Securing the Wireless LAN
Securing the Wireless LAN. George Ou Network Systems Architect Contributing editor – ZDNet. Contents. Introduction Relative risks of Wireless LANs Six dumbest ways to secure a WLAN Tools of the wireless LAN hacker The best ways to secure the WLAN SOHO WLAN implementations

Securing the Wireless LAN
E N D
Presentation Transcript
Securing the Wireless LAN George Ou Network Systems Architect Contributing editor – ZDNet
Contents • Introduction • Relative risks of Wireless LANs • Six dumbest ways to secure a WLAN • Tools of the wireless LAN hacker • The best ways to secure the WLAN • SOHO WLAN implementations • Enterprise WLAN implementations
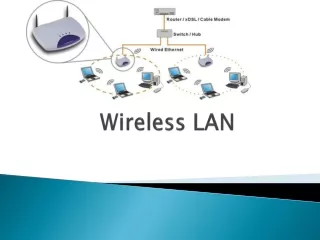
Introduction • Wireless security is a huge headache in IT • Wireless security widely misunderstood • Wireless security is everyone’s problem even if you don’t “think” you have a WLAN • Banning WLANs often result in “improvised” home grown solutions • Wireless LANs can be secured • Wireless security applicable elsewhere in IT
Relative risks of Wireless LANs • Wireless security is NOT an oxymoron • Less dangerous than having an Internet connection direct or indirect • Attacks from the Internet can come from anywhere on the entire globe • Web/FTP/Mail/DNS Servers • Back doors R00TK1T5 that can dial home • Attacks on Wireless LANs are limited to a couple of kilometers
Six dumbest ways to secure a WLANOverview • MAC “authentication” • SSID “hiding” • LEAP authentication • Disabling DHCP • Antenna placement and signal suppression • Switch to 802.11a or Bluetooth Wireless LANs ______________________________________ • Dishonorable mention: WEP Original article on http://blogs.zdnet.com/Ou
Six dumbest ways to secure a WLANMAC “authentication” • Use of the word “authentication” is laughable • All that’s happening is MAC address filtering • MAC addresses are transmitted in clear text • Extremely easy to capture • Extremely easy to clone and defeat • Extremely difficult to manage MAC filtering
Six dumbest ways to secure a WLANSSID “hiding” • No such thing as “hiding” an SSID • All that’s happening is Access Point beacon suppression • Four other SSID broadcasts not suppressed • Probe requests • Probe responses • Association requests • Re-association requests • SSIDs must be transmitted in clear text or else 802.11 cannot function
Six dumbest ways to secure a WLANLEAP authentication • Cisco LEAP authentication is extremely weak • LEAP successor EAP-FAST not much better • Cisco dominates Enterprise WLAN market • Significant percentage of Cisco shops use LEAP but have started to migrate to EAP-TLS • LEAP and EAP-FAST are free on client side • Only Cisco can sell LEAP and EAP-FAST on Access Points • Cisco APs support all open authentication standards like EAP-TLS and PEAP
Six dumbest ways to secure a WLANDisabling DHCP • Disabling DHCP and forcing the use of Static IP addresses is another common myth • IP schemes are easy to figure out since the IP addresses are sent over the air in clear text • Takes less than a minute to figure out an IP scheme and statically enter an IP address
Six dumbest ways to secure a WLANAntenna placement and signal suppression • Antenna placement and signal suppression does nothing to encrypt data • The hacker’s antenna is bigger than your’s • Directional high-gain antennas can pick up a weak signal from several kilometers away • Lowering the signal hurts legitimate users a lot more than it hurts the hackers • Wi-Fi paint or wall paper not 100% leak proof and very expensive to implement
Six dumbest ways to secure a WLANSwitch to 802.11a or Bluetooth wireless LANs • 802.11a is a transport mechanism similar to 802.11b or 802.11g • 802.11a has nothing to do with security • Pray that the hacker doesn’t have 5 GHz 802.11a capable equipment • Bluetooth is more of a wireless USB alternative • Can be used for wireless networking but not designed as an 802.11 a or b/g replacement
Six dumbest ways to secure a WLANDishonorable mention: WEP • WEP barely missed the six dumbest list because it can still hold up for a couple of minutes • Hacker named “KoreK” releases new WEP analysis tool in August 2004 • WEP coupled with 802.1x and EAP key rotation (AKA DWEP) is considered broken • Packet injection techniques lowers WEP cracking times to minutes Article: Next generation WEP cracking tools
Tools of the wireless LAN hackerOverview • Software • Auditor CD • Kismet • ASLEAP • Void11, Aireplay, Airedump, and Aircrack • Hardware • Cheap and compatible cardbus adapters • Omni directional high-gain antennas • Directional high-gain antennas • Off the shelf Laptop computer
Tools of the wireless LAN hackerAuditor CD • Bootable Linux CD with every security auditing tool under the sun • Everything needed to penetrate most wireless LAN and more • Mentioned as a favorite of the FBI • Relatively easy to use
Tools of the wireless LAN hackerKismet • Kismet is a Linux wireless LAN audit tool • Can see “hidden” SSIDs • Can see MAC addresses • Can see IP schemes • Can capture raw packet • GUI version lays everything out
Tools of the wireless LAN hackerASLEAP • ASLEAP cracks Cisco LEAP authentication • Exploits weak MSCHAPv2 authentication • Uses pre-computed indexed hash tables • Checks 45 million passwords a second • Upgraded to support PPTP VPN cracking
Tools of the wireless LAN hackerVoid11, Aireplay, Airedump, and Aircrack • New set of tools makes WEP cracking hundreds of times faster • Void11 forces users to re-authenticate • Aireplay monitors re-auth session for ARP and then plays back the ARP request to trigger responses from legitimate computers • Airedump captures all of the raw packets • Aircrack only needs 200,000 packets instead of 10,000,000 packets from previous tools
Tools of the wireless LAN hackerHardware: Cheap and compatible cardbus adapters • Prism 2/3 based 802.11b adapters • PrismGT based 802.11 b/g adapters • Atheros based 802.11 a/b/g adapters • All typically around $40 to $70 USD • All compatible with Linux cracking tools
Tools of the wireless LAN hackerOmni directional high-gain antennas • Typically 7 to 9 dB gain • General purpose surveying and war driving • Can be used to create evil twin access point • Less than $100 USD
Tools of the wireless LAN hackerDirectional high-gain antennas • Used to aim and focus in on victim • Picks up weak signals many kilometers away • Around $100 USD
Tools of the wireless LAN hackerOff the shelf Laptops • Any Laptop or PC can be used for hacking • New Laptops with good cracking speed are as low as $400 USD • Wireless hacking is NOT cost prohibitive!
