SMART CARDS
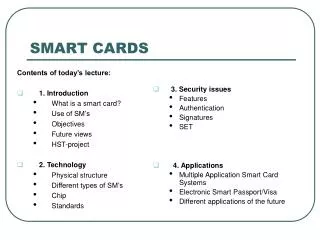
Contents of today’s lecture: 1. Introduction What is a smart card? Use of SM’s Objectives Future views HST-project 2. Technology Physical structure Different types of SM’s Chip Standards. 3. Security issues Features Authentication Signatures SET 4. Applications


SMART CARDS
E N D
Presentation Transcript
Contents of today’s lecture: 1. Introduction What is a smart card? Use of SM’s Objectives Future views HST-project 2. Technology Physical structure Different types of SM’s Chip Standards 3. Security issues Features Authentication Signatures SET 4. Applications Multiple Application Smart Card Systems Electronic Smart Passport/Visa Different applications of the future SMART CARDS
Introduction to smart cards- What is a smart card? • A credit card-sized plastic token with an embedded microchip (integrated circuit chip) • Provides • Persistent, protected storage • Memory capacity (4K - 32K is typical) • Computational capability and Processing power (a small CPU) • Self-contained Doesn’t need to depend on potentially vulnerable external resources • Today, smart cards are used by millions of cardholders worldwide and are at work in more than 90 countries, primarily in Europe and the Far East, processing point-of-sale transactions, managing records, and protecting computers and secure facilities.
SMART…? Usage of smart cards • In different applications which require strong security protection and authentication • Identification card • Medical card • Credit/debit bank card (as an electric wallet) • All require sensitive data to be stored on the card, such as: • biometrics information • personal medical history • cryptographic keys for authentication • Logging on to networks • Wirelessly: • Public transport payments (tickets) etc.
Objectives • Accelerate and harmonize the development and the use of sm’s • Interoperability: - Build a consensus for system interoperability - Harmonize smart cards based infrastructures across sectors • Multi-application cards: - Advance smart card technology for seamless use of multi-application cards. - Contribute to the development of innovative applications and services. • Security of transactions: - Agree on common protection profiles and specifications. - Develop certification services and cryptography support. • User Acceptance of Smart cards • Accessibility
Interoperability • different cards are usually not interchangeable • Memory cards usually have different interface characteristics from microprocessor cards: • different data formats and/or electrical signals across the interface between card and terminal • provide the different mixes of applications that various types of cardholder will want (BUT: rarely accepted at the moment) • A rare example of an attempt at interoperability: The UK EMV bank debit/credit card scheme demands interchangeability from its various suppliers - and gets it at the level at which the cards are used by the cardholder.
Future views “Smart cards are the keys to the media and information revolution no matter whether it is wired or wireless” • magnetic strip card will be replaced and integrated together into a multi-application card • Usebecomes daily • Will be used to carry a lot of sensitive and critical data • issues about whether or not the smart card is secure and safe enough to store that information
HST-project (Finnish research in 1999) • A Governmental project in Finland to build national Public Key Infrastructure (PKI). • Key concept in HST is Electronic ID-card, smart card which contains users cryptographic keys and certificates. • With this card and other PKI components person can be digitally identified in Internet where he or she can use it for example to sign documents. • Card contains its own operating system, special RSA-processor, specific software and certificates. In the card there are two certificates and private keys: one for authentication and encryption, other one for digital signature. Certificates are protected with PIN-codes which are only known to the card owner. • More of this can be read at: http://www.tcm.hut.fi/Opinnot/Tik-110.401/1999/Tutkielmat/kolsi/HST.pdf
Technology • Physical structure • Different types of SM’s • Chip / Standards
Physical Structure • Made up of three elements • A physical card (plastic) • A printed circuit chip • An integrated circuit chip (microcontroller) (Chips are embedded on the card) • Printed circuit conforms to ISO standard 7816/3 which provides five connection points for power and data • The printed circuit protects the circuit chip from mechanical stress and static electricity • The capability of a smart card is defined by its integrated circuit chip. • Chip made from silicon which is not flexible and particularly easy to break • In general, the size, the thickness and bend requirements for the smart card are designed to protect the card from being spoiled physically
Different types of SM’s • Java cards • SIM cards • eCash cards • Contact / Contactless Smart Cards • Proximity cards • Hybrid/twin cards • Combi cards
CONTACT: Cards the size of a conventional credit or debit card with a single embedded integrated circuit chip that contains just memory or memory plus a microprocessor. Popular Uses:Network security, vending, meal plans, loyalty, electronic cash, government IDs, campus IDs, e-commerce, health cards CONTACTLESS: Cards containing an embedded antenna instead of contact padsattached to the chip for reading and writing information contained in the chip's memory. Popular Uses:Student identification, electronic passport, vending, parking, tolls, IDs Contact / Contactless Smart Cards
Proximity cardsHybrid/twin cardsCombi cards • "Prox cards" communicate through an antenna similar to contactless smart cards except that they are read-only. • Uses: Security, identification and access control • Cards containing two or more embedded chip technologies such as a prox chip with its antenna and a contact smart chip with its contact pads are Hybrid/twin cards. • Uses: Accommodates legacy system infrastructure while adding applications that require different e-card technologies • The combi card has one smart chip embedded in the card that can be accessed. This form of smart card is growing in popularity because it provides ease-of-use and high security in a single card product. • Uses: Mass transit and access control combined with other applications such as network security, vending, meal plans, loyalty, etc.
