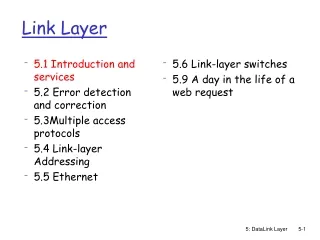
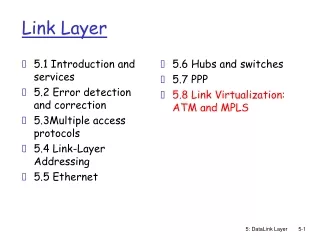
Introduction to Link Layer Protocols in Computer Networks
Learn about the link layer in computer networks, including the roles of hosts, routers, and links, as well as the protocols used for data transmission. Understand concepts such as framing, error detection, and flow control.


Introduction to Link Layer Protocols in Computer Networks
E N D
Presentation Transcript
Link layer د.عـــادل يوسف أبو القاسم
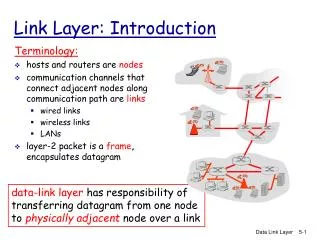
Terminology: عند دراسة ال link layer سنسمي كل من ال host و ال routers سنسميهم nodes . قنوات الاتصال التي تربط ال nodes المتجاورة سنسميها links مثلاً : wired links wireless links LANs ال packets في طبقة الربط سنسميها frame وهي كبسولة تحتوي ال datagram . Link layer: introduction global ISP Link Layer وظيفة طبقة ال link هي نقل ال datagram من node الى node اخرى مجاورة لها فيزيائياً خلال link .
يتم ارسال ال datagram بواسطة different link protocols على different links . مثال : e.g., Ethernet on first link, frame relay on intermediate links, 802.11 on last link transportation analogy: trip from Princeton to Lausanne limo: Princeton to JFK plane: JFK to Geneva train: Geneva to Lausanne tourist = datagram transport segment = communication link transportation mode = link layer protocol travel agent = routing algorithm Link layer: context Link Layer
Link layer services • framing, link access (التقسيم الى frames والوصول الى ال link) • encapsulate datagram into frame, adding header, trailer • channel access if shared medium • “MAC” addresses used in frame headers to identify source, dest • reliable delivery between adjacent nodes • wireless links: high error rates • بدلا من اكتشاف الخطأ في ال end-end افضل اكتشافه على مستوى ال node-node.
Link layer services (more) • flow control: • التحكم في تدفق البيانات من المرسل الى المستقبل. • error detection: • اكتشاف الاخطاء في ال frames. • error correction: • تصحيح الاخطاء التي يتم اكتشافها • half-duplex and full-duplex • with half duplex, nodes at both ends of link can transmit, but not at same time Link Layer
in each and every host link layer implemented in “adaptor” (aka network interface card NIC) or on a chip Ethernet card, 802.11 card; Ethernet chipset implements link, physical layer attaches into host’s system buses application transport network link link physical Where is the link layer implemented? cpu memory Link Layer host bus (e.g., PCI) controller physical transmission network adapter card
Parity checking وفيها يتم اضافة bit للفريم لتحدد هل حدث تعديل للفريم ام لا هذه البت تجعل عدد الواحدات في الفريم فردي او زوجي • Even two-dimensional bit parity: • detect and correct single bit errors • Odd single bit parity: • detect single bit errors هنالك طريقة اخرى لاكتشاف الاخطاء وهي ال checksum والتي تطرقنا لها في محاضرات سابقة
