Computer Security for Student-Administered Computers
This guide explores the critical security challenges faced by student-administered computers. It outlines common security incidents, such as port scanning, buffer overrun attacks, and denial of service attacks, emphasizing the importance of vigilance and proactive measures. The document also discusses various defenses, including policies, encryption, antivirus software, and firewalls, as well as the significance of risk management. Additionally, it offers practical advice on securing Windows 2000 systems through planning, installation, and updates, ensuring a comprehensive understanding of computer security.

Computer Security for Student-Administered Computers
E N D
Presentation Transcript
Agenda • What's the Problem? • Security Risk • Security Incidents • Defenses • Vigilance
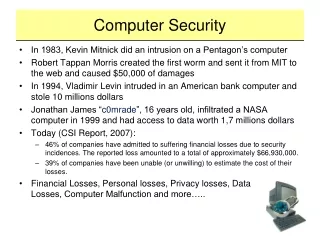
What's the Problem at UW? • http://staff.washington.edu/dittrich/talks/security/incidents.html • port-scanning: looking for systems to target • buffer-overrun attacks: command execution via coding errors • open account exploits: to login • packet sniffing: to learn login secrets • trojan horse attacks: to fool user into executing infected program • shared/stolen accounts: to login • denial of service attacks: to prevent or hamper use of computers • file storage: to pirate software/music/etc. • forging email or other electronic messages: to harass/threaten/fool
Security Goals • Microsoft Prescriptive Guidance: Security Operations Guide for Windows 2000 Server • http://www.microsoft.com/technet/treeview/default.asp?url=/TechNet/security/prodtech/windows/windows2000/staysecure/default.asp • Get secure • Stay secure (over time, amidst changes)
Security Risk • Managing risk to protected resources • Resources: data, applications, servers, etc. • what's its value? • Threat: something that could access/harm resources • natural/physical, unintentional/intentional • Vulnerability: point where resource can be attacked • Exploit: use of a vulnerability by a threat • could result in loss of confidentiality, integrity or availability • Risks need to be ranked: low, medium, high
Security Incidents • physical: earthquake, water leak, power failure, etc. • technical vulnerability exploits: attacks, buffer overflows, ... • information gathering exploit: OS identification, wireless leak, social engineering • denial of service exploit: resource removal, physical damage, etc.
Defenses • Data: encryption and backups; antivirus software • Application: developer needs to enforce • Host: limit server to specific roles • Network: blocking and/or encrypting traffic • Perimeter: firewalls; authorized PCs are clean before connecting • Physical: removable media, locks, redundancy, restricted areas • Policies and Procedures: raise awareness and prevent abuse
Windows 2000 Defenses • Planning • Isolation • Installation and Upgrades • Antivirus software • Group Policy/Registry Changes • IPSec/Filtering • Application Lockdown
Windows 2000 Defenses: Planning • What kind? • server: member or domain controller? • workstation? • What role? • basic? web server? cluster? • What’s required for other services? • need to think about this
Windows 2000 Defenses: Isolation • On Internet-connected computer: • gather all upgrades, antivirus software • http://www.washington.edu/computing/software • download • Network Associates/McAfee Netshield (server) • McAfee VirusScan (workstation) • upgrades and updates • burn on CD • Connect to a hub not connected to Internet • Use static, non-routable IP addresses: 10.10.xxx.xxx
Windows 2000 Defenses: Installation and Upgrades • Install Windows 2000 • don’t do it blindly -- read and think about it • Install latest service packs • Install security patches/hotfixes to service packs • Switch to non-privileged account • use RUNAS whenever elevated privileges needed • Watch logs (use EventViewer)
Windows 2000 Defenses: Antivirus • Install Netshield • Install latest upgrades/updates • don’t schedule to update/upgrade (not connected)
