Smart Cards
Smart Cards Security & Applications Outline What is a smart card ? History & Contemporary Usage of Smart Cards. Types of Smart Cards Advantages Smart Card & System Components Biometrics Security Applications What is a Smart Card ? A plastic card which contains


Smart Cards
E N D
Presentation Transcript
Smart Cards Security & Applications
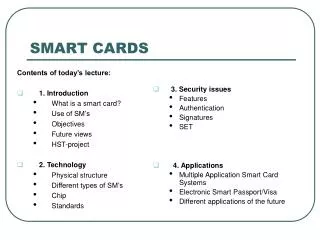
Outline • What is a smart card ? • History & Contemporary Usage of Smart Cards. • Types of Smart Cards • Advantages • Smart Card & System Components • Biometrics • Security • Applications
What is a Smart Card ? • A plastic card which contains • CPU, ROM, RAM, E2PROM • It has • I/O and processing capability. • Of 6-8 contacts, 6 connected to the chip. These are • Vcc, Vpp, Ground, Clock, Reset, Serial I/O.
History • Speculations about the first Smart card. • 1968 - The idea of using plastic cards as the carrier for microchips was developed by Jergen Dethloff. • 1970 - The first smart cards were introduced in Japan. • 1974 - First patent by Roland Morena. • 1979 - Motorola produced a smart card with a chip. • 1984 - Microchips on Visa debit cards in France. • 1990 - Philips offer 512 bit RSA signature in 1.5 sec. • 1993 - France mandated microchips on all bank cards.
History (cont’d) • 1995 - Korea issues 1.5 million contactless smart cards for public transportation. • 1996 - At the Atlanta Olympics, athletes, team members, and staffs were issued with contactless smart cards containing their identification number, biometrics, etc. • 1996 - SGS Thompson offers RSA in 60 ms. • 1997 - MS plans smart card login support for Win 98/NT 5.0.
Current Trends and Issues • Europe currently accounts for around 80% of the smart card market, with 16% in Asia, 3% in North America. • Several Asian countries have large smart card projects. • Even in North America around 5 million cards were issued in 1996. • 500 million cards in 1996, 2.5 billion in 2000. • Telephone cards is currently the largest application.
Current Trends and Issues (cont’d) Millions of Unit/Year
Manufacturers • Motorola - MSC0402 • ROM 23K • E2PROM 8K • RAM 384 Bytes • RNG • Hitachi- H8/300 • ROM 16K • E2PROM 8K • RAM 512 Bytes • 2 I/O ports • Others • Japan : NEC, Toshiba, Oki. • US : Texas Instruments, Atmel, Catalyst • SGS-Thompson (France), Philips (Netherlands), Siemens (Germany).
Not every Smart Card is Intelligent ! • Memory Cards contain a memory with a fixed logic that enables to read from and write to this memory. • Cards, that use microcomputer ICs, are more commonly known as Smart Cards or Chip Cards. • Chip Cards are active devices.
Types of Smart Cards • Contact Cards must be inserted into a reader • Contactless Cards powered by an RF signal using inductive coils. • Combi Cards can be powered by insertion or RF.
Advantages • Cannot be easily duplicated, • Tamper proof due to hardware technology, • Has processing power, • Incorporate cryptographic techniques, • Provide interactive authentication, • Flexible storage for biometrics, identification, • Organized information,
Advantages (cont’d) • Fraud reduction, • High memory capacity, • Paperless transactions, • Convenience.
Problems • Possible usage/registration fees, • Lack of internationally accepted standards, • Liability issues if card is lost/stolen/misused, • Downloading control, • System designers are not well informed about how to make use of the cryptographic products, • Inter-process protection in multi-application cards. • Contact/contactless cards.
Problems (cont’d) • The difficulty of single terminal accepting all cards due to many card issuers and schemes. • Because of patents it is difficult to enter smart card market especially for chip and card manufacturers. • Multi-functionality issues.
Inside the Smart Cards BUS CPU MEMORY CLOCK PROTECTION RESET I/O
Smart Card Components • Carrier - PVC, PETP. • Chip • Low-powerCMOS technology, operating at voltages between 2.2V and 5.5V: chips operating down to 1.5V and below are being designed. • 1 micron is now common, 0.2 micron is aimed • Microprocessor • 8 bit, Motorola 6805, Intel 8051 based. • Clock speed up to 5 MHz. • 16 bit processors are used in some newer chips.