Multiple access links, protocols هنالك نوعين من ال links : • point-to-point • PPP for dial-up access • point-to-point link between Ethernet switch, host • broadcast (shared wire or medium) • old-fashioned Ethernet • upstream HFC • 802.11 wireless LAN Link Layer shared RF (e.g., 802.11 WiFi) shared RF (satellite) shared wire (e.g., cabled Ethernet) humans at a cocktail party (shared air, acoustical)
Multiple access protocols • الاشارات تشترك في قناة اتصال واحدة • اذا ارسل اكثر من جهاز بيانات في نفس الوقت فأن ذلك يؤدي الى حدوث تصادم collision . multiple access protocol • هي عبارة عن خوارزميات موزعة تحدد كيفية مشاركة ال link بين ال nodes المختلفة . Link Layer
An ideal multiple access protocol • ال multiple access protocol المثالي يعمل وفق الآتي: given: broadcast channel of rate R bps الخصائص المطلوبة : • عندما تريد node واحدة الارسال من خلال القناة فأن ال node ترسل بمعدلbpsR • عندما تريد N nodes الارسال , فأن كل node ترسل بمعدل R/M . • يفضل ان يكون لا مركزي حيث لا توجد node معينة مهمتها ادارة عملية المشاركة. • يفضل ان يكون بسيطاً Link Layer
MAC protocols: taxonomy هنالك ثلاثة انواع رئيسيىة من برتكولات ال MAC : • channel partitioning(تقسيم القناة ) • divide channel into smaller “pieces” (time slots, frequency, code) • allocate piece to node for exclusive use • random access(الوصول العشوائي) • channel not divided, allow collisions • “recover” from collisions • “taking turns”(الوصول حسب ترتيب معين) • nodes take turns, but nodes with more to send can take longer turns Link Layer
Channel partitioning MAC protocols: TDMA TDMA: time division multiple access الوصول المتعدد باستخدام تقنية تقسيم زمن الوصول • كل جهاز له فترة معينة slots يصل فيها للقناة في كل دورة. • عيبها ان ال slots غير المستخدمة تكون فيها الشبكة عاطلة. • example: 6-station LAN, 1,3,4 have pkt, slots 2,5,6 idle Link Layer 6-slot frame 6-slot frame 3 3 4 4 1 1
Channel partitioning MAC protocols: FDMA FDMA: frequency division multiple access الوصول المتعدد بتقسيم التردد • يتم فيه تقسيم ال spectrum للقناة الى حزم من الترددات المختلفة • كل جهاز يتم تخصيص حزمة تردد معينة له. • عيبها ان التردد غير المستخدم يصبح عاطل • example: 6-station LAN, 1,3,4 have pkt, frequency bands 2,5,6 idle Link Layer time frequency bands FDM cable
Random access protocols • عندما يريد جهاز ما ارسال رسالة فانه يقوم بارسال الرسالة مباشرة عبر الشبكة حيث لا يوجد تنسيق بين الاجهزة في الارسال. • ميزتها انها تسمح للجهاز بالارسال بمعدل القناة الكامل R . • عيبها انه قد يحدث تصادم Collision . • random access MAC protocol specifies: • how to detect collisions • how to recover from collisions (e.g., via delayed retransmissions) • examples of random access MAC protocols: • slotted ALOHA • ALOHA • CSMA, CSMA/CD, CSMA/CA Link Layer
CSMA (carrier sense multiple access) الفكرة الاساسية هي listen before transmit وهي تحسس القناة قبل الارسال حيث انه اذا كانت القناة خالية قم بالارسال بالمعدل الكامل للقناة , اذا كانت القناة مشغولة أجل الارسال.
