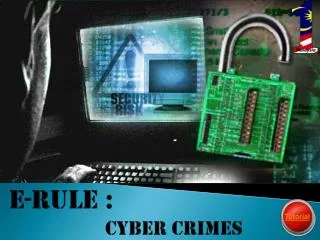
e-Rule
e-Rule. By Syazwani binti safee Pb11077 Nurul ashikin binti rani PB11083. cyber crimes. Big increase in cyber crimes (The Star 27 Apr 2011)

e-Rule
E N D
Presentation Transcript
e-Rule By Syazwanibintisafee Pb11077 Nurulashikinbintirani PB11083
cyber crimes • Big increase in cyber crimes (The Star 27 Apr 2011) KUALA LUMPUR: There has been an increase in cyber crimes in Malaysia over the last two years, more than 3,500 of them reported in the first three months of this year. CyberSecurity Malaysia chief operating officer ZahriYunos said some 8,000 cases were reported last year and attributed this to the growth in Internet usage and broadband penetration that now stood at 55%.
What is cyber crime? • Also known as computer crime,digital crime, e-crime and electronic crime
Internet banking fraud intrusion Examples of cyber crimes harrasment Intellectual property infringement
More example cyber crime • Identify Theft Some criminals use the Internet to break intovictims' online financial accounts, taking passwords, money and sensitive information • Computer Viruses Computer hackers are digital age criminals that can bring down large infrastructures with a single keystroke emitting a computer virus
Reasons for cyber crime For financial means Purely out of mischief To signal some form of protest Reasons for cyber crime Purely to pursue criminal activities Identity theaf Revenge on someone they hate To forge documents
Property infringements and legal right • Software piracy That action against the law when the employees install the same programme on multiple using software for which one license agreement was paid. -freeware and shareware Freeware allow you copy or download without payment Share ware is a software that canused by everyone for free for a limited time period only -treacherousCyber-vandals like to change the public site and display the information and how it canbe done by hackers as disloyal are interpreted to severe penalties. -stolenIf the contractor can access via the Internet to other users' information such as personal data, lists, records, personal e-mails, even with good intentions can be defined as theft
JenayahSiberdi Malaysia Naik 100%13 Januari 2009 (Harian Metro) • PULAU PINANG 25 Julai – Sebanyak 6,167 kespenipuandalam Internet melibatkannilaikerugian RM63 jutadilaporkandinegarainisepanjangtahunlalu.Iameningkatempat kali gandadalamtempohempattahunberbandingpada 2007 yang hanyamencatatkan 1,139 kesdengannilai RM11.4 juta. (Sumber:http://www.utusan.com.my/utusan/info.asp?y=2011&dt=0726&pub=Utusan_Malaysia&sec=Jenayah&pg=je_01.htm)
Kesanjenayahsiber • Kerugianwang ringgit. Inikesbiasa yang berlakudi internet. Contohnyaditipumelalui chatting room Yahoo Messenger. • Maruahdiritercemar. Contohmudahapabila video dangambarkurangeloktersebarmeluasolehorang yang tidakbertanggungjawab. • Kestabilanpolitiktergugat. Contoh paling mudahapabilaseorangremajamenghinalaguNegaraKu, makatersebarkesegenappelusukdunia