Chapter 4 – 1 The Medium Access Sublayer
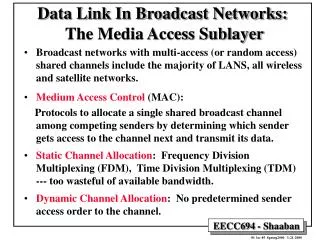
Chapter 4 – 1 The Medium Access Sublayer. Multiple Access Protocols. Broadcast Channels. Also called Multiaccess Channels Random Access Channels Determining who will use the channel next is a problem Medium Access Control (MAC) sublayer solves this problem

Chapter 4 – 1 The Medium Access Sublayer
E N D
Presentation Transcript
Chapter 4 – 1The Medium Access Sublayer Multiple Access Protocols Computer Networks 1
Broadcast Channels • Also called • Multiaccess Channels • Random Access Channels • Determining who will use the channel next is a problem • Medium Access Control (MAC) sublayer solves this problem • MAC is a sublayer (bottom part) of data link layer Computer Networks 1
Static Channel Allocation • Usually done by FDM or TDM • Not an efficient method for data traffic. E.g. • Let • The capacity of a channel be C bps • The mean time delay of the channel be T (seconds) • Frame arrival rate is a random variable from Poisson distribution with mean frames/second • Frame length is a random variable from exponential probability density function with mean 1/ bits/frame • Then • T = 1 / (C - ) (result from queuing theory) • Now, let the channel be divided into N subchannels with capacity C/N and mean input rate /N • TFDM= 1 / ((C/N) – (/N) = N / (C - ) = NT • The mean delay is N times worse Computer Networks 1
Dynamic Channel Allocation Assumptions 1 • Station Model • Generates frames at a rate of frames/unit time (Frame generation is Poisson Distribution) • Once a frame is generated, the station is blocked until the frame is successfully transmitted • Single Channel Assumption • All stations transmit and receive with equal priority over a unique channel Computer Networks 1
Dynamic Channel Allocation Assumptions 2 • Collision Assumption • Overlapping transmission by two or more stations at the same time garbles the frames (collision) • All stations detect collisions • There are no errors other than those generated by collisions • Continuous Time • Frame transmission can begin at any instant • Slotted Time • Time is divided into slots • Frame transmission always begins with a slot Computer Networks 1
Dynamic Channel Allocation Assumptions 3 • Carrier Sense • Stations can tell if the channel is in use • LANs generally have carrier sense • No Carrier Sense • Stations can not sense the channel before trying to use it • Satellite networks do not have carrier sense Computer Networks 1
Pure ALOHA • Users transmit any time • If there is collision • sender knows about it after a certain time, • waits random amount of time, • sends the frame again • Contention systems • Systems in which multiple users share a common channel in a way that can lead to conflicts • To maximize throughput, frames have uniform size Computer Networks 1
Frames in Pure ALOHA Computer Networks 1
ALOHA Assumptions • Frame time=time to transmit one frame • Number of frames generated in a frame time is a Poisson Distribution with mean N. • If N>1, every frame will suffer a collision • 0<N<1 is reasonable • Probability of k transmission attempts in a frame time is Poisson with parameter G. Pr[k]=Gk e-G/k! • For small N, G N • For large N, G>N Computer Networks 1
ALOHA cont’d • P0 = probability that a frame does not suffer a collision • S = Probability of a transmission succeeding • S = G P0 Computer Networks 1
ALOHA Frame Collision Period Computer Networks 1
Efficiency of ALOHA • Referring to Fig 4-2, the vulnerable period is two frame times • The probability that no frame is transmitted during this period is e-2G • Pr[0]=e-G in one frame period so P0=e-2G in two frame periods • Therefore S = G e-2G • The maximum of S occurs at G=0.5, S=1/2e Computer Networks 1
ALOHA Throughput Computer Networks 1
Slotted ALOHA 1 • Can only transmit at the beginning of a slot • Vulnerable period is halved • Hence S = G e-G • S peaks at G = 1 • Probability that a frame avoids a collision is e-G • The probability of a collision is 1-e-G • Probability of a transmission requiring exactly k attempts is Pk=e-G(1-e-G)k-1 Computer Networks 1
Slotted ALOHA 2 • Expected number of transmissions, E, per each created frame is E = k Pk = ke-G(1-e-G)k-1= d/dG(1-e-G)k = k=1 k=1 k=1 d/dG (1-e-G)k = d/dG eG = eG k=1 • Conclusion: Performance exponentially degrades by the load Computer Networks 1
