Cryptology
E N D
Presentation Transcript
Cryptology Kylie Brown
Outline • Introduction • What is Cryptology • Confusion and Diffusion • History • Methods • Single Key • Public Key • Cryptanalysis Overview • Ethics
Introduction What is Cryptology Confusion and Diffusion History
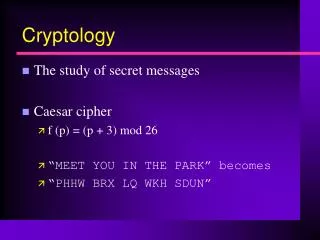
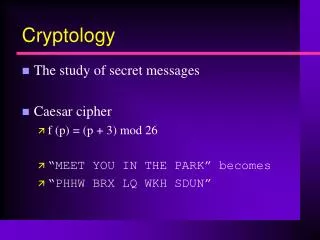
What is Cryptology • The use and study of methods of hiding information • Plaintext: The message (not encrypted) • Cipher text: The encrypted message • Encryption: The process of converting the plaintext into cipher text • Code: Rule for replacing a piece of the plaintext with something else • Key: Known only b the transmitter and receiver, used to encrypt/decrypt the message • Cryptanalysis: The science of code breaking
Confusion and Diffusion • Confusion: The interceptor should not be able to predict the effect of changing one symbol of plaintext will affect cipher text. • Diffusion: Information from plaintext should be spread throughout the cipher text so that changes to the plaintext will cause changes throughout the cipher text.
History • Spartans in Ancient Greece • First documented use of cryptography • Used a tapered baton called a scytale • The message could only be read when the parchment upon which the message was written was wrapped around the scytale • 4th Century BC: first treatise • Written by Aeneas Tacticus • In the book: On the Defense of Fortifications
History • WWI • Most famous cipher was the German ADFGVX fractional cipher • WWII • Rotor Cipher Machines • Most famous Cipher Machine: Germany’s Enigma • Cracked by the British using the Turing Bomb
Methods Single Key Monoalphabetic Ciphers Polyalphabetic Ciphers DES AES Public Key Key Distribution RSA
Single Key • Key for encrypting and decrypting are the same • Monoalphabetic Cipher: Each letter in the plaintext will always be replaced by the same letter/symbol • Ex: Caesar Cipher • Polyalphabetic Cipher: Each letter in the plaintext may not always be replaced by the same letter/symbol • Ex: Playfair Cipher
Substitution: Monoalphabetic Cipher • Caesar Cipher: Shift the alphabet • DOG = GRJ • Keyword: keyword then fill in alphabet • COMPUTER SCIENCE = CJGKSQOM PCYOHCO
Substitution: Playfair • Polyalphabetic Cipher • Charles Wheatstone in 19th Century England • 5X5 grid, fill in the key at the beginning and then add the rest of the alphabet (in order) • I/J are in the same box • Pair the letters of the message into digrams. • If there is an odd number, add X to the end • If there a digraph is made up of identical letter, separate them with a different letter
Playfair • Rules for exchanging letters • If the columns and rows are different • New letter is the row of the current letter and the column of its pair • If the rows are the same • New letter is the one to the right • If the columns are the same • New letter is the one below
Key: Dictionary • Message: Computer Science • CO MP UT ER SC IE NC EX • TD PQ XD GN PO DF RD HU • What is this? ODMCQZ
Problems with Monoalphabetic • Monoalphabetic ciphers are easy to break (think cryptoquip) • Find most commonly used letters (E, T, A, O, N, I, R, S, H) • Find most commonly used digrams and trigrams (ex: the, st) • Then the most common trigrams, etc. • Spacing makes it even easier (so don’t carry over spaces)
Substitution: Vigenere • Polyalphabetic Cipher • How it works • Choose a key • Write the key for the length of the message • (p+k)mod26
Substitution: Autokey • Repetition was Vigenere’s undoing • How to use autokey • Write key once • Fill in the rest with either the plaintext or cipher text
Transposition: Route Ciphers • Rail Fence: stagger plaintext between X rows • Ex: Computer Science with rail fence 2
Route Ciphers • A better method: • Create a matrix with a keyword across the top row. • Fill the Matrix from left to right with the message • Take the letters from top to bottom by alphabetic order of the keyword (do not take keyword)
Example I LIKE TO PLAY WITH MATRICES IAAZIPHELLMSTIIZKYTZOTCZEWRZ
