Token-Based Firewall Implementation on Lambda Grid Research
Discusses Token-Based Firewall scenario admitting flows to Lambda Grid, with emphasis on Multidomain Service & Control Plane Policies. Prototype on Intel NPU platform with HMAC-SHA1 algorithm. Introduces experimental results from Super Computing 2005.

Token-Based Firewall Implementation on Lambda Grid Research
E N D
Presentation Transcript
Token Based Firewalls GGF-16 FirewalI Issues Research Group Athens, Feb 14th 2006 Welcome Leon Gommans - University of Amsterdam leon.gommans@science.uva.nl LAMBDAGRID
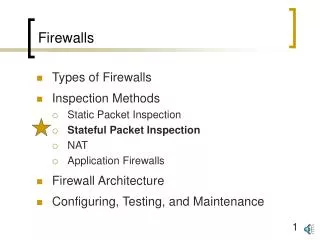
Content Progress on material presented at GGF-14 Context. Firewall scenario. Experiment. Results. Leon Gommans UvA 14/2/06 1/8
Context: Research on deployment scenario’s for the Lambda Grid created by the GLIF community Leon Gommans UvA 14/2/06 2/8
Token Based Firewall scenario admitting flows to a Lambda Grid Multidomain Service & Control Plane Policy + C + C Grid App Grid Service X DRAC, UCLP,GMPLS + C + C + C + C T T Token Admit Lamda Grid (GLIF) Token admit Token Re- Move Token Insert Rejected packets DMZ DMZ Internet • Token Insert Firewall generates tokens inside IP packets for specific flows identified by C (Capabilities) using a HMAC-SHA1 algorithm with a key at wire speed. • Other flows which are not identified (green) or authorized follow the “regular” path. • A Token Admit Firewall is used to recognize the tokens inside every IP packet at wire speed and subsequently admit the flows onto link blue of the lambda grid. • Keys are issued on behalf of the owner of Lambda Grid link blue by the service & control plane. The service plane hereto deploys AAA mechanisms. • Service plane provisions the corresponding path configurations. Grid Service Y Secure and Trusted control Channel Leon Gommans UvA 14/2/06 3/8
Prototype implementation on Intel NPU development platform IP HEADER DATA CRC Capabilities + MASK C C C C Token Key HMAC-SHA1 algorithm Token IP HEADER Options DATA CRC T Leon Gommans UvA 14/2/06 4/8
Intel IXP 2855: 11M HMAC-SHA1 operations/sec @ 1.5 GHz Leon Gommans UvA 14/2/06 5/8
Experiment Super Computing 2005 NPU programming based on extensions of FFPF ( ffpf.sourceforge.net ) from EU Scampi project. T T Leon Gommans UvA 14/2/06 6/8
First results: Single Thread / Single Micro-Engine implementation using single 1 gb/s input port using UDP iperf. Working now on multi-thread implementation and later put it on multiple Micro-Engines (up to 16 available) Leon Gommans UvA 14/2/06 7/8
Conclusion Tokens allow applications to be admitted to “owned” optical lightpath resources Token based design allows integration with regular firewall scenario’s Tokens allow temporal split between (service, based complex) collection of authorization(s) and use of the authorization. Tokens can be derived from higher-level Certificate based authorization infrastructures and therefore be matched with the VO based models. Crypto-functions in a single NPU is likely to support high bandwidth application up to 10 Gb/s. Acknowledge Scientific Input: Mihai Cristea, John Vollbrecht, Robert Meijer, Cees de Laat, Franco Travostino, Yuri Demchenko, Li Xu, Fred Wan, Bill Allcock, Frank Siebenlist. Equipment: Intel Corporation Funding: SURFnet GigaPort NG, EU project NextGrid. Leon Gommans UvA 14/2/06 8/8