Web Application Security Implementation
In response to a recent security incident involving a website vulnerability that compromised customer data, a rapid web application security assessment program is mandated. This program includes conducting a comprehensive audit of web servers and applications through automated vulnerability scans and manual audits. Key deliverables will be presented to senior management, outlining an inventory of assets, identifying common vulnerabilities, and providing actionable recommendations to strengthen security measures and prevent future incidents.

Web Application Security Implementation
E N D
Presentation Transcript
Web Application Security Implementation SANS MSISE GDWP Kevin Bong John Brozycki July 26, 2007
Introduction • Website vulnerability used to copy customer data to foreign host. • Senior management to acquire services of penetration team. Not available for immediate needs. • Post incident,we are tasked with creation of a web application security assessment program, to implement within a few days.
Web Assessment Process Manual Web Server Audit Inventory Conduct Interviews Automated Vulnerability Scan Report Findings Manual Web Application Audit
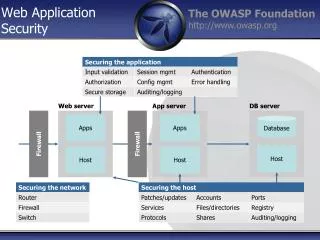
Web Service Inventory • Need to know what is legitimate and necessary. (Programs, services, ports) • Need to know where the data lives and how it is accessed. • Rate assets (web servers/services) to focus resources and set priorities.
Performing Automated Scans • Verify the inventory by confirming the existence of services. • Identify additional, unneeded processes and check for common vulnerabilities and misconfigurations for both the necessary and unnecessary processes and services. • Quickly identify the low hanging fruit.
Manual Audit of Web Server Security • Review if best practices are followed • Is defense in depth employed? • Configuration of web server and web development frameworks • User and service accounts and rights • Error messages, other information leakage • Do log files store appropriate information? • Review change processes for ports and services through interviews
Manual Audit of Web Applications • Based on inventory, focus on potentially vulnerable code • Specific tests to be performed against each dynamic page • Interview developers to determine if processes prevent new vulnerabilities
Deliverables for the Senior Management Team • Reports and recommendations delivered within days. • Results of inventory, scans, and manual audits used to provide action items that can be given to implementation team. • Additional recommendations from tiger team to management to minimize reoccurrences.