Effective WEB isolation
SafeExplorer offers effective web isolation, protecting your corporate environment from unknown online threats. By defining a trusted web policy and enforcing browser usage, you can automatically distribute web policies across your enterprise. With web browsing being a necessity for both government and private sectors, SafeExplorer ensures productivity without compromising security. It isolates browser instances in secure compartments, preventing malware from infiltrating your system. Experience the confidence of safe browsing; contact us for a free trial today!

Effective WEB isolation
E N D
Presentation Transcript
Safexplorer Effective WEB isolation Separate your corporate environment from unknown threats of the WEB. Define trusted WEB policy. Enforce the use of WEB browsers. Automatically distribute WEB policies across your enterprise.
WEB as a Necessity • Today government institutions and private businessescannot imagine their functioning without using WEB. It increases the productivity of everyday’s work and brings endless new possibilities. • At the same time Internet is a home of unknown threats – exploits, worms, viruses and anything else which has not yet been encountered.
Always unknown threat • On practice severe vulnerabilities of the WEB browsers are discovered and fixed every year. • Methods of penetration are constantly evolving and variations of malware and viruses increasing dramatically. • Fixes and antivirus patches are often coming too late and sometimes are hopeless in detection. • The conclusion is evident: • Use of WEB browsers can never be completely risk-free.
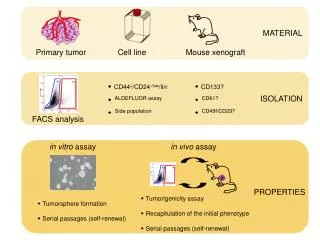
Browser separation on the fly The SafeExplorertechnology automatically wraps a WEB browser process in an isolated “compartment”. “Isolated” browser instancesare easily identifiable by corresponding markers. Such an instance of the browser process is running in its own environment, separated from actual user environment.
Browser separation on the fly “Isolated” browser instances are separated from: • Local, removable and network drives • User profile data and documents • Printers (optionally) • Other programs and system components running on the user desktop
Browser separation on the fly Thus viruses or unwanted software have no chance to infiltrate the rest of the system or spy over user data. The isolated “compartment” is reset at the end of the session, restoring itself to an initial clean state.
No limitations for trusted sites The automatic isolation of WEB browsers is turned off for “approved” WEB locations. Browser instances accessing these URLs will function as usual, without the access limitations. Approved Other
Designed for confidence Safexplorer • Guarantees full confidence in WEB browsing by effectively blocking the unknown threats of the Internet. For today and the future. • Allows quick centralized rollout across the enterprise with further configuration through company security policies. • Is compatible with all versions of Windows and most popular browsers. • Contact us to start a free trial. • www.securesystems.lv