Suspicious Activity Reporting
Shaping the Future of Public Safety and Collaboration. XML Exchange Development. Deploy. Requirements. NIEM. Mo del Data. Test. Suspicious Activity Reporting. Build Exchange. Generate Dictionary. Overview – Public Sector NIEM Team, December 2011.

Suspicious Activity Reporting
E N D
Presentation Transcript
Shaping the Future of Public Safety and Collaboration XML Exchange Development Deploy Requirements NIEM Model Data Test Suspicious Activity Reporting Build Exchange Generate Dictionary Overview – Public Sector NIEM Team, December 2011
The following is intended to outline Oracle general product direction. It is intended for information purposes only, and may not be incorporated into any contract. It is not a commitment to deliver any material, code, or functionality, and should not be relied upon in making purchasing decisions. The development, release, and timing of any features or functionality described for Oracle’s products remains at the sole discretion of Oracle. DisclaimerNotice
Introduction In the ten years since 9/11/2001, we have seen the information sharing challenges in the public safety arena expand beyond terrorist threats to encompass a broad set of criminal justice, emergency management, intelligence, and other homeland security activities.Has the power and breadth of available information sharing solutions kept up with the scale and scope of the problem? What solutions are needed for 2020 problems? By examining current architecture and data sharing methods, the community can address the needs that must be met to deliver the next generation of pragmatic solutions with standards-based information sharing.
Community, Collaboration and Safety Social Challenges and Community Involvement Enabling Technologies – SAR v2 Standards and Initiatives Summary
Society Today Social Challenges
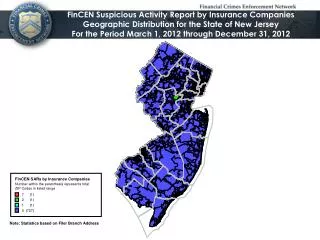
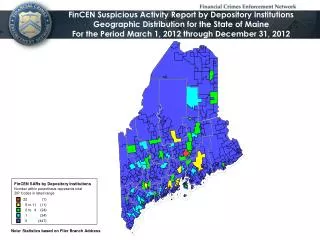
National SAR Initiative Position Focus is on law enforcement and financial services sector rather than broad citizen and community involvement http://www.ise.gov/nationwide-sar-initiative ISE coordination: Current NSI sites: http://nsi.ncirc.gov/implementation_map.aspx • Current thinking of the office of the Director of National Intelligence cites suspicious behavior as“observed behavior that may be indicative of intelligence gathering or pre-operational planning related to terrorism, criminal or other illicit intention. Behavior that could be considered suspicious and potentially tied to terrorism, and thus warrant a report, includes surveillance, photography of facilities, site breaches or physical intrusions, cyberattacksand the examination of security.”
Public Safety Areas and Scope Seemingly unconnected activity and participants provide key markers to intended criminal or terrorist patterns
Citizens and Averting Future Tragedy • Who knew that Anders Behring Breivikwas a disturbed fanatic planning to detonate a car bomb and then attack innocent children? • Who knew Michael Vick was involved in illegal dog fighting rings from his property? Who knew that NordineAmrani had acquired three hand grenades a shotgun and automatic weapon?
Vision for Collaborative SAR initiative • Empowering community collaboration across all aspect of public safety not just terrorism and priority government sector targets • Integrating first responder systems to allow coordination to maximize resources • Providing a complete suite of solutions, not just islands of coordination
Suspicious Activity Report (SAR) V2 Enabling Technologies
Upgrading First Responder Coordination • First responders and paramedics are using personal smart phones to bridge gap • Existing systems using telephone landlines and dispatchers – with different dispatchers not able to see each others information • Need is for emergency responder coordination systems with online view of developing situations and units involved along with real time feedback from those responders, including video feeds
Budget Restrictions v Policing Scope • America continues to allocate significant budgets to law enforcement and policing • The key to effective policing has always been enabling citizen participation combined with responsiveness and follow through • Policing has to cover an ever increasing raft of areas • How to leverage information technologies and communications tools to allow limited police resources to do more? • Better first responder coordination
Information Sharing has Critical Role • Can act to bring together communities and law enforcement to combat challenges posed by world today • Provide people with sense of involvement and security • Combines Mobile, Social and Internet tools • Enable reporting and collaboration between community and law enforcement
Capabilities and Benefits • Ensure privacy / security with built-in oversight and auditing to minimize risks • Reduce costs through use of open standards and common shared infrastructure and deployments (e.g. cloud computing, mobile communications networks) • Rapid response to events - natural and man made • Secure first responder integration and coordination tools
Overview and Highlights Enabling Technologies
NIEM and Information Sharing • A national program supported by the Federal government, connecting communities who share a common need to exchange information in order to advance their missions at state, local and tribal levels • Provides a common vocabulary for information exchange • Offers an online repository of information exchange package documents (IEPDs) • Provides tools to support exchange development • Provides a community of users and support that enables enterprise-wide information exchange. • NIEM going international; Canada, Mexico, Europe.
Next Generation Collaboration Diagrams of cloud, secure social media, mobile, big data, event analysis and correlation Secure communications infrastructure with fault tolerance and security
Toward 2020 Policing and Community Coordination Standards and Initiatives
Focus Areas • IJIS NSI initiative • SAR v2.0 development • Public Events protection and support • Community natural disaster recovery • Man made incident responding • First responder coordination
SAR components • SAR v1.5 components • NIEM core dictionary • LEXS 3.1.4 dictionary LEXS components referenced dictionaries NIEM core components XML XML XML New structure components based on NIEM + SAR + new Definitions stored as syntax neutral canonical XML Example - Suspicious Activity Report V2.0 Dictionary Collection DRAFT Namespaces of dictionary components
Reviewing Technology Efforts Summary and review
Summary of Technologies • Short term initiatives • SAR V2.0 standard • Proof of Concept verification • Medium term objectives • Fusion Center integration • Open platform architecture • Cloud availability, mobile alerts and reporting • First responders coordination • Long term vision • Advanced policing techniques • Analysis, Events, Reporting, Trends (e.g. FBI UCR)
Work in Progress NIEM – information exchange services development LEXS messaging systems and enabling secure information exchanges Middleware integration – SOA stack or OSS stack Dictionaries – domain canonical collections of NIEM components management Application solutions – SAR, Emergency Management, Child Services, State Department -Person Lookup
Q & A • Resource Center link • http://www.oracle.com/goto/niem Download the CAM editor toolkit from: http://www.cameditor.org