Java card • The Java Card specifications enable Java technology to run on smart cards and other devices with limited memory • Multi-Application Capable - Java Card technology enables multiple applications to co-exist securely on a single smart card • Dynamic: - New applications can be installed securely • Secure: - relies on the inherent security of the Java programming language to provide a secure execution environment. - platform's proven industry deployments and security evaluations ensure that card issuers benefit from the most capable and secure technology available today.
CHIP - What does the chip contain and what is it made for? • Made for the portable storage and retrieval of data • Used memory types: • ROM Read only memory (mask ROM) • PROM Programmable read only memory • EPROM Erasable programmable ROM • EEPROM Electrically erasable PROM • RAM Random access memory • Memory-only chips are functionally similar to a small floppy disk. • Chips that contain both memory and a microprocessor are also similar to a small floppy disk, except they contain an "intelligent" controller used to securely add, delete, change, and update information contained in memory.
Standards • The standardization of smart card systems is an ongoing process. One of the standards most referred to is the ISO-7816 standard. It is divided as follows: Part 1: Physical characteristics Part 2: Dimensions and location of the contacts Part 3: Electronic signals and transmission protocols Part 4: Industry commands for interchange Part 5: Number system and registration procedure for application identifiers Part 6: Interindustry data elements • Present projects: • Smart MEIJI is a joint project designed to reinforce co-operation between Europe and Japan in the field of smart cards
SECURITY ISSUES - Features - Authentication - Signatures - SET
Security features • An important aspect to smart cards to prevent unauthorized users from gaining access to information contained on the card. • The advantage smart cards have over magnetic stripe cards is that the smart card contains the computer chip which stores the password or PIN. • the password is not sent over a communication line to a computer system for verification, which can easily be tapped. • most important part of a smart card is the software that provide the applications • It has been established that any secure transaction involves 6 generic functions: • Data Protection • Identification of the cardholder • Mutual authentication • Secure writing • Certification or signature • Encryption • The security imposed to protect the transmission between the card and the outside world by the mean of cryptographic technique in order to control the: • writing operation • authentication the card or the terminal • origin of the message • transmission of cryptographic keys
Authentication • The most common method used for cardholder verification at present is to give the cardholder a PIN (Personal Identification Number) which he or she has to remember. • PINs can be stolen or abused. • The only truly effective method of Cardholder Verification is the measurement of a physiological characteristic unique to an individual and incapable of fraudulent replication or abuse. • Biometrics: • Iris and Retinal scans, • Face or Hand geometry, • DNA, • most acceptable attribute is the fingerprint.
Signatures • Electronic signatures in combination with a PKI. • Loaded with private key(s), public key certificates and some ways to point securely to non-repudiation policies • The loading procedure and the data formats need to be specified. • The use of standardized APIs to allow electronic signature enabled applications to interface with any kind of smart card is to be considered • Blind signatures allow privacy features to be built into applications. • Ecash, for instance, uses blind signatures to offer payer anonymity. • Privacy issues are certain to play an increasingly important role in the continuing development of digital signature applications.
SET (Secure Electronic Transaction) • When a purchase is made: - the user's credit card account information is verified as authentic to the vendor and then debited at the user's financial institution. - All transmissions of information are secure through the use of the SET (Secure Electronic Transaction) Protocol 1.0, developed by Visa and MasterCard, which encrypts all data during transmission.
APPLICATIONS • Application areas • Multiple Application Smart Card Systems • Different applications of today and the future
Applications • With advanced technologies special solutions for various applications have been created with smart cards, for example in the fields of: • Mobile telephony • Gaming and Wagering • Healthcare systems • Network security • Personnel access • Logistics management • Multiple basic application areas and industries in our daily lives
Multi-application sm’s • Most of the smart card systems in use today serve one purpose and are related to just one process: • smart telephone card • electronic money • medical card • electronic identification card • All of these applications are stored in different smart card systems separately require users to carry multiple cards for multiple applications • The smart card has the capability to integrate those applications together to form a multiple application card by utilizing its embedded microprocessor and memory storage spaces. • 3 different infrastructures of multiple application smart card systems
LAST SLIDE… Any questions ? Thank you for your time!