Product Cipher: ADFGVX • Uses a 6X6 matrix and a key to encrypt the message into the letters A,D,F,G,V, and X • Fill the matrix in with the keyword and then the rest of the alphabet in order, followed by the numbers 0-9 (no doubles) • Replace each cipher text letter with the two letters that mark its row and column
ADFGVX Example • Message: Computer Science, Key: Dictionary • AFAVFXGAGGAGDVGFAFADAVAXAFDV
Stream vs. Block Cipher • A stream cipher translates plaintext into cipher text symbol by symbol • Most of the methods discussed thus far are stream ciphers • Errors like skipping a symbol will corrupt the rest of the message • A block cipher encrypts plaintext by blocks • Reduces corruption and risk of code breaking
Data Encryption Standard • Developed by IBM, based on an encryption algorithm called Lucifer • Proper name: Data Encryption Algorithm
DES Algorithm • Cycles are repeated 16 times • Split the plaintext into 64bit blocks • Key is any 56-bit number with an extra 8 bits on the end • Some people are uncomfortable with only a 56-bit key • Double DES: run twice with 2 different keys • Triple DES: 3 keys. Encrypt, Decrypt, Encrypt
Advanced Encryption Standard • January 1997-August 1999, Encryption “Contest” • Winner: Rijndael (RINE dahl) • Combination of the names of the creators: Vincent Rijmen and Joan Daemen
Overview of Rijndael • Plaintext split into 128-bit blocks • Number of “rounds” based on key size • 10 for 128-bits, 12 for 192-bits, 14 for 256-bits • Four Steps per cycle • Byte Substitution: Using a substitution box, substitute each bit according to a table • Shift Row: for 128 and 192: (n-1)bit left, for 256: row 2 by 1 bit, row 3 by 3 bits, row 4 by 4 bits • Mix Column: XOR bits together • Add Subkey: portion of subkey XOR with result
Problems with Single Key • Sender and Receiver must both hold a copy of the key • What happens if there are 100 people who want to communicate secretly • Each person has to remember 99 keys and must keep each key from being discovered • Number of keys required: 4950
Solution: Public Key • Also called two-key • Each person has two keys • Public key for encrypting • Private key for decrypting • Keep your private key and give everyone else your public key
Background for RSA • Euler Totient: (n) • The number of integers in the set of real numbers less than n that are relatively prime to n • For a prime number, p, (p) = p-1 • For distinct primes p & q, (pq) = (p-1)(q-1) • Examples • (8) = 4 {1,3,5,7} • (91) = (13)*(7) = 6*12 = 72
RSA Algorithm • Pick two large prime numbers (p & q) • Calculate (n) where n= pq • Find e such that e is relatively prime to (n) • gcd(e, (n)) = 1 • Find d such that ed ≡ 1 mod (n) • d is the inverse of e mod (n) • Public keys: e, n • Private Key: d
RSA Encryption and Decryption • Encryption: C = En,e(M) = Me mod n • Decryption: M = Dn,d (C) = Cd mod n
Cryptanalysis Overview • Method used is based on the amount of information • Brute Force: try all possibilities • Dictionary Attack: run through a dictionary of words trying to find the key or plaintext • Cipher text only • Chosen Plaintext: Have the ability to find the cipher text relating to an arbitrary plaintext • Chosen Cipher text: can choose an arbitrary cipher text and know the plaintext • Adaptive chosen plaintext: determine cipher text based on plaintext using iteration
Ethics and Cryptology • Is cryptology ethical? • “Technology has no intrinsic ethical nature” • Wiretapping: Should encryption of digital communication be stymied in order to accommodate this practice? • Proper usage of cryptology is all about individual responsibility • Cryptology should not be withheld
References • Pell, Oliver. Cryptology. http://www.ridex.co.uk/cryptology/ • Arup Guha’s class lectures http://www.cs.ucf.edu/~dmarino/ucf/cis3362/lectures/ • Pfleeger, Charles P. Pfleeger, Shari Lawrence. Security in Computing. 4th Edition. Pearson Education. 2007 • Falk, Courtney. The Ethics of Cryptography. http://www.cerias.purdue.edu/bookshelf/archive/2005-37.pdf