Windows 2000 Defenses:Group Policy/Registry Changes • %SystemRoot%\security\templates • Basic • Basicwk.inf (workstation) • Basicsv.inf (member server) • Basicdc.inf (domain controller) • Incremental • securedc.inf (domain controller) • securews.inf (workstations or member servers) • IIS Incremental.inf (IIS only)
Windows 2000 Defenses:Apply AD Group Policy • Active Directory Users and Computers/Domain Controllers/Properties/Group Policy/New • type “BaselineDC Policy” • press enter, then right-click on BaselineDC Policy • select “No Override • Edit/Windows Settings (expand)/Security Settings/Import Policy • locate template BaselineDC.inf and place name in “Import Policy From” box • close Group Policy and then click Close • replicate to other domain controllers and reboot
Windows 2000 Defenses:Apply Member Group Policy • Active Directory Users and Computers/Member Servers/Properties/Group Policy/New • type “Baseline Policy” • Edit/Windows Settings (expand)/Security Settings/Import Policy • locate template Baseline.inf and place name in “Import Policy From” box • close Group Policy and then click Close • repeat above for Incremental template files • replicate to other domain controllers and reboot
Windows 2000 Defenses:Verify Group Policy • Verify with secedit (compare with existing template) • secedit /analyze /db secedit.sdb /cfg xxxxx.inf • look at log file • Test!
Windows 2000 Defenses:Registry Changes (in Baseline) • HKLM\System\CurrentControlSet\Services\Tcpip\Parameters • EnableICMPRedirect=0 • SynAttackProtect=2 • DisableIPSourceRouting=2 • PerformRouterDiscovery=0 • HKLM\System\CurrentControlSet\Services\AFD\Parameters • DynamicBacklogGrowthDelta=10 • EnableDynamicBacklog=1 • MinimumSynamicBacklog=20 • MaximumDynamicBacklog=20000
Windows 2000 Defenses:IP Filtering • Block all ports not needed for servers
Windows 2000 Defenses:Application Lockdown • Read application’s notes on security • IIS • IS Incremental.inf • follow guidelines • SQL Server • change default system DBA passwords • protect DBs with access rights/file permissions
Linux Defenses • Planning • Isolation • Installation and Upgrades • Antivirus software??? • IP Filtering • Application Lockdown
Linux Defenses: Planning • What kind? • workstation? • server? • What servers? • web server? insecure servers? • What apps are required? • What services are required?
Linux Defenses: Isolation • On Internet-connected computer: • gather all upgrades • burn on CD • Connect to a hub not connected to Internet • Use static, non-routable IP addresses: 10.10.xxx.xxx
Linux Defenses: Installation and Upgrades • Install Linux • don’t do it blindly -- read and think about it • put /tmp, /home and /var/log in separate partitions • Install latest upgrades • Switch to non-privileged account • use “su -” whenever elevated privileges needed • Watch logs (usually in /var/log)
Linux Defenses: IP Filtering • tcp wrappers • /etc/hosts.deny • ALL:ALL • /etc/hosts.allow • ALL: 10. LOCAL • sshd: ALL • /etc/xinetd.d • disable=yes for undesired services • killall -USR2 xinetd
Linux Defenses: Apache Lockdown • Apache -- start by restricting everything <Directory /> Options None AllowOverride None Order deny,allow Deny from all </Directory> • then allow by specific directories • want to disable CGI, includes
Linux Defenses: FTP Lockdown • should not use -- sends passwords in plain text • use ssh/scp/sftp instead • /etc/ftpusers • should NOT include root or other privileged accounts • disallow anonymous FTP • should read: class all real *
References • http://www.washington.edu/computing/security • Microsoft Baseline Security Analyzer • for 2000/XP • requires Internet access to run • http://www.microsoft.com/technet/treeview/default.asp?url=/technet/security/tools/Tools/mbsahome.asp • SANS Institute Bookstore (Windows 2000 & Linux) • SANS = System Administration, Networking and Security) • https://www.washington.edu/computing/software/sitelicenses/sans/sw/access.html