W i reless LAN Security
220 likes | 367 Vues
W i reless LAN Security. Presented by: Pallavi Priyadarshini Student ID 003503527. Agenda. Brief background on Wireless LAN Basic security mechanisms in 802.11 WEP Vulnerabilities Enhancing wireless security with WPA Comparing WEP and WPA Conclusion. Brief Background.

W i reless LAN Security
E N D
Presentation Transcript
Wireless LAN Security Presented by: Pallavi Priyadarshini Student ID 003503527
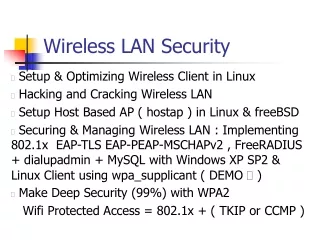
Agenda • Brief background on Wireless LAN • Basic security mechanisms in 802.11 • WEP Vulnerabilities • Enhancing wireless security with WPA • Comparing WEP and WPA • Conclusion
Brief Background • A local area network (LAN) with no wires • Several Wireless LAN (WLAN) standards • 802.11 - 1-2 Mbps speed, 2.4Ghz band • 802.11b (Wi-Fi) – 11 Mbps speed, 2.4Ghz band • 802.11a (Wi-Fi) - 54 Mbps speed, 5Ghz band • 802.11g (Wi-Fi) – 54 Mbps speed, 2.4Ghz band
Security Challenges and Solutions • Challenges • Beyond any physical boundaries • Encryption, Authentication and Integrity • Basic Security Mechanisms in 802.11 • Service Set ID (SSID) – Acts like a shared secret, but sent in clear. • MAC Address Lists – Modifiable and also sent in clear. • The WEP Algorithm
More on WEP • Stands for Wired Equivalent Privacy • Designed to encrypt data over radio waves • Provides 3 critical pieces of security • Confidentiality (Encryption) • Authentication • Integrity • Uses RC4 encryption algorithm • Symmetric key stream cipher • 64-bit shared RC4 keys, 40-bit WEP key, 24-bit plaintext Initialization Vector (IV)
IV IV Key Sequence Seed PRNG XOR Ciphertext Secret Key Integrity Check value CRC-32 Algorithm Plaintext Plaintext WEP Encryption and Integrity Message Data payload PRNG – RC4 Pseudorandom number generation algorithm
WEP Authentication • 2 levels of authentication • “Open” : No authentication • “Shared secret” : Request for shared key auth. Station B Station A Nonce N E(N, KA-B) Authentication response
WEP – The “flawed” Solution • Weakness in key management • Single key for all access points and client radios • Static unless manually changed • Authentication and encryption keys are the same • Shared key authentication failure • No knowledge of secret to gain network access • WEPPR=C P (where C, P are passively recorded) Authentication request Attacker Challenge R AP WEPPR R Success
WEP – The “flawed” Solution (contd.) • Weakness in Encryption • Short 24-bit IV, reuse mandatory • Weak per-packet key derivation - exposes RC4 protocol to weak key attacks. Given c1 and c2 with same IV, c1 c2= p1p2 [p1 S p2 S], leading to statistical attacks to recover plaintexts • Short 40-bit encryption scheme • No forgery protection • Using CRC-32 checksum possible to recompute matching ICV for changed data bits • Given C= RC4(IV, key) <M, ICV(M)>, can find C’ that decrypts to M’=M+Δ such that C’= RC4(IV, key) <M’, ICV(M’)>
WEP – The “flawed” Solution (contd.) • No protection against replays • Optional, mostly not turned on by users
Design Constraints • WEP patches will rely entirely on software upgrade • Access points have little spare CPU capacity for new functions • Encryption functions are hard-wired in the access points
Enhancing WLAN Security with WPA • WPA - Wireless Protected Access • Strong, standards based, interoperable security for Wi-Fi • Addresses all known weaknesses of WEP • Subset of forthcoming IEEE 802.11i standard • Designed to run as a software upgrade on most Wi-Fi certified products.
Security Mechanisms in WPA - TKIP • Uses TKIP (Temporal Key Integrity Protocol) Encryption. • Suite of algorithms wrapping WEP • Adds 4 new algorithms to WEP: • New cryptographic message integrity code (MIC) called Michael - to defeat forgeries • New IV sequencing discipline - to remove replay attacks • A re-keying mechanism – to provide fresh encryption and integrity keys
More on TKIP • A per-packet key mixing function • Phase 1 (Eliminates same key use by all links) - Combines MAC address and temporal key. Input to S-box to produce intermediate key • Phase 2 (De-correlates IVs and per-packet keys) - Packet sequence number encrypted under the intermediate key using a fiestel cipher to produce 128-bit per packet key. • TKIP leverages 802.1X/EAP framework for key management
802.1X/EAP Architecture Supplicant (wireless client) Authenticator (AP) Authentication Server (RADIUS) EAP-start EAP-identity request EAP-identity response EAP success/reject EAP success/reject
WPA Modes of Operation - Pre-shared key vs. Enterprise • Pre-shared Key Mode for home/SOHO users • Does not require authentication server • “Shared Secret” or password entered manually in the AP and wireless client. • WPA takes over automatically. • Only the clients with matching passwords are allowed to join the network. • The password automatically kicks off the TKIP encryption process. • Enterprise Mode for corporate users • Requires an authentication server like RADIUS • Centralized management of user credentials
Access Point Internet Authentication server WPA modes of operation – Enterprise Mode Wired Network Services
Conclusion • WPA is not an ideal security protocol design… • However, it is a dramatic improvement in Wi-Fi security. • Has not been broken (yet). • Protects the original hardware investment. • If hardware constraint removed, a more robust security solution possible. • Such a solution is being developed based on a even stronger cryptographic cipher - Advanced Encryption Standard (AES).
References [1] Bruce Potter & Bob Fleck, “802.11 Security”, O-Reilly, December 2002 [2]James larocca & Ruth larocca, “802.11 Demystified”, McGraw-Hill Telecom, 2002 [3]Whitepaper on Wireless LAN Security on http://www.wi-fi.org [4]http://www.ieee802.org/1/pages/802.1x.html