Carrier Sense Multiple Access (CSMA) Protocols • ALOHA does not listen to the channel before it transmits, ending up with poor performance • Carrier Sense Protocols • Stations listen the channel if there is any transmission going on before they transmit Computer Networks 1
Persistent and Nonpersistent CSMA • 1-persistent CSMA • Stations transmit with probability 1 whenever they find the channel idle • Nonpersistent CSMA • If the channel is idle before the first attempt, transmit • If the channel is already in use, wait for a random amount of time, and then listen to the channel for transmission • P-persistent CSMA • Applies to slotted channels • If the channel is idle, • transmit with probability p • Defer transmission until the next slot with probability q = 1 – p • If, in the mean time, someone else transmits, wait a random time • If channel busy • Wait for the next slot Computer Networks 1
Channel Utilization for Random Access Protocols Computer Networks 1
CSMA with Collision Detection (CSMA/CD) • collision Detection • Abort transmission as soon as detect collision • If is the time the signal propagates between two farthest stations, the station has to wait 2 to make sure that no collision has occurred • CSMA/CD model has contention, transmission and idle periods • Contention period is modeled as a slotted ALOHA with slot size 2 Computer Networks 1
CSMA/CD States Computer Networks 1
Collision-Free Protocols • Assumptions • There are N stations • Each station has a unique address (0 to N-1) hardwired to it • Question • Which station gets the channel after a successful transmission? Computer Networks 1
A Bit-Map Protocol (Reservation Protocol) • Two rounds of transmission cycle • First Round (Contention Period) • Consists of N slots each reserved for a particular station • In this period, each station transmits • 1 if it has a frame to transmit • 0 if it has no frame to transmit • At the completion of the first round everybody knows who wants to transmit • Second Round (Transmission Period) • Stations transmit according to the order formed in the first round • There will not be any collisions Computer Networks 1
The basic bit-map protocol Computer Networks 1
Reservation Protocol Performance :Binary Countdown • Each station has a binary station address • A station wanting to transmit broadcasts its address starting with the high-order bit • The bits from each station are boolean Or’ed • Arbitration Rule • As soon as a station sees that a high-order bit position that is 0 in its address is overwritten by 1, it gives up • Channel Efficiency is d/(d+log2N) • If station address is the first field in the frame then efficiency is 100%. Computer Networks 1
Binary Countdown Example Computer Networks 1
Wavelength Division Multiple Access (WDMA) Protocols • All optical LANs divide the spectrum into wavelength bands • Each station is assigned two channels • Narrow channel: Control channel to signal the station • Wide channel: Station outputs data frames • Narrow channel is divided into m time slots • Wide channel is divided into n+1 slots • n for data output • 1 for status (to indicate which slots on both channels are free) Computer Networks 1
WDMA 2 Computer Networks 1
WDMA 3 • Both connection-oriented and connectionless traffic is supported • Each station has: • A fixed-wavelength receiver for listening to its own control channel • A tunable transmitter for sending on other station’s control channel • A fixed-wavelength transmitter for outputting data frames • A tunable receiver for selecting a data transmitter to listen to Computer Networks 1
WDMA Connection Setup Procedure • A tunes its data receiver to B’s data channel and waits for the status slot to learn about a free B control slot (on 4 of A) • A chooses a free control slot and sends a CONNECTION REQUEST (on 2 of A) • B assigns a data slot to A by announcing it in the status slot (on 3 of B, B also tunes 4 to A’s 3) • A reads this announcement and a unidirectional connection from A to B is established (A transmits on 4 in the slot assigned by B) • If the request was for two way communications, B would repeat the same procedure Computer Networks 1