pointer deference. • Division by zero checking • Uninitialized variable checking • Data race checking
Example-Buffer Overflow Checking • Buffer overflow in assembly level: • write to a memory location beyond the boundaries of current stack frame. • Identify instrumentation point: • find write operations which have a variable d as its destination address. • Assertion instrumentation: • Add assertion d > %ebp && d < %espbefore the write instruction. • Model checking assertions.
Example-Assembly Code s1 s1 s5 s2 s6 s3 s4
Control Flow Graph S1 J1 S2 S3 J2 S4 S5 J3 S6
CFG for Instrumented Code esp1 = esp0 - 0x4 M[esp1] = ebp0 ebp1 = esp1 esp2 = esp1 - max{0, 15} esp3 = esp2 – 0x20 S1 J1 M[ebp1 +0x8]>1 eax0= M[ebp1 + 0xc] eax1= M[eax0 + 0x4] M[esp3 + 0x18] = eax1 M[esp3 + 0x1c] = 0 S3 ebx0 =φ(S3,S4.2,M[ esp3 + 0x1c]) eax2 = M[esp3 + 0x18] eax3 = strlen (eax2) S4.2 S5 M[eax7] = edx0 M[esp3+0x1c] = M[esp3 + 0x1c] + 1 Error eax7 > ebp1 && eax7 < esp3 A1 eax4 = M[esp3 + 0x1c] eax5 = eax4 + M[esp3 + 0x18] edx0 = M[eax5] eax6 = esp3 + 0x10 eax7 = M[esp3 + 0x1c] + eax6 S4.1 J3 eax3 < ebx0 S6
On-going & future Work • Implementation. • More abstraction techniques(e.g., irrelevant code elimination). • Symbolic model checking
The End Thanks !