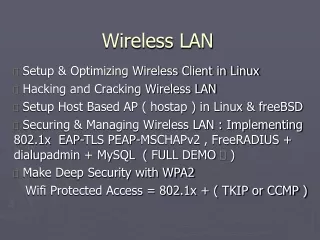
Wireless LAN
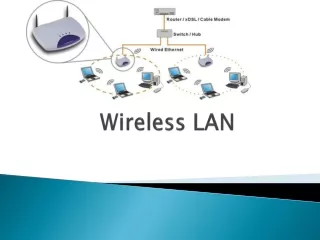
Wireless LAN. About WLAN. IEEE 802.11 standard Use wireless transmission medium such as radio, microwave, infrared to provide network connectivity An Access Point (AP) is installed to act as Bridge between wireless and wired Network

Wireless LAN
E N D
Presentation Transcript
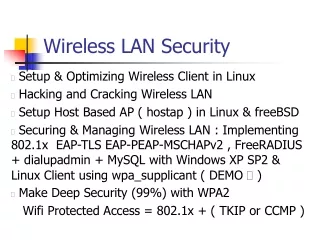
Wireless LAN Network Security
About WLAN • IEEE 802.11 standard • Use wireless transmission medium such as radio, microwave, infrared to provide network connectivity • An Access Point (AP) is installed to act as Bridge between wireless and wired Network • The AP is connected to wired network and is equipped with antennae to provide wireless connectivity • Range (distance between AP and WLAN client) depends on structural hindrances and RF gain of the antenna at the AP • A client is always associated with one AP and when the client moves closer to another AP, it associates with the new AP • Three flavors: 802.11b, 802.11a, 802.11g, etc. Network Security
802.11 Architecture • Access Point (AP): • Any entity that has station functionality & provides access to distributed system • They transmit and receive radio frequencies • Basic Service Set (BSS): • Set of stations controlled by a single coordination function • Every BSS has an identification (ID) called the BSSID which is the MAC address of the AP servicing the BSS Network Security
Architecture continued • Extended service set (ESS): A set of two or more connected BSSs with APs connected through a Distribution System. Each ESS has an ID called the ESSID which is a 32-byte character string. • Distribution system (DS): Connects APs in an ESS. The concept of a DS can be used to increase network coverage through roaming between cells. Network Security
Services • Services provided by distribution system: • Distribution • Integration • Association • Re-association • Disassociation • Services provided by stations: • Authentication & de-authentication • Privacy • Data delivery Network Security
Station types • No-transition • A station is either stationary or moving only inside a BSS • BSS-transition • A station can move from one BSS to another, but inside one ESS • ESS-transition mobility • A station can move from one ESS to another Network Security
WLAN Protocol Architecture Network Security
MAC Sublayers - DCF Distributed Coordination Function • It uses CSMA/CD, contention based (without pre-coordination) • The “listen before talk" operating procedure (first sense then transmit) • Before sending a frame, the source station senses the medium. After a station is found to be idle, the station waits for a period of time DIFS – Distributed InterFrame Space; then the station sends a control frame called RTS – Request to send • After receiving RTS and waiting for period of time SIFS – Short interframe space, the destination station sends control frame CTS – clear to send back to source. It indicates that destination is ready to receive data • The source station sends data after waiting for amount of time equal to SIFS • The destination sends ACK to ensure delivery of frame Network Security
MAC Sublayers - PCF Point Coordination Function • Optional access method, works only in infrastructure network • High priority than DCF • A centralized contention-free polling access method • AP performs polling of stations one after another • To give priority to PCF over DCF: PIFS (PCF IFS) and SIFS are defined • SIFS is same as in DCF • PIFS is shorter than DIFS: If at the same time, a station wants to use only DCF and AP wants to use PCF, AP gets priority Network Security
WLAN Benefits • Convenience • Mobility: Nomadic access • Productivity • Deployment • Expandability • Low Cost: no wiring required • Robust Network Security
WLAN disadvantages • Security • Range • Reliability • Speed • Radio emissions • Hidden and exposed station problem Network Security
WLAN : 802.11b • The most popular 802.11 standard currently in deployment. • Supports 1, 2, 5.5 and 11 Mbps data rates in the 2.4 GHz ISM (Industrial-Scientific-Medical) band Network Security
WLAN : 802.11a • Operates in the 5 GHz UNII (Unlicensed National Information Infrastructure) band • Incompatible with devices operating in 2.4GHz • Supports Data rates up to 54 Mbps. Network Security
WLAN : 802.11g • Supports data rates as high as 54 Mbps on the 2.4 GHz band • Provides backward compatibility with 802.11b equipment Network Security
Standards in process • 802.11ac : <6GHz throughput (Dec 2013) • 802.11ad : 60 GHz throughput (Dec 2012) • 802.11af : TV whitespace (Jun 2014) • 802.11ah : 1 GHz throughput Sensor Network (May 2015) • 802.11ai : Fast initial link setup (Sep 2014) Network Security
Recommended Reading • WLAN MAC layer frame format & frame types • Physical layer specifications: IEEE 802.11 FHSS, DSSS, Infrared, OFDM etc • Network Allocation Vector • WEP security service • Wireless transmission media • Bluetooth architecture & frame format • CSMA, ALOHA Network Security