رغم عملية تحسس القناة الا ان التصادم لازال يمكن ان يحدث تأخير ال propagation يعني ان جهاز ما قد لا يسمع ارسال جهاز آخر. عند حدوث تصادم فان كل البيانات التي تم ارسالها تكون غير سليمة. CSMA collisions spatial layout of nodes Link Layer
CSMA/CD (collision detection)اكتشاف التصادم CSMA/CD: • CSMA/CD تعمل بنفس طريقة CSMA لكن يتم اكتشاف التصادم وعندها نكون قد قللنا نسبة البيانات التالفة. • يتم اكتشاف الاخطاء بسهولة في الشبكات السلكية حيث يتم قياس قوة الاشارة ومقارنة الاشارات المرسلة والمستقبلة. • difficult in wireless LANs: received signal strength overwhelmed by local transmission strength Link Layer
CSMA/CD (collision detection) spatial layout of nodes Link Layer
1. NIC(Network Interface Card) receives datagram from network layer, creates frame 2. If NIC senses channel idle, starts frame transmission. If NIC senses channel busy, waits until channel idle, then transmits. 3. If NIC transmits entire frame without detecting another transmission, NIC is done with frame ! 4. If NIC detects another transmission while transmitting, aborts and sends jam signal Ethernet CSMA/CD algorithm
“Taking turns” MAC protocols channel partitioning MAC protocols: • share channel efficiently and fairly at high load • inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! random access MAC protocols • efficient at low load: single node can fully utilize channel • high load: collision overhead “taking turns” protocols look for best of both worlds! Link Layer
data data poll “Taking turns” MAC protocols polling: • ال master node تدعو ال slave nodes لارسال بياناتهم حسب الترتيب. • Concerns(عيوبها) : • polling overhead • latency • single point of failure (master) master Link Layer slaves
“Taking turns” MAC protocols token passing: • في هذه الطريقة لا توجد master node . • توجد token يتم تمريرها من جهاز لجهاز بترتيب معين. • ال node التي معها ال token يمكنها ارسال البيانات. • Concerns عيوبها : • token overhead • latency • single point of failure (token) T (nothing to send) Link Layer T data
Summary of MAC protocols • channel partitioning, by time, frequency or code • Time Division, Frequency Division • random access(dynamic), • ALOHA, S-ALOHA, CSMA, CSMA/CD • carrier sensing: easy in some technologies (wire), hard in others (wireless) • CSMA/CD used in Ethernet • CSMA/CA used in 802.11 • taking turns • polling from central site, token passing • bluetooth, FDDI, token ring
MACaddresses and ARP • 32-bit IP address: • network-layer address for interface • used for layer 3 (network layer) forwarding • MAC (or LAN or physical or Ethernet) address: • function:used ‘locally” to get frame from one interface to another physically-connected interface (same network, in IP-addressing sense) • 48 bit MAC address (for most LANs) burned in NIC ROM, also sometimes software settable • e.g.: 1A-2F-BB-76-09-AD Link Layer hexadecimal (base 16) notation (each “number” represents 4 bits)
MAC addresses and ARP each adapter on LAN has unique MAC address 1A-2F-BB-76-09-AD LAN (wired or wireless) Link Layer adapter 71-65-F7-2B-08-53 58-23-D7-FA-20-B0 0C-C4-11-6F-E3-98
MAC addresses (more) • أعطاء ال MAC address يتم بواسطة IEEE . • اصحاب مصانع كروت الشبكة يقوموا بشراء عناوين MAC من IEEE . • MAC address: يشبه الرقم الوطني • IP address: يشبه رقم البريد • MAC flat address ➜ portability • يمكن ان تنتقل من شبكة الى شبكة اخرى بنفس عنوان ال MAC . • IP hierarchical address not portable • لا يمكن لشخص ان ينتقل من شبكة لاخرى بنفس عنوان ال IP . Link Layer
Question: how to determine interface’s MAC address, knowing its IP address? ARP: address resolution protocol ARP table: each IP node (host, router) on LAN has table • IP/MAC address mappings for some LAN nodes: < IP address; MAC address; TTL> • TTL (Time To Live): time after which address mapping will be forgotten (typically 20 min) 137.196.7.78 1A-2F-BB-76-09-AD 137.196.7.23 Link Layer 137.196.7.14 LAN 71-65-F7-2B-08-53 58-23-D7-FA-20-B0 0C-C4-11-6F-E3-98 137.196.7.88
