Auditing IT Governance Controls
Auditing IT Governance Controls. Lesson Objectives. After studying this topic, you should: • Understand the risks of incompatible functions and how to structure the IT function.

Auditing IT Governance Controls
E N D
Presentation Transcript
Lesson Objectives After studying this topic, you should: • Understand the risks of incompatible functions and how to structure the IT function. • Be familiar with the controls and precautions required to ensure the security of an organization’s computer facilities. • Understand the key elements of a disaster recovery plan. • Be familiar with the benefits, risks, and audit issues related to IT outsourcing.
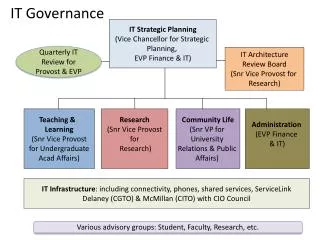
IT Governance Information technology (IT) governance is a relatively new subset of corporate governance that focuses on the management and assessment of strategic IT resources. Key objectives of IT governance are to reduce risk and ensure that investments in IT resources add value to the corporation.
IT Governance Controls This controls focus on: 1. Organizational structure of the IT function 2. Computer center operations 3. Disaster recovery planning
STRUCTURE OF THE INFORMATION TECHNOLOGY FUNCTION • The organization of the IT function has implications for the nature and effectiveness of internal controls, which, in turn, has implications for the audit.
Centralized Data Processing Under the centralized data processing model, all data processing is performed by one or more large computers housed at a central site that serves users throughout the organization.
Related Terms Database Administration • Centrally organized companies maintain their data resources in a central location that is shared by all end users. In this shared data arrangement, an independent group headed by the database administrator (DBA) is responsible for the security and integrity of the database.
Data Processing • The data processing group manages the computer resources used to perform the day-to-day processing of transactions. It consists of the following organizational functions: data conversion, computer operations, and the data library.
Data Conversion. The data conversion function transcribes transaction data from hard-copy source documents into computer input. For example, data conversion could involve keystroking sales orders into a sale order application in modern systems, or transcribing data into magnetic media (tape or disk) suitable for computer processing in legacy type systems.
Computer Operations. The electronic files produced in data conversion are later processed by the central computer, which is managed by the computer operations groups. Accounting applications are usually executed according to a strict schedule that is controlled by the central computer’s operating system.
Data Library. The data library is a room adjacent to the computer center that provides safe storage for the off-line data files. Those files could be backups or current data files. For instance, the data library could be used to store backup data on DVDs, CD-ROMs, tapes, or other storage devices.
Systems Development • The information systems needs of users are met by two related functions: system development and systems maintenance. • Systems Development is responsible for analyzing user needs and for designing new systems to satisfy those needs. The participants in system development activities include systems professionals, end users, and stakeholders.
Systems professionals include systems analysts, database designers, and programmers who design and build the system. Systems professionals gather facts about the user’s problem, analyze the facts, and formulate a solution. The product of their efforts is a new information system.
End users are those for whom the system is built. They are the managers who receive reports from the system and the operations personnel who work directly with the system as part of their daily responsibilities.
Stakeholders are individuals inside or outside the firm who have an interest in the system, but are not end users. They include accountants, internal auditors, external auditors, and others who oversee systems development.
Systems Maintenance • Once a new system has been designed and implemented, the systems maintenance group assumes responsibility for keeping it current with user needs. The term maintenance refers to making changes to program logic to accommodate shifts in user needs over time.
Segregation of Incompatible Functions Operational tasks should be segregated to: • 1. Separate transaction authorization from transaction processing. • 2. Separate record keeping from asset custody. • 3. Divide transaction-processing tasks among individuals such that short of collusion • between two or more individuals fraud would not be possible.
The Distributed Data Processing • An alternative to the centralized model is the concept of distributed data processing (DDP). The topic of DDP is quite broad, touching upon such related topics as end-user computing, commercial software, networking, and office automation. • Simply stated, DDP involves reorganizing the central IT function into small IT units that are placed under the control of end users.
Risks Associated with DDP • Inefficient use of Resources • risk of mismanagement of organization-wide IT resources by end users • risk of operational inefficiencies because of redundant tasks being performed within the end-user committee • risk of incompatible hardware and software among end-user functions
2. Destruction of Audit Trails 3. Inadequate Segregation of Duties 4. Difficulty in Hiring Qualified Personnel 5. Lack of Standards
Advantages of DDP • Cost Control • Improved Cost Control Responsibility • Improved User Satisfaction • Backup Flexibility
Controlling the DDP Environment Implement a Corporate IT Function • Central Testing of Commercial Hardware and Software • User Services • Standard-setting body • Personnel Review
Audit Objective The auditor’s objective is to verify that the structure of the IT function is such that individuals in incompatible areas are segregated in accordance with the level of potential risk and in a manner that promotes a working environment. This is an environment in which formal, rather than casual, relationships need to exist between incompatible tasks.
