Enhancing User Privacy: Preventing Query Association Attacks
This document discusses the vulnerability of user requests to query association attacks, where attackers can infer sensitive attributes. It presents two effective methods to mitigate these risks: many-to-one and many-to-many queries. Key techniques include k-anonymity, l-diversity, and t-closeness, which help ensure that user data is sufficiently obfuscated. These frameworks guarantee that users cannot be linked to fewer than ℓ distinct values of service attributes, enhancing privacy by making it difficult to track individual users based on location or service usage patterns.

Enhancing User Privacy: Preventing Query Association Attacks
E N D
Presentation Transcript
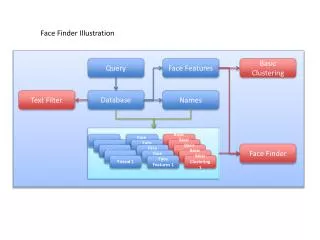
Query homogeneity attacks • Problem: • The attacker want to infer information from the sensitive attribute(s) involved in a user’s request => query association
Two methods to prevent query association: • Many-to-one queries: a k-anonymous cloaking region <-> single service attribute => k potential users who may be the owner of the service attribute • Many-to-many queries: a cloaking region <-> a set of service attribute values (ones belonging to the users inside the region)
l-diversity • Query l-diversity: ensures that a user cannot be linked to less than ℓ distinct service attribute values. equivalence class (EC)
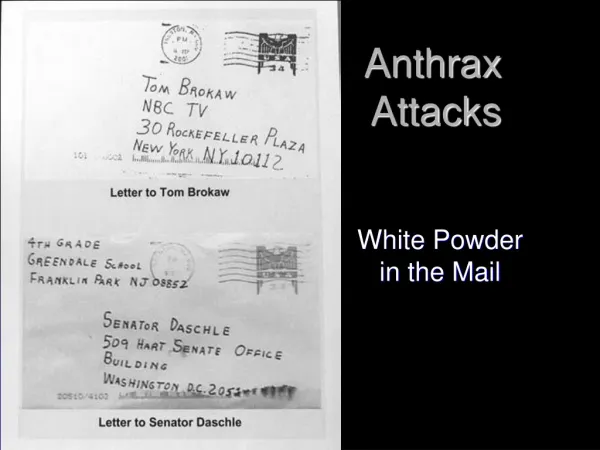
t-closeness all disease is stomach problem
l-diversity & t-closeness • Satisfying location k-anonymity • Satisfying query ℓ-diversity • Satisfying query t-closeness query 3-diverse and location 3-anonymous
m-Invariance • Query m-Invariance: the number of possible query association attacks will increase if a user can be associated with more number of service attribute values.