Information Flow Control
Information Flow Control. Nick Feamster CS 6262 Spring 2009. Lattice-Based Models. Denning's axioms Bell-LaPadula model (BLP) Biba model. Denning’s Lattice Model. SC set of security classes SC X SC flow relation (i.e., can-flow) SC X SC -> SC class-combining operator.

Information Flow Control
E N D
Presentation Transcript
Information Flow Control Nick FeamsterCS 6262Spring 2009
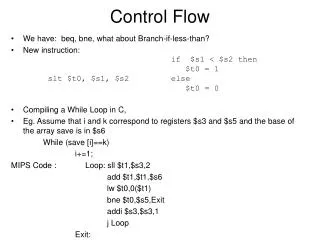
Lattice-Based Models • Denning's axioms • Bell-LaPadula model (BLP) • Biba model
Denning’s Lattice Model SC set of security classes SC X SC flow relation (i.e., can-flow) SC X SC -> SC class-combining operator < SC, , >
Denning’s Axioms • SC is finite • is a partial order on SC • SC has a lower bound L such that L A for all A SC • is a least upper bound (lub) operator on SC < SC, , >
Implications • SC is a universally bounded lattice • there exists a Greatest Lower Bound (glb) operator (also called meet) • there exists a highest security class H
Lattice Structures reflexive and transitive edges are implied but not shown Hierarchical Classes Top Secret Secret Confidential Unclassified can-flow
Lattice Structures Top Secret Secret Confidential Unclassified dominance can-flow
Lattice Structures Compartments and Categories {ARMY, CRYPTO} {ARMY } {CRYPTO} {}
Lattices Structures Compartments and Categories {ARMY, NUCLEAR, CRYPTO} {NUCLEAR, CRYPTO} {ARMY, NUCLEAR} {ARMY, CRYPTO} {NUCLEAR} {CRYPTO} {ARMY} {}
Lattice Structures Hierarchical Classes with Compartments {A,B} TS {B} {A} {} S product of 2 lattices is a lattice
Challenges • Implicit information flow • Conditional statements can implicitly leak information • Implementing a system that explicitly controls the flow of information
Static Binding: Run-Time • Objects are statically bound to classes • Can operate either at runtime, or at compile-time • Run-time mechanisms • Each process has a mechanism that specifies the highest class p can write from and the lowest class p can write to
Static Binding: Compile-Time • Certify program at compile-time • Advantages • Security guarantees before execution • Does not affect the execution speed • Disadvantages • Flows not specified by the program cannot be verified • Hardware could malfunction
Dynamic Binding • Objects can dynamically change their classification • One approach: Update the class of an object whenever data flows into it • Nondecreasing class mechanisms • Main problem: requires explicit flow to update the class of an object
Possible Applications • Confinement • No leaking information about confidential processes • Databases • Control information flow for different classes of information in the database • Decoupling right of access from right of control
Motivation • Malicious software sneaks onto computers • Collects users’ private information • Causes havoc on Internet • Slows performance • Costs to remove • Reputable vendors violate users’ privacy • Google Desktop • Sony Media Player
Traditional Malware detection • Signature-based • Cannot detect new malware or variants • Heuristics • High false positives • High false negatives
Panorama Approach • Input • Suspicious behavior • Inappropriate data access, stealthfully • Process • Whole-system, fine-grained taint tracking • Marking data • Operating-system-aware taint analysis • What touches the tainted data and how • Output • Taint Graphs • Tracked tainted data
Taint Graph • Information flow that shows the process that accessed the tainted data • Make policies based on Taint Graph • Compare unknown samples against Taint Graph • Automatic • Numerous categories
Taint Graph generation • Similar to a mapped out logic/process tree • Conceptually, horizontal branching • 9 different types of Root taint sources • Text, password, http, https, icmp, ftp, document, and directory • Non-root entries can be • OS objects (processes, modules) • OS resource (such as a file)
Conceptual Structure • Works with closed code • Windows OS • FireFox • Monitors the whole system in a processor emulator • Shadow memory stores taint status of • Each byte of physical memory • CPU’s general purpose registers • Hard disk and network interface buffer
Taint Sources • Test information is inputted and marked as taint source • Inputted from hardware such as • Keyboard • Network interface • Hard disk • Tainting at hardware level • Malware could hook before input reaches the software
Taint Propagation • Monitors CPU instructions and DMA operations dealing with tainted data • OS-Aware taint tracking • Developed a kernel module • Authenticated communications to taint engine
OS-Aware Taint Tracking • Resolving process and module information • Which process does an operation come from? • Module notifier • Tampering? • Mapping file and network information to taints • File system forensics • Mapping connections back to processes
Code Identification • Identifying the code under analysis and its actions • Entire code segment is labeled • Dynamic or Encrypted code is labeled too • A similar method labels trusted code • What does the analysis do about various derivatives of the code • Dynamic generation • Calling trusted code
Three Categorized Behaviors • Anomalous information access • MS Paint accessing passwords • Anomalous information leakage • BHO reporting home about surfed websites • Excessive information access • Repeatedly accessed directory to hide rootkit
Malware detections • 42 real-world malware samples • 56 benign applications were tested • Only 3 false positives, no false negatives • 2 from a personal firewall • 1 from a browser accelerator
Summary • A new system to detect malware • System-Wide Information Flow • Taint tracking • Data access and process tracking • Taint graphs • Policies
Contributions • Unified approach to detect and analyze diverse malware • Designed and developed a functional prototype • Detected all malware samples • Keystroke loggers, password sniffers, packet sniffers, stealth backdoors, rootkits, and spyware
Weaknesses • Performance Overhead • Using Cygwin utilities • Prototype is not optimized • Slowdown average is 20 times • Intended as a offline tool • Evasive malware • Time bombs • Selective keystroke loggers • Virtual environment detection
How to Improve • Optimize the code • Automate taint graph analysis and policy implementation • Virtual environment shielding • Or switch out of emulated environment • Implement mentioned improvements • Unicode conversion- switch case issue