A wants to send datagram to B B’s MAC address not in A’s ARP table. A broadcasts ARP query packet, containing B's IP address dest MAC address = FF-FF-FF-FF-FF-FF all nodes on LAN receive ARP query B receives ARP packet, replies to A with its (B's) MAC address frame sent to A’s MAC address (unicast) A caches (saves) IP-to-MAC address pair in its ARP table until information becomes old (times out) soft state: information that times out (goes away) unless refreshed ARP is “plug-and-play”: nodes create their ARP tables without intervention from net administrator ARP protocol: same LAN Link Layer
111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.222 49-BD-D2-C7-56-2A Addressing: routing to another LAN walkthrough: send datagram from A to B via R • focus on addressing – at IP (datagram) and MAC layer (frame) • assume A knows B’s IP address • assume A knows IP address of first hop router, R (how?) • assume A knows R’s MAC address (how?) Link Layer B A R 111.111.111.111 74-29-9C-E8-FF-55 222.222.222.220 1A-23-F9-CD-06-9B 222.222.222.221 111.111.111.112 88-B2-2F-54-1A-0F CC-49-DE-D0-AB-7D
MAC src: 74-29-9C-E8-FF-55 MAC dest: E6-E9-00-17-BB-4B IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.222 49-BD-D2-C7-56-2A Addressing: routing to another LAN • A creates IP datagram with IP source A, destination B • A creates link-layer frame with R's MAC address as dest, frame contains A-to-B IP datagram Link Layer B A R 111.111.111.111 74-29-9C-E8-FF-55 222.222.222.220 1A-23-F9-CD-06-9B 222.222.222.221 111.111.111.112 88-B2-2F-54-1A-0F CC-49-DE-D0-AB-7D
MAC src: 74-29-9C-E8-FF-55 MAC dest: E6-E9-00-17-BB-4B IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.222 49-BD-D2-C7-56-2A Addressing: routing to another LAN • frame sent from A to R • frame received at R, datagram removed, passed up to IP Link Layer B A R 111.111.111.111 74-29-9C-E8-FF-55 222.222.222.220 1A-23-F9-CD-06-9B 222.222.222.221 111.111.111.112 88-B2-2F-54-1A-0F CC-49-DE-D0-AB-7D
IP Eth Phy MAC src: 1A-23-F9-CD-06-9B MAC dest: 49-BD-D2-C7-56-2A IP Eth Phy IP src: 111.111.111.111 IP dest: 222.222.222.222 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.222 49-BD-D2-C7-56-2A Addressing: routing to another LAN • R forwards datagram with IP source A, destination B • R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram Link Layer B A R 111.111.111.111 74-29-9C-E8-FF-55 222.222.222.220 1A-23-F9-CD-06-9B 222.222.222.221 111.111.111.112 88-B2-2F-54-1A-0F CC-49-DE-D0-AB-7D
IP Eth Phy MAC src: 1A-23-F9-CD-06-9B MAC dest: 49-BD-D2-C7-56-2A IP Eth Phy IP src: 111.111.111.111 IP dest: 222.222.222.222 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.222 49-BD-D2-C7-56-2A Addressing: routing to another LAN • R forwards datagram with IP source A, destination B • R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram Link Layer B A R 111.111.111.111 74-29-9C-E8-FF-55 222.222.222.220 1A-23-F9-CD-06-9B 222.222.222.221 111.111.111.112 88-B2-2F-54-1A-0F CC-49-DE-D0-AB-7D
IP Eth Phy MAC src: 1A-23-F9-CD-06-9B MAC dest: 49-BD-D2-C7-56-2A IP src: 111.111.111.111 IP dest: 222.222.222.222 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.222 49-BD-D2-C7-56-2A Addressing: routing to another LAN • R forwards datagram with IP source A, destination B • R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram Link Layer B A R 111.111.111.111 74-29-9C-E8-FF-55 222.222.222.220 1A-23-F9-CD-06-9B 222.222.222.221 111.111.111.112 88-B2-2F-54-1A-0F CC-49-DE-D0-AB-7D
Questions These slides are adapted from Computer Networking: A Top Down Approach Jim Kurose, Keith RossAddison-WesleyMarch 2012