Multi Kingdom AAA Security using Kerberos v5
120 likes | 263 Vues
Multi Kingdom AAA Security using Kerberos v5. Kaushik Narayan. Kerberos Operation. Associations and Contexts. Association is relationship between two communication endpoints. Contexts consist of specific context attributes that are used to establish, maintains and release associations.

Multi Kingdom AAA Security using Kerberos v5
E N D
Presentation Transcript
Multi Kingdom AAA Security using Kerberos v5 Kaushik Narayan
Kerberos Operation HCL Cisco Offshore Development Center
Associations and Contexts • Association is relationship between two communication endpoints. • Contexts consist of specific context attributes that are used to establish, maintains and release associations. • Context operations. • Context attributes. • Negotiation attributes. HCL Cisco Offshore Development Center
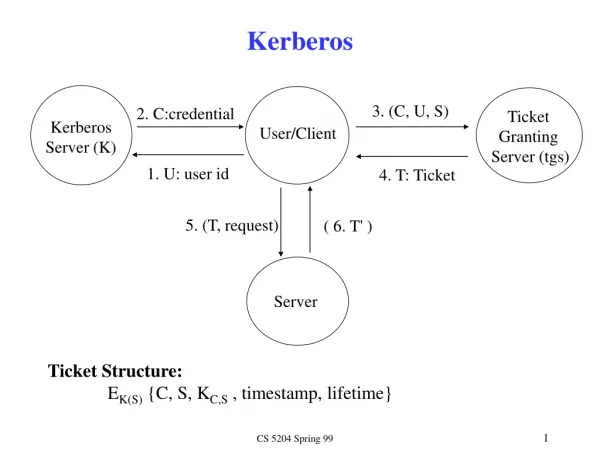
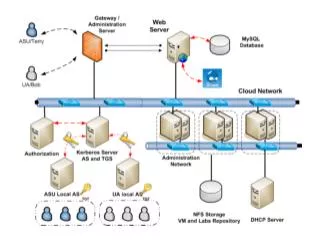
Kerberos Security Contexts • Security contexts cover only the Kerberos application exchange and not the communication with the KDC. • Kerberos session keys form the context attributes which can be employed by AAA servers for creating a secure communication channel. • An authentication transaction is a pre-requisite. HCL Cisco Offshore Development Center
Modes of Operation • End to End mode. • Hop by Hop mode. • End to End and Hop by Hop mode. • Any to Any mode HCL Cisco Offshore Development Center
End to End mode Kingdom4 Kingdom1 Kingdom3 Kingdom2 AAA Server AAA Server AAA Server AAA Server AAA exchanges Kerberos End to End Security Context HCL Cisco Offshore Development Center
Hop by Hop Mode Kingdom4 Kingdom1 Kingdom3 Kingdom2 AAA Server AAA Server AAA Server AAA Server AAA exchanges Kerberos Hop by Hop Security Context HCL Cisco Offshore Development Center
End to End with Hop by Hop Kingdom4 Kingdom1 Kingdom3 Kingdom2 AAA Server AAA Server AAA Server AAA Server AAA exchanges Kerberos Hop by Hop Security Context Kerberos End to End Security Context HCL Cisco Offshore Development Center
Any to Any Mode Kingdom4 Kingdom1 Kingdom3 Kingdom2 AAA Server AAA Server AAA Server AAA Server AAA exchanges Kerberos Hop by Hop Security Context Kerberos End to End Security Context HCL Cisco Offshore Development Center
Dependency on Data Modeling • Capabilities of intermediate AAA servers needs to be defined. • There needs to be a model that defines data that intermediate AAA servers with different capabilities need to inspect or modify in different application scenarios. • Use of attribute policies is an alternative. HCL Cisco Offshore Development Center
Capabilities Discovery • The source AAA server needs to have the knowledge of the kingdoms that the request must traverse. • Needs to discover capabilities of AAA servers in each of these kingdoms. • Topology knowledge is not required. HCL Cisco Offshore Development Center
Sessions • The authentication transaction would perform the Kerberos AS and TGS exchange. • Kerberos anonymous tickets can be employed to create kerberos security contexts with intermediate kingdoms. • Multiple security contexts can be created and destroyed by AAA servers during the lifetime of the main session. • Security contexts operations would form a session and these security context sessions would be sub-sessions of the main session. HCL Cisco Offshore Development Center