Modest Proposals for Layered Email Authentication
50 likes | 159 Vues
In the 2005 APCauce/Apricot conference, D. Crocker discusses the complexities of email systems and proposes solutions for layered email authentication. The presentation highlights key actors such as Mail User Agents (MUA), Mail Submission Agents (MSA), and Mail Transfer Agents (MTA). Crocker emphasizes the need to evaluate the legitimacy of these actors to establish trust in email communications. Various proposals for email authentication methods like SPF, Sender-ID, and DomainKeys are covered, alongside the challenges presented by different email actors that could lead to spam or other issues.

Modest Proposals for Layered Email Authentication
E N D
Presentation Transcript
Modest Proposals for Layered Email Authentication APCAUCE/APRICOT – Kyoto 2005 D. Crocker dcrocker@bbiw.net Brandenburg InternetWorking bbiw.net
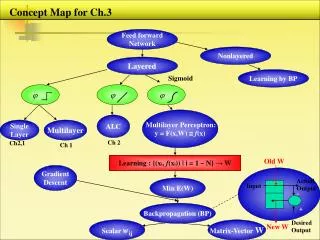
.forward MDA MSA MTA PeerMTA MTA List MTA MDA MTA MTA MDA MUA Email is… Complicated! MUA MSA MTA MTA PeerMTA MTA Mail Agents MUA = User MSA = Submission MTA = Transfer MDA = Delivery MTA MDA MUA D. Crocker APCauce/Apricot – Kyoto, 2005
Recipient Originator DeliveryAgent Sender Relay Relay Bounce Email Actors/Participants • Which actor/participant is being evaluated? • Which actor/participant is vouching for them? D. Crocker APCauce/Apricot – Kyoto, 2005
Challenge Different email actors Each might create problems Each might prevent problems Goal Identify actors Evaluate their legitimacy Decide whether to trust their message traffic Proposals Path Registration Meng Wong SPF Sender-ID Crypto Message Authentication Jim Fenton Identified Internet Mail (IIM) DomainKeys Handling Service Support Dave Crocker Certified Server Validation (CSV) Bounce Address Tag Validation (BATV) What we will cover D. Crocker APCauce/Apricot – Kyoto, 2005
Universal spam solution rebuttal Checkbox form-letter for responding to spam solutions proposals. See: <http://craphound.com/spamsolutions.txt> Your post advocates a ( ) technical ( ) legislative ( ) market-based ( ) vigilante approach to fighting spam. Your idea will not work. Here is why it won't work. (One or more of the following may apply to your particular idea, and it may have other flaws which used to vary from state to state before a bad federal law was passed.)… D. Crocker APCauce/Apricot – Kyoto, 2005