electronic data security
To start the presentation, click on this button in the lower right corner of your screen. The presentation will begin after the screen changes and you press enter . electronic data security. in human subjects research. Electronic data security. hacking theft lost equipment.

electronic data security
E N D
Presentation Transcript
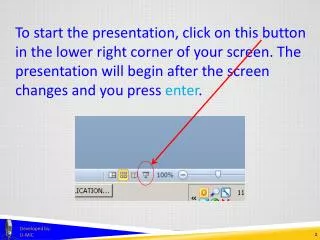
To start the presentation, click on this button in the lower right corner of your screen. The presentation will begin after the screen changes and you press enter. Developed by: U-MIC
electronicdata security in human subjects research Developed by: U-MIC University of Michigan IRB Collaborative
Electronic data security • hacking • theft • lost equipment Developed by: U-MIC
Office of Human Research Compliance Review (OHRCR) recommendations for Electronic data security best practices Developed by: U-MIC
Office of Human Research Compliance Review (OHRCR) recommendations for Electronic data security • collect only the data you need • deidentify as soon as possible Developed by: U-MIC
Office of Human Research Compliance Review (OHRCR) recommendations for Electronic data security • separate identifying information from research data • use encryption software Developed by: U-MIC
Office of Human Research Compliance Review (OHRCR) recommendations for Electronic data security • restrict access • use machines managed by IT • collect • store • process • transmit Developed by: U-MIC
Office of Human Research Compliance Review (OHRCR) recommendations for Electronic data security • avoid portable devices • use encryption software Developed by: U-MIC
Office of Human Research Compliance Review (OHRCR) recommendations for Electronic data security delete identifying information Developed by: U-MIC
Information and Technology Services (ITS) recommendations for Electronic data security while traveling • use a loaner machine • bring only necessary machines and data • create a temporary password Developed by: U-MIC
Information and Technology Services (ITS) recommendations for Electronic data security while traveling • create a data inventory • leave a back-up behind • implement full-disk encryption Developed by: U-MIC
Information and Technology Services (ITS) recommendations for Electronic data security while traveling • avoid public internet networks • virtual private network (VPN) http://www.itcom.itd.umich.edu/vpn/ Developed by: U-MIC
Information and Technology Services (ITS) recommendations for Electronic data security while traveling • keep machines with you • password-lock Developed by: U-MIC
Information and Technology Services (ITS) recommendations for Electronic data security while traveling • if a machine is lost or stolen • contact authorities • change passwords • security@umich.edu Developed by: U-MIC
Electronic data security Information Technology Services (ITS) http://www.itcs.umich.edu/ Medical School Information Services (MSIS) https://www.umms.med.umich.edu/msis/home/index.php Medical Center Information Technology (MCIT) http://www.itcom.itd.umich.edu/umnoc/mcit-help.php Office of Human Research Compliance Review (OHRCR) http://www.ohrcr.umich.edu/ Developed by: U-MIC
Brian Seabolt IRBMED thank you. Developed by: U-MIC