Enhancing ICTF with Amazon EC2: A Hands-On Approach for Cybersecurity Training
This document summarizes the integration of the International Capture the Flag (ICTF) competition with Amazon's Elastic Compute Cloud (EC2), allowing students to gain hands-on experience in a realistic cybersecurity environment. Since 2006, UCCS has participated in ICTF, and this initiative aims to simulate the competition's network architecture using EC2. Key aspects include creating and managing Amazon Machine Images (AMIs), understanding cloud networking challenges, and exploring future work such as automation and intelligent security systems. This effort prepares participants for real-world attack and defense scenarios.

Enhancing ICTF with Amazon EC2: A Hands-On Approach for Cybersecurity Training
E N D
Presentation Transcript
ICTF EC2 By Daniel Ruiz
Summary Background ICTF and EC2 Create AMI Manage AMI Cloud Networking ICTF EC2 Network Layout Problems Future Work
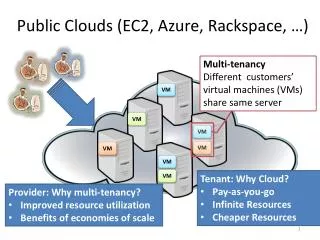
Background ICTF and EC2 • ICTF • International Capture the Flag (ICTF) is a hacking competition held yearly in December • UCCS has been participating in ICTF since 2006 • EC2 • Amazon Elastic Compute Cloud (EC2) is a web service that provides compute capacity in a cloud. • Allow the creation of an Amazon Machine Image (AMI) which is essentially an OS image that can be uploaded and ran within Amazons EC2.
Background Cont. • ICTF EC2 • Is an attempt to mimic the ICTF network from within Amazons EC2 • Goals • Allow students to have hands on experience in an ICTF environment before the competition • Allow for experimentation on attack and defense
Create AMI • Amazon EC2 account • AWS Access Key Identifiers • x.509 certificate • AMI-Tools are needed to create an Linux/Windows AMI • Existing AMI’s can also be used • Amazon Web Service (AWS) Management Console • Elasticfox (Firefox plugin)
Manage AMI • AMI cannot be shutdown only terminated and rebooted • AMI-Tools can be used to manage AMI • GUI Managers are also available: • ElasticFox • AWS Management Console AWS Management Console ElasticFox
Problems • Cloud Security • Cannot run certain attacks (DoS and DDos) from within the cloud • Cost $$$ • IP’s can take up to 24 hours to trickle there way through the internet (Can be solved with Elastic IP) • Can get kicked out of cloud • Would require new account and rebuilding of ICTF images
Future Work • Automate deployment and shutdown of the ICTF Cloud Network • Create an intelligent network intrusion detection system (NIDS) • Experiment with network security solutions such as: • Protocol Intrusion Detection Systems (PIDS ) • Host-Based Intrusion Detection Systems (HIDS) • Honeypots • Tarpits