Cloud Encryption and Key Management Considerations
Cloud Encryption and Key Management Considerations. Daniel Cuschieri Information Security Distance Learning Weekend Conference August 2013. What is the Cloud?. An evolving term Many existing technologies and approaches to computing combined into something different

Cloud Encryption and Key Management Considerations
E N D
Presentation Transcript
Cloud Encryption and KeyManagement Considerations Daniel Cuschieri Information Security Distance Learning Weekend Conference August 2013
What is the Cloud? • An evolving term • Many existing technologies and approaches to computing combined into something different • Storing your data on someone else’s computer and accessing it via a network (Bruce Schneier) • A collection of services, applications, information, and infrastructure comprised of pools of compute, network, information, and storage resources that can be acquired or released as necessary (Cloud Security Alliance, 2009)
Types of Clouds (NIST, 2009)
The Cloud’s Benefits… • Cost savings • Improved flexibility • Better scalability • More focus on the core business • Higher availability • Device independence
… And It’s Concerns (KPMG Netherlands, 2010)
Cloud Threats • Generic security threats apply • Confidentiality, Integrity and Availability • Virtually unlimited Cloud compute power • Vulnerability of Cloud management interfaces • Malicious Cloud provider insiders • A shared Cloud infrastructure • Little direct control over data • Insufficient forensic and auditing information • An unknown risk profile
Encryption as a Countermeasure • Data • Cloud management • Forensics • Malicious Cloud provider insiders • Compliance • Unknown risk profile
Where to Encrypt Data • Data at rest, in transit or in use (Ponemon Institute, 2012)
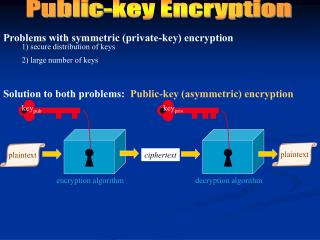
How to Encryption Data • In SaaS • Consumer encryption before data transmittal • Provider encryption after data transmittal • Third party encryption during data transmittal • In PaaS • Application-level encryption • Infrastructure-level encryption • In IaaS • Application-level encryption • Volume-based encryption
Challenges of Cloud Encryption • Encryption policies • Availability of encrypted data • Integrity of encrypted data • Encryption client security • Compliance with legislation and standards
Desirable Encryption Functionality • Processing encrypted data • Sorting encrypted data • Searching encrypted data • Encryption interoperability
Challenges of Key Management • Key generation and storage • Key availability • Key disposal and expiration • Key management policy • Separation of duties • Key management interoperability
The Future of Cloud Security • Cloud security is an issue, but measures such as encryption can address these concerns • These measures are constantly improving • Security will soon change from being a Cloud inhibitor to being one of the key enablers of Cloud adoption (Penn, 2010)
Thank you Daniel Cuschieri danielcuschieri@gmail.com