Smart Card Components (cont’d) • Microprocessors (cont.) • RISC microcontrollers are available for smart cards • Coprocessors • Multiprecision arithmetic operations (multiplication and exponentiation). • DES encryption operations. • RSA or Elliptic Curve Signatures • Memory • ROM is used for storing the fixed program of the card, also known as its mask.
Smart Card Components (cont’d) • Memory (cont.) • PROM is used for loading a card’s serial numbers or other fixed values. (up to 32 Bytes) • Flash Memory is sometimes used for storing additional programs. It is becoming more common. • E2PROM is used for most data storage. Analogous to Hard drive in PC. It can be read and written any time. It accounts for more than half of the total chip area. • RAM is a temporary working storage. Volatile. 128 to 512 Bytes. • FERAM or FRAM (Ferro-electric RAM)is a new technology. Nonvolatile. A replacements for E2PROM.
Smart Card Components (cont’d) • Memory (cont.) • FERAM (cont.), write time is about the same, writing requires less energy. It is important for contactless cards • Contacts • Up to 8 contacts, the position and designation are defined by ISO 7816-2. • Antenna • All input-output - and often the power - is transmitted by RF signals. • The distance can be up to 1m.
Smart Card Components (cont’d) • Input - output • Bi-directional serial input-output interface. • Mask • Fixed program for an application rather than an operating system. • It is becoming more like an operating system as the multi-application cards are getting more popular. • Therefore, common operating system problems becomes a concern for the manufacturers as well as its own intrinsic problems such as data access control between the different applications.
Chip Security Features • Address scrambling of ROM and E2PROM. • Light, high and low-frequency, voltage and temperature detectors. • Protection layers to prevent scanning. • Null operations. • The buss is not accessible from outside.
System Components • A smart card is an element in a distributed computing system. • Readers, Terminals, PINpads, PC readers, EPOS or EFT-POS terminals, ATMs, Vending machines, • Trusted Third Parties • Authentication hosts, Evidence centers, Key escrow Challenge Response 1. Generates challenge 2. Signs 3. Response Certificate 5. Checks certificate 4. Passes 6. Checks response
Passwords and Biometrics • To identify or verify the identity of card holder. • Passwords or PIN numbers • Can be forgotten, given away, guessed • Tokens • Can be lost or stolen, lent or transferred to someone else deliberately. • Biometrics • Used in high security applications along with passwords, PINs or tokens.
Passwords and Biometrics (cont’d) • Biometrics (cont.) • Signature verification, Keystroke dynamics voice recognition. • Fingerprint, hand geometry, retina scan, iris scan, etc. • Template for the biometrics can be stored in smart cards as well as on a central system.
Security • Security is one of the main issues in smart cards. • Availability of more powerful and secure smart cards depends on the cryptographic techniques used in the transactions. • The card may require identification, not only from card users, but even from the interface device which it is trying to communicate. • Smart cards contain sensitive information which should not be exposed in any circumstances.
Security (cont’d) • To eliminate the need for online authorization in financial applications, a smart credit or debit card could be authenticated offline. • Data access should be controlled. • Non-repudiation in commercial transactions. • Shopping in the Internet. • All these requirements can be satisfied using advanced cryptographic techniques.
Authentication • Replace password-based schemes. • Static Authentication • the card contains a certificate issued under the secret key of its card issuer, whose public key, signed by the scheme, also features on the card. • This scheme does not require cryptographic processing. • Only issuer has got private and public key pairs. • Simple, however not secure.
Authentication (cont’d) Scheme public key Card Data : - SDA Certificate - Issuer Public Key Certificate 1. Card Sends : - selected card data - card data certificate - issuer public-key certificate 2. Terminal decodes issuer public key using scheme public key. 3. Verifies card certificate using issuer public key 4. Compares with hashed form of the card data Static Data Authentication
Authentication (cont’d) • Dynamic Authentication • Challenge-based. • The terminal issues a challenge to the card, • The card signs the card serial number and this challenge. • The terminal verifies this signature. • The card must incorporate the public-key encryption functions. • The private key is permanently stored in the card and protected by physical security features. • Key management issue.
