HAPTER 7
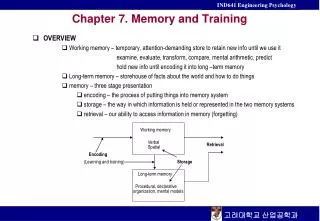
HAPTER 7. Information Systems Controls for Systems Reliability Part 1: Information Security. INTRODUCTION. Questions to be addressed in this chapter: How does security affect systems reliability?

HAPTER 7
E N D
Presentation Transcript
HAPTER 7 Information Systems Controls for Systems Reliability Part 1: Information Security
INTRODUCTION • Questions to be addressed in this chapter: • How does security affect systems reliability? • What are the four criteria that can be used to evaluate the effectiveness of an organization’s information security? • What is the time-based model of security and the concept of defense-in-depth? • What types of preventive, detective, and corrective controls are used to provide information security? • How does encryption contribute to security and how do the two basic types of encryption systems work?
INTRODUCTION • One basic function of an AIS is to provide information useful for decision making. In order to be useful, the information must be reliable, which means: • It provides an accurate, complete, and timely picture of the organization’s activities. • It is available when needed. • The information and the system that produces it is protected from loss, compromise, and theft.
INTRODUCTION • The five basic principles that contribute to systems reliability: SYSTEMS RELIABILITY
INTRODUCTION • The five basic principles that contribute to systems reliability: • Security SYSTEMS RELIABILITY • Access to the system and its data is controlled. SECURITY
INTRODUCTION • The five basic principles that contribute to systems reliability: • Security • Confidentiality SYSTEMS RELIABILITY CONFIDENTIALITY • Sensitive information is protected from unauthorized disclosure. SECURITY
INTRODUCTION • The five basic principles that contribute to systems reliability: • Security • Confidentiality • Privacy SYSTEMS RELIABILITY • Personal information about customers collected through e-commerce is collected, used, disclosed, and maintained in an appropriate manner. CONFIDENTIALITY PRIVACY SECURITY
INTRODUCTION • The five basic principles that contribute to systems reliability: • Security • Confidentiality • Privacy • Processing integrity SYSTEMS RELIABILITY • Data is processed: • Accurately • Completely • In a timely manner • With proper authorization CONFIDENTIALITY PROCESSING INTEGRITY PRIVACY SECURITY
INTRODUCTION • The five basic principles that contribute to systems reliability: • Security • Confidentiality • Online privacy • Processing integrity • Availability SYSTEMS RELIABILITY CONFIDENTIALITY PROCESSING INTEGRITY PRIVACY AVAILABILITY • The system is available to meet operational and contractual obligations. SECURITY
INTRODUCTION • Note the importance of security in this picture. It is the foundation of systems reliability. Security procedures: • Restrict system access to only authorized users and protect: • The confidentiality of sensitive organizational data. • The privacy of personal identifying information collected from customers. SYSTEMS RELIABILITY CONFIDENTIALITY PROCESSING INTEGRITY PRIVACY AVAILABILITY SECURITY
INTRODUCTION • Security procedures also: • Provide for processing integrity by preventing: • Submission of unauthorized or fictitious transactions. • Unauthorized changes to stored data or programs. • Protect against a variety of attacks, including viruses and worms, thereby ensuring the system is available when needed. SYSTEMS RELIABILITY CONFIDENTIALITY PROCESSING INTEGRITY PRIVACY AVAILABILITY SECURITY
COBIT and Trust Services • Control Objectives for Information Technology (COBIT) • Information systems controls required for achieving business and governance objectives Adequate Controls
FUNDAMENTAL INFORMATION SECURITY CONCEPTS • There are three fundamental information security concepts that will be discussed in this chapter: • Security as a management issue, not a technology issue. • The time-based model of security. • Defense in depth.
FUNDAMENTAL INFORMATION SECURITY CONCEPTS • There are three fundamental information security concepts that will be discussed in this chapter: • Security as a management issue, not a technology issue. • The time-based model of security. • Defense in depth.
SECURITY AS A MANAGEMENT ISSUE • Though information security is a complex technical subject, security is first and foremost a top management issue, not an IT issue.
SECURITY AS A MANAGEMENT ISSUE • Management is responsible for the accuracy of various internal reports and financial statements produced by the organization’s IS. • SOX Section 302 requires that the CEO and CFO certify the accuracy of the financial statements. • SOX Section 404 requires that the annual report include a report on the company’s internal controls. Within this report, management acknowledges their responsibility for designing and maintaining internal controls and assessing their effectiveness. • Security is a key component of the internal control and systems reliability to which management must attest. • As identified in the COSO model, management’s philosophy and operating style are critical to an effective control environment.
