RSA Cryptosystem
RSA Cryptosystem. by Drs. Charles Tappert and Ron Frank The information presented here comes primarily from https ://en.wikipedia.org/wiki/RSA_(cryptosystem ) and http://www.math.uchicago.edu/~ may/VIGRE/VIGRE2007/ REUPapers /FINALAPP/Calderbank.pdf. RSA Cryptosystem.

RSA Cryptosystem
E N D
Presentation Transcript
RSA Cryptosystem by Drs. Charles Tappert and Ron Frank The information presented here comes primarily from https://en.wikipedia.org/wiki/RSA_(cryptosystem) and http://www.math.uchicago.edu/~may/VIGRE/VIGRE2007/ REUPapers/FINALAPP/Calderbank.pdf
RSA Cryptosystem • RSA is the most commonly used public-key cryptosystem • Named after its developers: Rivest, Shamir, Adleman • Developed when they were in their early 20s and researchers at the MIT Lab • Algorithm announced in Scientific American in 1977 • RSA is based on Euler’s number theoretic result • If p and q are prime numbers and a is an integer not divisible by either p or q, then • a(p-1)(q-1) = 1 mod pq • φ(pq) = φ(p) φ(q) = (p-1)(q-1)
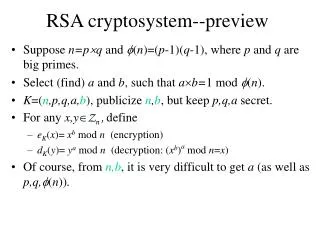
RSA Cryptosystem • The principle behind RSA is to find 3 very large positive integers n, e, and d such that • (me)d = m (mod n) where m = the message < n • e encodes, d (difficult to find unless provided) decodes • and n is the product of two very large integers p and q • The RSA algorithm involves four steps • Key generation • Key distribution • Encryption • Decryption
RSA Cryptosystem Key generation • Choose two distinct large prime numbers p and q • n = pq is the modulus for both public & private keys • Compute l(n) = lcm(f(p),f(q)) = lcm(p-1,q-1) • Where l is Carmichael’s totient function • Choose an integer e such that 1 < e < l(n) and gcd(e,l(n)) = 1 (that is, e and l(n) are coprime) • Determine d as d = e-1 (mod l(n)) • That is, solve for d from de = (mod l(n)) • e = public key exponent, d = private key exponent • Public key = (n, e), Private key = (n, d)
RSA Cryptosystem Key Distribution, Encryption, Decryption • Distribution: the public key (n, e) is distributed • Encryption: plaintext message is converted into an integer m, then encrypted into code c = me (mod n) • Decryption: m = cd (mod n)
RSA Cryptosystem Example • Choose two distinct prime numbers p=61 & q= 53 • Compute n = pq = 61*53 = 3233 • Compute l(n) = lcm(p-1,q-1) = lcm(60,52) = 780 • Choose any integer e < 780 coprime to 780, let e=17 • Compute d from de = 1 mod l(n) to get d = 413 • Public key (n=3233, e=17) • Send plaintext message “A”, m = 65 (ASCII for “A”) • Encode c = 6517 mod 3233 = 2790 • Private key (n=3233, d=413) • Decode c=2790: m = 2790413 mod 3233 = 65
RSA Cryptosystem Calculator • http://umaranis.com/rsa_calculator_demo.html • https://www.cs.drexel.edu/~jpopyack/IntroCS/HW/RSAWorksheet.html