The best ways to secure the WLANOverview • Good cryptography allows secure communications over unsecured medium • Follow best practice cryptographic principles • Strong authentication • Strong encryption • WPA and WPA2 standards
The best ways to secure the WLANStrong authentication background • Strong authentication is often overlooked • Well established secure authentication methods all use SSL or TLS tunnels • TLS is the successor of SSL • SSL has been used for nearly a decade in E-Commerce • SSL or TLS requires Digital Certificates • Digital Certificates usually involves some form of PKI and Certificate management
The best ways to secure the WLANStrong authentication in Wireless LANs • Wireless LANs typically use 802.1x and EAP • Common standard EAP types are EAP-TLS, EAP-TTLS and PEAP • LEAP and EAP-FAST are not standard • EAP-TLS requires server and client certificates • EAP-TTLS and PEAP only require client-side certificates • EAP-TTLS created by Funk and Certicom • PEAP created by Microsoft, Cisco and RSA Details on EAP types at: http://blogs.zdnet.com/Ou/?p=67
The best ways to secure the WLANStrong authentication and RADIUS servers • EAP authentication requires RADIUS support in Access Point and one or more RADIUS servers • Microsoft Windows 2003 Server has fully functional RADIUS component called IAS • Supports EAP-TLS and PEAP • Windows 2000 only supports EAP-TLS • Easily integrates in to NT domains or Active Directory • Funk software makes Steelbelted and Odyssey • Open source FreeRadius supports broad range of EAP types
The best ways to secure the WLANStrong encryption • Encryption is well understood • No known methods of breaking good encryption • DES encryption has never been crypto-analyzed in nearly 30 years and must be brute forced • 3DES still considered solid but slow • AES is the official successor to DES and is solid at 128, 192, or 256 bits
The best ways to secure the WLANStrong encryption in Wireless LANs • RC4 encryption is known to be weak • WEP uses a form of RC4 encryption • Dynamic WEP makes WEP cracking harder • TKIP is a rewritten WEP algorithm • No known methods against TKIP yet but some theoretical attacks are on the horizon • AES encryption mandated in the newest Wireless LAN standards is rock solid
The best ways to secure the WLANWPA and WPA2 standards • WPA used a trimmed down version of 802.11i • WPA2 uses the ratified 802.11i standard • WPA and WPA2 certified EAP types • EAP-TLS (first certified EAP type) • EAP-TTLS • PEAPv0/EAP-MSCHAPv2 (Commonly known as PEAP) • PEAPv1/EAP-GTC • EAP-SIM • WPA requires TKIP capability with AES optional • WPA2 requires both TKIP and AES capability Details on EAP types at: http://blogs.zdnet.com/Ou/?p=67
SOHO WLAN implementations • Minimum encryption should be TKIP • Run AES encryption if possible • EAP authentication usually not feasible for Small offices and home offices • SOHO WLANs usually rely on WPA-PSK • PSK (pre-shared keys) are easier than WEP with 26 HEX digits • PSK must be at least 8 alphanumeric random characters • Zyxel offers Access Points with PEAP RADIUS built-in
Enterprise WLAN implementationsWPA and WPA2 standards • Minimum encryption should be TKIP • Run AES encryption if possible • EAP-TLS authentication recommended • PEAP or EAP-TTLS authentication at a minimum
Enterprise WLAN implementationsWireless Switches • Wireless LAN switches manage large numbers of Access Points • Much easier to manage • Wireless switch makers • Symbol • Cisco Airespace • Aruba
Enterprise WLAN implementationsAdvanced security implementations • Multiple Virtual SSID and VLAN support • VLAN assignment based on group membership • Guest Wireless LANs that are isolated • Mitigating WEP security risks for WEP only devices using Firewall or Router ACLs (Access Control Lists) • Can be done with single device such as the Cisco 851W which is a Firewall, Router, Managed Switch, and Access Point all-in-one