COMPUTER NETWORKS Data-link Layer (The Medium Access Control Sublayer)
MAC Sublayer. COMPUTER NETWORKS Data-link Layer (The Medium Access Control Sublayer). MAC Sublayer. Questions to be answered ? In broadcast networks, How the channel is divided between competing users? What is Medium Access Control (MAC)?

COMPUTER NETWORKS Data-link Layer (The Medium Access Control Sublayer)
E N D
Presentation Transcript
MAC Sublayer COMPUTER NETWORKS Data-link Layer (The Medium Access Control Sublayer)
MAC Sublayer • Questions to be answered ? • In broadcast networks, How the channel is divided between competing users? • What is Medium Access Control (MAC)? • What protocols are used for allocating a multiple access channel ? Computer Networks
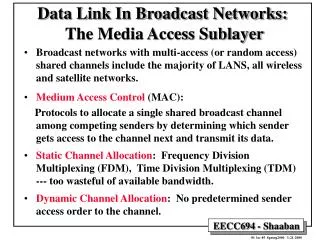
MAC Sublayer • the need for determine who gets to use the channel • When there are two ormore users trying to use a shared single channel there should be an algorithm to control this access. • This problem occurs in broadcast networks which are known as multiaccess channels. Computer Networks
MAC Sublayer • What is MAC? • Medium Access Control (MAC) is a sublayer of the Data-link layer. • The protocols used to determine who goes next on a multiaccess channel belongs to a MAC sublayer. • MAC is important in LAN which use a multiaccess channel as the basis for communication. Computer Networks
MAC Sublayer • The Channel Allocation Problem • There are two schemes to allocate a single channel among competing users: • Static Channel Allocation. • 2) Dynamic Channel Allocation Computer Networks
MAC Sublayer • Static Channel Allocation: • In this scheme a Frequency Division Multiplexing (FDM) is used for allocating a single channel among competing users. • Example • if we have N users, the bandwidth will be divided into N equal-size portions. • ++ FDM is a simple and efficient allocation mechanism. • - -Waste of resources when the traffic is bursty, or the channel is lightly loaded. Computer Networks
MAC Sublayer • Dynamic Channel Allocation: • Before the discussion of algorithms used for dynamic allocation we need to consider the following assumptions. • Station Model: N independent stations generate frames for transmission. (Generate >Block >Transmission) • Single channel Assumption: Single channel is available for all communication. • Collision Assumption • Continuous Time, or Slotted Time • Carrier Sense, or No Carrier sense Computer Networks
MAC Sublayer • Multiple Access Protocols: • - ALOHA is a system proposed for solving the channel allocation problem. • there are two versions of ALOHA: • Pure ALOHA; 2) Slotted ALOHA • The basic difference with respect to timing is: • Pure ALOHAdoes not requireglobal time synchronization; • Slotted ALOHA does Computer Networks
Pure ALOHA In pure ALOHA, frames are transmitted at completely arbitrary times.
MAC Sublayer • Pure ALOHA • The system is working as follows: • 1- let users transmit whenever they have data to be sent. • 2- expected collisions will occur. • 3- the collided frames will be destroyed. • 4- using a feedback mechanism to know about the status of frame. • 5- retransmit the destroyed frame. Computer Networks
Pure ALOHA (2) Vulnerable period for the shaded frame.
MAC Sublayer • Pure ALOHA • The main disadvantage of Pure ALOHA is a low channel utilization. • This is expected due to the feature that all users transmit whenever they want. Computer Networks
Pure ALOHA (3) Throughput versus offered traffic for ALOHA systems.
MAC Sublayer • Slotted ALOHA • In this method the proposal was to divide the time into discrete intervals each interval corresponding to one frame. • In Slotted ALOHA, a computer can not send anytime, instead it is required to wait for the beginning of the time slot. • The big advantage of Slotted ALOHA is the increase in channel utilization. Computer Networks
MAC Sublayer • Slotted ALOHA • There is a limit for the best channel utilization using Slotted ALOHA. • To reduce the chance of collisions the station should be able to detect what other stations are doing. • In LAN networks this is possible, therefore they can achieve better utilization than Slotted ALOHA. • Carrier Sense Protocols are protocols in which stations listen for a carrier. Computer Networks
MAC Sublayer • Carrier Sense Multiple Access (CSMA) Protocols • There are several versions of carrier sense protocols: • 1-persistent CSMA • Non-persistent CSMA • P-persistent CSMA • CSMA with Collision Detection (CSMA/CD) Computer Networks
MAC Sublayer • Carrier Sense Multiple Access (CSMA) Protocols • - In 1-persistent CSMA, a station prior to send data it listen to the channel to see if anyone else is transmitting at that moment. • if the channel is busy, the station waits until it becomes idle. • If the channel is idle, the station transmits a frame. • If a collision occurs, the station waits a random amount of time and starts all over again. Computer Networks
MAC Sublayer • Carrier Sense Multiple Access (CSMA) Protocols • Although this protocol has disadvantages, it is better than ALOHA and Slotted ALOHA • -- 1) It’s performance depends on the propagation delay. • -- 2) There is a chance when two stations start transmission at the same time. Computer Networks
MAC Sublayer • Carrier Sense Multiple Access (CSMA) Protocols • In Non-persistent CSMA a station makes conscious attempt to sense the channel. • After the first attempt, if the channel is idle, it sends, however, if the channel is already in use, it waits a random period of time and repeats the algorithm. • (+ -)This algorithm has better utilization but longer delays than 1-persistent CSMA. Computer Networks
MAC Sublayer • Carrier Sense Multiple Access (CSMA) Protocols • In p-persistent CSMA a station transmits if the channel is idle with a probability p and with probability q=1-p it waits until the next slot. Computer Networks
MAC Sublayer • Carrier Sense Multiple Access (CSMA) Protocols • The main advantage of persistent and non-persistent over ALOHA is that they ensure no station begins to transmit when it senses the channel busy. Computer Networks
MAC Sublayer • CSMA with Collision Detection • It is important that stations should terminate transmission as soon as they detect a collision. • This protocol is called CSMA/CD. • It is widely used on LANs in the MAC sublayer. • It is the basis of the popular Ethernet LAN. Computer Networks
CSMA with Collision Detection CSMA/CD can be in one of three states: contention, transmission, or idle.
MAC Sublayer • CSMA with Collision Detection • A collision can be detected by looking at the power or pulse width of the received signal and comparing it to the transmitted signal. • After a station detects a collision it terminates its transmission, waits a random period of time, and then tries again, assuming that no other station has started transmitting in the meantime. Computer Networks
MAC Sublayer • CSMA with Collision Detection • Collision detection is an analog process. Therefore, special encoding is commonly used. • A sending station must continually monitor the channel, listening for noise bursts that might indicate a collision. For this reason, CSMA/CD with a single channel is inherently a half-duplex system. Computer Networks