SECURITY AS A MANAGEMENT ISSUE • The Trust Services framework identifies four essential criteria for successfully implementing the five principles of systems reliability: • Develop and document policies. • Effectively communicate those policies to all authorized users. • Design and employ appropriate control procedures to implement those policies. • Monitor the system, and take corrective action to maintain compliance with the policies. • Top management involvement and support is necessary to satisfy each of the preceding criteria.
FUNDAMENTAL INFORMATION SECURITY CONCEPTS • There are three fundamental information security concepts that will be discussed in this chapter: • Security is a management issue, not a technology issue. • The time-based model of security. • Defense in depth.
TIME-BASED MODEL OF SECURITY • Given enough time and resources, any preventive control can be circumvented. • Consequently, effective control requires supplementing preventive procedures with: • Methods for detecting incidents; and • Procedures for taking corrective remedial action. • Detection and correction must be timely, especially for information security, because once preventive controls have been breached, it takes little time to destroy, compromise, or steal the organization’s economic and information resources.
TIME-BASED MODEL OF SECURITY • The time-based model of security focuses on implementing a set of preventive, detective, and corrective controls that enable an organization to recognize that an attack is occurring and take steps to thwart it before any assets have been compromised. • All three types of controls are necessary: • Preventive • Limit actions to those in accord with the organization’s security policy and disallows all others.
TIME-BASED MODEL OF SECURITY • The time-based model of security focuses on implementing a set of preventive, detective, and corrective controls that enable an organization to recognize that an attack is occurring and take steps to thwart it before any assets have been compromised. • All three types of controls are necessary: • Preventive • Detective • Identify when preventive controls have been breached.
TIME-BASED MODEL OF SECURITY • The time-based model of security focuses on implementing a set of preventive, detective, and corrective controls that enable an organization to recognize that an attack is occurring and take steps to thwart it before any assets have been compromised. • All three types of controls are necessary: • Preventive • Detective • Corrective • Repair damage from problems that have occurred. • Improve preventive and detective controls to reduce likelihood of similar incidents.
TIME-BASED MODEL OF SECURITY • The time-based model evaluates the effectiveness of an organization’s security by measuring and comparing the relationship among three variables: • P = Time it takes an attacker to break through the organization’s preventive controls. • D = Time it takes to detect that an attack is in progress. • C = Time to respond to the attack. • These three variables are evaluated as follows: • If P > (D + C), then security procedures are effective. • Otherwise, security is ineffective.
FUNDAMENTAL INFORMATION SECURITY CONCEPTS • There are three fundamental information security concepts that will be discussed in this chapter: • Security is a management issue, not a technology issue. • The time-based model of security. • Defense in depth.
DEFENSE IN DEPTH • The idea of defense-in-depth is to employ multiple layers of controls to avoid having a single point of failure. • If one layer fails, another may function as planned. • Information security involves using a combination of firewalls, passwords, and other preventive procedures to restrict access. • Redundancy also applies to detective and corrective controls.
DEFENSE IN DEPTH • Major types of preventive controls used for defense in depth include: • Authentication controls (passwords, tokens, biometrics, MAC addresses) • Authorization controls (access control matrices and compatibility tests) • Training • Physical access controls (locks, guards, biometric devices) • Remote access controls (IP packet filtering by border routers and firewalls using access control lists; intrusion prevention systems; authentication of dial-in users; wireless access controls) • Host and application hardening procedures (firewalls, anti-virus software, disabling of unnecessary features, user account management, software design, e.g., to prevent buffer overflows) • Encryption
DEFENSE IN DEPTH • Detective controls include: • Log analysis • Intrusion detection systems • Managerial reports • Security testing (vulnerability scanners, penetration tests, war dialing)
DEFENSE IN DEPTH • Corrective controls include: • Computer emergency response teams • Chief Security Officer (CSO) • Patch Management
Understanding Targeted Attacks • How are they done? • Reconnaissance • Social Engineering • Scan and Map • Research • Attack Execution • Cover Tracks • Collecting information to identify potential vulnerabilities. • Tricking unsuspecting employees into allowing access to system. • Detailed scan of system to identify potential points of remote entry. • Researching vulnerabilities of software identified during scan. • Unauthorized access to system. • Removing evidence of attack.
PREVENTIVE CONTROLS • Major types of preventive controls used for defense in depth include: • Authentication controls (passwords, tokens, biometrics, MAC addresses) • Authorization controls (access control matrices and compatibility tests) • Training • Physical access controls (locks, guards, biometric devices) • Remote access controls (IP packet filtering by border routers and firewalls using access control lists; intrusion prevention systems; authentication of dial-in users; wireless access controls) • Host and application hardening procedures (firewalls, anti-virus software, disabling of unnecessary features, user account management, software design, e.g., to prevent buffer overflows) • Encryption
PREVENTIVE CONTROLS • The objective of preventive controls is to prevent security incidents from happening. • Involves two related functions: • Authentication • Focuses on verifying the identity of the person or device attempting to gain access. • Authorization • Restricts access of authenticated users to specific portions of the system and specifies what actions they are permitted to perform.