Reset card Answer to reset Select Application Send Application Data Auth. card & terminal Terminal risk management Request cryptogram Card risk management Send cryptogram (Perform online Transaction) Send Results (Complete Transaction) Authentication (cont’d) EMV Transaction Model
Public Key Algorithms Used in Smart Cards • RSA • Gemplus’ GPK4000 smart card features an advanced cryptographic co-processor and is the first public key smart card. The GPK4000’s functionality includes 1024-bit RSA-based digital signature with 4KBytes of application memory. Signing takes less than a second. • The Philips crypto-controller P83C858, utilizing RSA public-key cryptography, will be used in Visa smart card as a market trial in the United Kingdom and Japan.
Public Key Algorithms Used in Smart Cards (cont’d) • ECC • It requires much less memory than RSA. • It does not require a co-processor • Currently, no smart card with ECC is available in the market. • In 1997, VeriFone, owned by HP, licenced Certicom’s Elliptic Curve Engine to secure its VeriSmart System and Personal ATM devices for downloading cash onto smart cards in the home. No product is available so far.
Confidentiality • Sensitive data are stored in card memory in an encrypted form. • A smart card may be used on line for cryptographic transmission to remote users. • For encrypting data, in most cards DES is currently implemented. • TELEPASS is a proprietary algorithm which uses 48-bit key. • One time keys are used for data encryption. The technique is called digital envelope.
Smart Card Keys • Manufacturer keys • Protection keys avoid access to special memory zones. • Personalization key is the card ID to allow applications to recognize the card. • Issuer keys are used to protect the issuer’s data and critical parts of the application as well as to recover a blocked card or to recycle outdated cards.
Smart Card Keys (cont’d) • Secret keys are used for confidentiality and authentication. They are stored by the manufacturers or issuers. • User keys • Different PIN numbers to access to different applications • A typical smart card specifies one manufacturer key, one personalization key, one primary issuer key, four secondary issuer keys, and four user keys
Applications • Telephony & Telecommunications • Prepaid phone cards • Reloadable and account cards • GSM cards • TV decryption • Computer system access • Internet purchases • Internet mail • Data and program confidentiality
Financial Applications Card scheme • ATM, Debit Credit and Charge cards. • Benefit Payments • Retailer Loyalty • Transaction Authorization Merchant acquirer Card issuer Goods Retailer Card holder
Financial Applications (cont’d) 1. Make purchase • Electronic purses : stored value cards. • mondex card & wallet. • card-to-card transactions. • disposable or reloadable • multiple currencies. • Europay (world), PayCard (Germany), Danmont (Denmark), Mcard (U.S.). 2. Make payment 3. Transaction sent to host computer
Applications (Health) • Insurance Cards • Health Cards • Confidentiality is important. • Santal Cards in France. • Opto-smart card in Germany • ATM and debit cards in San Marino contains a health zone. • Exeter Care card in UK.
Applications (Health) Emergency Administration Dental care Transplant Children Pharmacy Home care Blood donor Pregnancy Eye surgery Hypertension Family Care Consultation Hospital
Applications (Transport) • Public Transportation • Electronic Ticketing • In-flight Entertainment • Road Tolling • Parking
PTO 2 PTO 3 PTO 4 Applications (Transport) Revenue Public transport operator 1 Issues card Determines concessionary rates Sets validity periods Records “home” journeys Scheme coordinator Claims revenue entitlement, subsidy Checks validity Checks concessionary rates Records “away” journeys
Application (Others) • User Identification Cards • University Cards • Used by universities in France, Italy, US and Canada. • Pilot projects in Spain, Norway, Australia. • British Gas Card - smart card solution called Quantum • PCMCIA Cards • Follow-me Phones by Siemens (Germany).
Application (University Card) Coffee Shop Book Shop Information Photocopiers Car park Health Administration Library
The Future: Multi-application Cards • Secure operating system. • Downloading. • Hybrid card types • Card control • Issuer responsibility • Consumer issues • Interchange and compatibility with existing card types
Active Smart Card Research And Projects • Third CARDIS conference (Sept 14-16) in Belgium. • IC architecture and techniques • Standards and fault tolerance • Specific co-processors for cryptography • Operating systems & application design • Algorithms & protocols for identification, authentication, verification • Convergence with portable PCs • Internet Payment System