Audit Procedures If a company uses Centralized IT Function • Review relevant documentation, including the current organizational chart, mission statement, and job descriptions for key functions, to determine if individuals or groups are performing incompatible functions. • Review systems documentation and maintenance records for a sample of applications. Verify that maintenance programmers assigned to specific projects are not also the original design programmers.
• Verify that computer operators do not have access to the operational details of a system’s internal logic. Systems documentation, such as systems flowcharts, logic flowcharts, and program code listings, should not be part of the operation’s documentation set. • Through observation, determine that segregation policy is being followed in practice. Review operations room access logs to determine whether programmers enter the facility for reasons other than system failures.
If DDP is used: • Review the current organizational chart, mission statement, and job descriptions for key functions to determine if individuals or groups are performing incompatible duties. • Verify that corporate policies and standards for systems design, documentation, and hardware and software acquisition are published and provided to distributed IT units.
Verify that compensating controls, such as supervision and management monitoring, are employed when segregation of incompatible duties is economically infeasible. • Review systems documentation to verify that applications, procedures, and databases are designed and functioning in accordance with corporate standards.
THE COMPUTER CENTER • Accountants routinely examine the physical environment of the computer center as part of their annual audit. The objective of this section is to present computer center risks and the controls that help to mitigate risk and create a secure environment.
Physical Location • The physical location of the computer center directly affects the risk of destruction to a natural or man-made disaster. To the extent possible, the computer center should be away from human-made and natural hazards, such as processing plants, gas and water mains, airports, high-crime areas, flood plains, and geological faults. The center should be away from normal traffic, such as the top floor of a building or in a separate, self-contained building. Locating a computer in the basement building increases its risk to floods.
Construction • Ideally, a computer center should be located in a single-story building of solid construction with controlled access (discussed next). Utility (power and telephone) lines should be underground. The building windows should not open and an air filtration system should be in place that is capable of extracting pollens, dust, and dust mites.
Access • Access to the computer center should be limited to the operators and other employees who work there. Physical controls, such as locked doors, should be employed to limit access to the center. Access should be controlled by a keypad or swipe card, though fire exits with alarms are necessary. To achieve a higher level of security, access should be monitored by closed-circuit cameras and video recording systems.
Air Conditioning • Computers function best in an air-conditioned environment, and providing adequate air conditioning is often a requirement of the vendor’s warranty. Computers operate best in a temperature range of 70 to 75 degrees Fahrenheit and a relative humidity of 50 percent. Logic errors can occur in computer hardware when temperatures depart significantly from this optimal range.
Fire Suppression • Fire is the most serious threat to a firm’s computer equipment. Many companies that suffer computer center fires go out of business because of the loss of critical records, such as accounts receivable. The implementation of an effective fire suppression system requires consultation with specialists.
Fault Tolerance • Fault tolerance is the ability of the system to continue operation when part of the system fails because of hardware failure, application program error, or operator error.
1. Redundant arrays of independent disks (RAID). Raid involves using parallel disks that contain redundant elements of data and applications. If one disk fails, the lost data are automatically reconstructed from the redundant components stored on the other disks.
2. Uninterruptible power supplies. Commercially provided electrical power presents several problems that can disrupt the computer center operations, including total power failures, brownouts, power fluctuations, and frequency variations. The equipment used to control these problems includes voltage regulators, surge protectors, generators, and backup batteries.
Audit Objectives The auditor must verify that: • Physical security controls are adequate to reasonably protect the organization from physical exposures • Insurance coverage on equipment is adequate to compensate the organization for the destruction of, or damage to, its computer center
Audit Procedures • Test of Physical Construction • Test of Fire Detection System • Test of Access Control • Rest of RAID • Test of Uninterruptible Power Supply • Test of Insurance Coverage
DISASTER RECOVERY PLANNING • Disasters such as earthquakes, floods, sabotage, and even power failures can be catastrophic to an organization’s computer center and information systems. Disasters may be natural, human-made or system failure.
Features of a DRP • 1. Identify critical applications • 2. Create a disaster recovery team • 3. Provide site backup • 4. Specify backup and off-site storage procedures
Identify Critical Applications • The first essential element of a DRP is to identify the firm’s critical applications and associated data files. Recovery efforts must concentrate on restoring those applications that are critical to the short-term survival of the organization.
Create a Disaster Recovery Team • Recovering from a disaster depends on timely corrective action. Delays in performing essential tasks prolongs the recovery period and diminishes the prospects for a successful recovery. To avoid serious omissions or duplication of effort during implementation of the contingency plan, task responsibility must be clearly defined and communicated to the personnel involved.
Provide Site Backup • A necessary ingredient in a DRP is that it provides for duplicate data processing facilities following a disaster. Among the options available the most common are mutual aid pact; empty shell or cold site; recovery operations center or hot site; and internally provided backup.
Mutual Aid Pact. A mutual aid pact is an agreement between two or more organizations (with compatible computer facilities) to aid each other with their data processing needs in the event of a disaster.