PREVENTIVE CONTROLS • Users can be authenticated by verifying: • Something they know, such as passwords or PINs. • Something they have, such as smart cards or ID badges. • Some physical characteristic (biometric identifier), such as fingerprints or voice.
PREVENTIVE CONTROLS • Passwords are probably the most commonly used authentication method and also the most controversial. • An effective password must satisfy a number of requirements: • Length • Longer is better. • Should be at least 8 characters.
PREVENTIVE CONTROLS • Passwords are probably the most commonly used authentication method and also the most controversial. • An effective password must satisfy a number of requirements: • Length • Multiple character types • Use a mix of upper-and lower-case alphabetic, numeric, and special characters.
PREVENTIVE CONTROLS • Passwords are probably the most commonly used authentication method and also the most controversial. • An effective password must satisfy a number of requirements: • Length • Multiple character types • Random • Passwords should not be words found in the dictionary or dictionary words preceded or followed by a number such as 4dog or dog4. • Should not be related to the employee’s personal interests or hobbies, because special-purpose, password-cracking dictionaries can be found on the Internet containing the most common passwords related to various topics.
PREVENTIVE CONTROLS • Passwords are probably the most commonly used authentication method and also the most controversial. • An effective password must satisfy a number of requirements: • Length • Multiple character types • Random • Secret • The most important requirement. • A password must be kept secret to be effective.
PREVENTIVE CONTROLS • A password that meets the preceding criteria is typically difficult to memorize—exacerbated by the typical requirement that the password be changed every 90 days. • So most people either: • Select passwords that can be easily guessed but can be memorized; or • Select passwords that meet the criteria for a strong password but write them down. • When the password is written down, it changes from something the employee knows to something the employee has, which can be stolen and used.
PREVENTIVE CONTROLS • As a result of this dilemma, some security experts argue for abandoning the quest to develop and use strong passwords. • They note that a major component of help desk costs is associated with resetting passwords. • They suggest reliance on dual-factor authentication methods, such as a combination of a smart card and a PIN number.
PREVENTIVE CONTROLS • Other experts disagree. • They note that operating systems can now accommodate passwords longer than 15 characters. • So users can create strong but easy-to-remember paraphrases like: Idlike2binParis. • Long paraphrases dramatically increase the effort required to crack them by guessing. • So this group argues that longer length, coupled with the fact that it is easier to remember a long paraphrase than a strong password, should dramatically cut help desk costs while improving security.
PREVENTIVE CONTROLS • Each authentication method has its limitations. • Passwords • Can be guessed, lost, written down, or given away.
PREVENTIVE CONTROLS • Each authentication method has its limitations. • Passwords • Physical identification techniques • Include cards, badges, and USB devices. • Can be lost, stolen, or duplicated.
Expensive and often cumbersome. • Not yet 100% accurate, sometimes rejecting legitimate users and allowing unauthorized people. • Some techniques like fingerprints may carry negative connotations that hinder acceptance. • Security concerns surround the storage of this data. • If the data is compromised, it could create serious, life-long problems for the donor. • Unlike passwords or tokens, biometric identifiers cannot be replaced or changed. PREVENTIVE CONTROLS • Each authentication method has its limitations. • Passwords • Physical identification techniques • Biometric techniques
PREVENTIVE CONTROLS • Although none of the three basic authentication methods is foolproof by itself, the use of two or three in conjunction, known as multi-factor authentication, is quite effective. • Example: Using a palm print and a PIN number together is much more effective than using either method alone.
PREVENTIVE CONTROLS • Authorization controls are implemented by creating an access control matrix. • Specifies what part of the IS a user can access and what actions they are permitted to perform. • When an employee tries to access a particular resource, the system performs a compatibility test that matches the user’s authentication credentials against the matrix to determine if the action should be allowed.
PREVENTIVE CONTROLS • Who has the authority to delete Program 2?
PREVENTIVE CONTROLS • Which files can user 12354 access?
PREVENTIVE CONTROLS • Which programs can user 12354 access?
PREVENTIVE CONTROLS • The access control matrix should be regularly updated, so that an employee who changes job duties cannot accumulate a set of rights that are incompatible with proper segregation of duties.
PREVENTIVE CONTROLS • Authentication and authorization can be applied to devices as well as users. • Every workstation, printer, or other computing device needs a network interface card (NIC) to connect to the organization’s network. • Each network device has a unique identifier, referred to as its media access control (MAC) address. • It is possible to restrict network access to only those devices which have a recognized MAC address or to use MAC addresses for authorization. • For example, payroll or EFT applications should be set only to run from authorized terminals. • MAC address can be changed using software making it possible to “spoof” a machine’s identity.
Training Control Physical Access Control Remote Access Hardening Encryption PREVENTIVE CONTROLS • These are the multiple layers of preventive controls that reflect the defense-in-depth approach to satisfying the constraints of the time-based model of security.