2. Security 2.1 Introduction 2.2 Life cycle of smart card 2.3 Logical Structure 2.4 Access Control
2.1 Introduction • What makes the smart card better than normal magnetic stripe card? • The advantage smart cards have over magnetic stripe cards is that the smart card contains the computer chip which stores the password or PIN • Therefore, the password is not sent over a communication line to a computer system for verification, which can easily be tapped.
2.2 Life cycle of smart card • Divided into five phases (on most smart cards) • These phases justified by • Limitation of transfer and access of data is incremental throughout different phases • Different areas of smart card protected throughout the life cycle
2.2.1 Fabrication phase • Carried out by the chip manufacturers • A Fabrication Key (KF) is added to protect the chip • unique and is derived from a master manufacturer key • Fabrication data will be written to the circuit chip
2.2.2 Pre-personalisation phase • Done by Card manufacturers • Chip will be mounted on the plastic card • The connection between the chip and the printed circuit will be made • Fabrication key (KF) changed to Personalisation key (KP) • Personalisation lock Vper • No further modification of the KF • Physical memory access instructions will be disabled • Access of the card can be done only by using logical memory addressing
2.2.3 Personalisation phase • Conducted by the card issuers • Data files contents and application data are written to the card • Information of card holder stored to the chip (PIN, Unlocking PIN) • Utilisation lock Vutil • No further modification of the KP
2.2.4 Utilisation phase • Phase for the card owners use of the card • Access of information on the card will be limited by the security policies set by the application
2.2.5 End-of-Life phase • Two ways: • 1. invalidation lock • All operations will be disabled (except read) • 2. Control system irreversibly blocks access • All operations will be disabled
2.2.6 Summary of life-cycle Table 1: Phases and access rights of smart card's life cycle(Source: Philips DX smart card reference manual, 1995)
2.3 Logical Structure • After a smart card is issued to the consumer, protection of the card will be controlled by the application operating system mainly • Access of data has to be done through the logical file structure on the card
2.3 Logical Structure (2) • A smart card can be viewed as a disk drive, including • master file (MF) (similar to root in e.g. MS-DOS) • dedicated files (DFs) (similar to normal folder) • elementary files (EFs) (similar to normal files)
2.3 Logical Structure (3) Figure 2: Logical file structure of smart card
2.3 Logical Structure (4) • In short, • the file structure of the smart card OS is similar to other common OS such as UNIX • However, it provides a greater security control • accessing conditions and file status field for each file header • file lock
2.4 Access Control • Each file attached with a header which indicates the access conditions • The fundamental principle of the access control is based on the correct presentation of PIN numbers • Primarily, the access conditions can be divided into five following non-hierarchical levels ->
2.4 Access Control (2) • Always (ALW) • no restrictions • Card holder verification 1 & 2 (CHV1 & 2) • Access granted if valid CHV presented • Administrative (ADM) • Allocation and administrative authority • Never (NEV) • Access always forbidden
2.4 Access Control (3) • PIN presentations: • PIN and unblocking PIN • Stored in separate elementary files (EF) • Access conditions prevent changes • Changes can be made by issuing old and new PIN • If both PINs fail, irreversible blockage will occur
3. Attacks 3.1 Introduction 3.2 Logical attacks 3.3 Physical attacks 3.4 Mathematical attacks 3.5 Conclusions
3.1 Introduction • Target of attacks: • The secret of the cryptographic algorithm • The keys stored • The access control • Information strored on card
3.2 Logical attacks • Starting point: • EEPROM (electrically erasable programmable read only memory) write operations can be affected by unusual voltages and temperatures -> • information can be trapped by raising or dropping the supplied voltage to the microcontroller
3.2 Logical attacks (2) • Example 1. Attack of PIC16C84 microcontroller • Erasing the memory by raising the voltage VCC (Supply voltage) to VPP (Programming voltage) - 0.5V
3.2 Logical attacks (3) • Example 2. Attack on DS5000 security processor • A short voltage drop can release the security lock without erasing the secret data sometimes
3.2 Logical attacks (4) • Example 3. Usage of analogue random generator • Creates cryptographic keys that will produce an output of almost all 1’s when the supply voltage is lowered slightly.
3.2 Logical attacks (5) • Prevention of logical attacks • some security processors implemented sensors which will cause an alarm when there is any environmental changes
3.3 Physical attacks • Invasive physical attacks • Reverse engineering of the circuit chips • erasing the security lock bit by focusing UV light on the EPROM • probing the operation of the circuit by using microprobing needles • using laser cutter microscopes to explore the chip
3.3 Physical attacks (2) • Example 1. Invasive physical attacks • Circuit chip removed from the plastic card • The resin dissolved • The acid and resin washed away >>>>> The chip can be examined and attacked directly (only for US $30)
3.3 Physical attacks (3) • Example 2. Attacking by reverse engineering circuit chips (High quality laboratory needed) • etching away a layer of a chip at a time • thin film of a metal attached to chip creating a diode -> filmed with electron beam • PCs image processing system software used to analyze the pictures The layout and function of the chip can then be identified