Quantum Lower Bounds The Polynomial and Adversary Methods
200 likes | 355 Vues
This presentation by Scott Aaronson explores quantum computing's capabilities and limitations, focusing on lower bounds through Polynomial and Adversary methods. Quantum computing relies on quantum mechanics principles and challenges such as demonstrating if quantum computers can solve NP problems in polynomial time. It discusses foundational concepts like the Quantum Model, unitary evolution, and key methodologies to establish decision problem sizes in computational theory. Emphasizing successes and challenges, the talk analyzes the intersection of classical and quantum computational paradigms.

Quantum Lower Bounds The Polynomial and Adversary Methods
E N D
Presentation Transcript
Quantum Lower BoundsThe Polynomial and Adversary Methods Scott Aaronson September 14, 2001 Prelim Exam Talk
Motivation • Quantum computing: model of computation based on our best-confirmed physical theory • To understand quantum computing, must know limitations as well as capabilities • E.g., can QC’s decide NP in polynomial time? • Smart money says no, but proving it implies PNP • Popular alternative: study restricted models
Talk Overview • Intro to Quantum Model • Polynomial Method (Beals et al. 1998) • N lower bound for search • Part of D(f)1/6 bound for total functions • Adversary Method (Ambainis 2000) • Density matrices and entanglement • N lower bound for search (again)
The Quantum Model • State of computer: superposition over binary strings • To each string Y, associate complex amplitudeY • Y |Y|2 = 1 • On measuring, see Y with probability |Y|2 • Dirac ket notation: State written | = Y Y |Y • Each |Y is called a basis state
Unitary Evolution • Quantum state changes by multiplying amplitude vector with unitary matrix: |(t+1)= U|(t) • U is unitary iff U-1=U†,† conjugate transpose (Linear transformation that preserves norm=1) • Example: • Circuit model: U must be efficiently computable Black-box model: No such restriction (|0+ |1)/2 = |1
Query Model • Algorithm state is i,z,ai,z,a|i,z,a (i: index to query z: workspace a: answer bit) • Input: X=x1…xn {0,1}n • Query replaces each |i,z,a by (-1)x[i]|i,z,a • Algorithm alternates unitaries and queries: U0 O1 U1 … UT-1 OT UT • Ui are arbitrary, but independent of input • By end, i,z|i,z,f(X)|2 2/3 for every X
Lower Bounds by PolynomialsBeals, Buhrman, Cleve, Mosca, de Wolf, FOCS 1998 Key Idea • Let Q2(f) = minimum no. of queries used by quantum alg that evaluates f:{0,1}n{0,1} w.p. 2/3 for all X=x1…xn {0,1}n • If quantum algorithm makes T queries, acceptance probability is degree-2T polynomial over input bits • Implies Q2(f) ~deg(f)/2, where ~deg(f) = min degree of polynomial p s.t. |p(X)–f(X)| 1/3 for all X • Show ~deg(f) is large for function f of interest
Lemma: Q2(f) ~deg(f)/2. • Proof: After T queries, amplitude i,z,a of basis state |i,z,a is a complex-valued multilinear polynomial of degree T over x1,…,xn. By induction. • Base case: Before any queries, i,z,a is degree-0 polynomial. • Query: Replaces each i,z,a by (1-2xi)i,z,a. Increases degree by 1. Since xi{0,1}, can replace xi xi by xi. • Unitary: Replaces each i,z,a by linear combination of i’,z’,a’. So degree doesn’t increase. • Separating real and imaginary parts, i,z|i,z,f(X)|2 is a real-valued multilinear polynomial of degree 2T.
Lemma (Minsky, Papert 1968): If p: RnR is a multilinear polynomial, there’s a polynomial q: RR s.t. • deg(q) deg(p), • q(|X|) = psym(X) = (1/n!) S(n)p((X)) • (|X|: Hamming weight of X S(n): Symmetric group) • Proof: Let d = deg(psym) deg(p). Let Vj = sum of all products of j distinct variables. Since psym is symmetrical, • psym(X) = a0 + a1V1 + … + adVd • for some aiR. Vj assumes value • choose(|X|,j) = |X|(|X|-1)(|X|-2)…(|X|-j+1)/j! • on X, which is a polynomial of degree j of |X|. So construct q(|X|) of degree d accordingly.
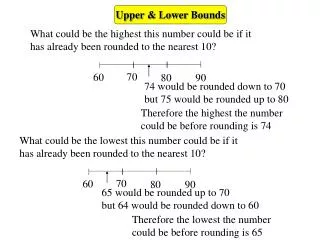
Approximate Degree of OR Theorem (Ehlich, Zeller 1964; Rivlin, Cheney 1966): Let p: RR be a polynomial s.t. b1 p(i) b2 for every integer 0 i n and |dp(x)/dx| c for some real 0 x n. Then deg(p) [cn / (c + b2 – b1)]. Corollary (Nisan, Szegedy 1994): ~deg(ORn) = (n). Proof: Let r: RR be symmetrization of approximating polynomial for ORn. Then 0 r(i) 1 for every integer 0 i n, and dr(x)/dx 1/3 for some x [0,1] because r(0) 1/3 and r(1) 2/3. So deg(r) [n/3 / (1/3 + 1 – 0)].
Definitions: C(f) and bs(f) For total Boolean function f and input X: XB = X with variables in set B flipped Certificate complexity CX(f) = Minimum size of set A s.t. f(X) = f(XB) for all B disjoint from A C(f) = maxX CX(f) Block sensitivity bsX(f) = Maximum number of disjoint sets B s.t. f(X) f(XB) bs(f) = maxX bsX(f) Immediate: bs(f) C(f) D(f), D(f) deterministic query complexity
Bound for Total Boolean Functions • Theorem (Beals et al.): D(f) = O(Q2(f)6) for all total f. • Proof overview: • bs(f) = O(Q2(f)2). Follows easily from n lower bound for ORn. • C(f) bs(f)2. Proved on next slide. • D(f) C(f) bs(f). Proof omitted. Idea: To evaluate f, repeatedly query a 1-certificate consistent with everything queried so far. Need to repeat at most bs(f) times.
Lemma (Nisan 1991): C(f) bs(f)2. • Proof: Let X {0,1}n be input, B1,…,Bb be disjoint minimal blocks s.t. b = bsX(f) bs(f). Claim: C = iBi {0,1}, variables set according to X, is a certificate for X of size bs(f)2. • If C were not a certificate, let X’ be input that agrees with C s.t. f(X’) f(X). Let X’ = XB. Then B is a sensitive block for X disjoint from iBi, contradiction. • For each 1 i b, |Bi| bs(f). For if we flip a Bi-variable in XB[i], function value must flip from f(XB[i]) to f(X), otherwise Bi wouldn’t be minimal. So every singleton in Bi is a sensitive block for f on XB[i]. Hence size of C is bs(f) bs(f). • (Is lemma tight? Open problem!)
Quantum Adversary MethodAmbainis, STOC’2000, to appear in JCSS • Key Idea • Give algorithm superposition of inputs • Consider (I=inputs, A=algorithm) as bipartite quantum state. • Initially I and A are unentangled. By end of computation, they must be highly entangled. • Upper-bound how much entanglement can increase via a single query. • How? Density matrices.
Density Matrices • Mixed state: distribution over quantum states • I.e., one part of composite state • (Not mixed: pure) • Non-unique decomposition into pure states: • |0 w.p. ½, |1 w.p. ½ • = (|0+|1)/2 w.p. ½, (|0-|1)/2 w.p. ½ • Density matrix: = ipi|ii| • where || has (i,j) entry i*j • represents all measurable information
Entanglement • Quantum state is entangled if not a mixture of product states (States for which measuring one subsystem reveals nothing about other subsystems) • Examples: ½(|00+|01+|10+|11): unentangled |00 w.p. ½, |11 w.p. ½: unentangled (|00+|11)/2: entangled (EPR pair)
Plan of Attack • Input:(1/|S|) XS|X • t = i,z,a pt,i,z,a|t,i,z,at,i,z,a| after t queries • Initially: input and algorithm unentangled 0 is pure state (0)XY = 1/|S| for all X,Y • By end: highly entangled T highly mixed |(T)XY|1/(3|S|) (say) for all X,Y with f(X)f(Y) • Goal: Upper-bound At = X,Y:f(X)f(Y) (|(t-1)XY|-|(t)XY|)
Lemma: For all X,Y with f(X)f(Y), |(0)XY|-|(T)XY| = (1/|S|). Proof: Let i,z,a i,z,a|i,z,a, i,z,a i,z,a|i,z,a be final algorithm states on X and Y respectively. Then (T)XY = (1/|S|) i,z,a i,z,a* i,z,a (1/|S|) [i,z,a|i,z,a|2] [i,z,a|i,z,a|2] (by Cauchy-Schwarz) (1/|S|) { [i,z|i,z,0|2] [i,z|i,z,0|2] + [i,z|i,z,1|2] [i,z|i,z,1|2] } (2/|S|)[(1- )], where is error prob.
Theorem: Q2(ORn) = (n). Proof: Let S contain all X{0,1}n of Hamming wt 1. A0=n-1 and ATn/2 (say); we show At-1-At = O(n). At-1-At X,Y:f(X)f(Y) |()XY-(’)XY| (=t-1, ’=t) i,z,api,z,aX,Y:f(X)f(Y) |(i,z,a)XY-(’i,z,a)XY|. Now (i,z,a)XY = i,z,a,X*i,z,a,Y, since i,z,a is a pure state. A query maps i,z,a,X to (-1)x[i]i,z,a,X, (i,z,a)XY to (-1)x[i]+y[i](i,z,a)XY. And for all X,Y, x[i]y[i] for only two values of i, so only four rows/columns change. So At-1-At 8 maxY X |i,z,a,X*i,z,a,Y| 8 X |i,z,a,X| = O(n) by Cauchy-Schwarz.
Game-Tree Search • For some problems, adversary method yields better bound than polynomial method • I.e. AND of n OR’s of n vars each • Upper bound: recursive Grover, O(n log n) • bs(f) = O(Q2(f)2) yields only Q2(f) = (4n) • Adversary method:Q2(f) = (n) • Idea: each XS can be changed in n places to produce Y s.t. f(X)f(Y), YS.