Users
Users. Greg Porter V1.0, 26 Jan 09. What is a user?. Users “own” files and directories Permission based on “ownership” Every user has a User ID (UID) Unique numeric user identifier Every user must belong to at least one group Groups have a Group ID (GID) Unique numeric group identifier


Users
E N D
Presentation Transcript
Users Greg Porter V1.0, 26 Jan 09
What is a user? • Users “own” files and directories • Permission based on “ownership” • Every user has a User ID (UID) • Unique numeric user identifier • Every user must belong to at least one group • Groups have a Group ID (GID) • Unique numeric group identifier • Every file and directory is marked with a UID and GID
“Special” users • The user named “root” is special • UID 0 (zero) • Can access any file, regardless of UID or GID • Either you’re root, or you’re not • Used for admin purposes, not for “normal” use • Easy to trash things with the root account • Some programs run as non-human users • “Daemons” are services like print servers, web servers • An apache web server might run as the user “apache” • Daemons don’t log in • The users bin, sys, and nobody are other common system users
Where user information is kept • The /etc/passwd file • Plain text file in /etc User:Password:UID:GID:GECOS:Home:Shell yyang:x:502:1234:Ying Yang:/home/yyang:/bin/bash • User: text name of user, usually all lower • Password: no longer used, ‘x’ means see /etc/shadow • UID: some number, unique • GID: primary group of user • GECOS: text field for user info, name, phone number, etc. • Home: user’s home (log in) directory • Shell: program that is executed upon login
Passwords • Used to be stored in /etc/passwd • Publicly readable • Stored as a encrypted “hash” • With today’s fast CPU’s, easy to crack • Most systems today ‘shadow’ password hashes • Hashes stored in /etc/shadow • Not publicly accessible, only root has read • Plain text file yying:$2$H871LCBM$Uik4a32i/fs7wBd0SVfpU/:14052:0:99999:7::: • Fields following the hash related to password aging
Groups • Group information stored in /etc/group • Plain text file Name:Password:GID:Members users:x:1234:joe,mama,sam • Name: text group name • Password: optional, rarely used, allows non-members to join group • GID • Members: comma separated list
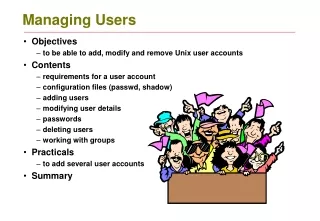
User management • Command line tools, fast and scriptable • If you use the tools, you won’t screw up /etc/passwd • passwd, change a password • useradd, add a user • userdel, delete a user • usermod, modify a user • groupadd, add a group • groupdel, delete a group • groupmod, modify a group
Becoming root or someone else • Don’t log in as root, if possible • Dangerous, easy to break things • Better is to “switch user” or “set user” to root • /bin/su with no argument assumes root • You’ll need root’s password • Use su to become other users, as well • Even better is to use “superuser do”, sudo • sudo <command> runs command as root • sudo will ask for *YOUR* password • Add sudoers to /etc/sudoers • Install “sudo shell”, ss and get a root shell that’s logged
User shells • Program specified for each user in /etc/passwd • For human users, usually is a command interpreter, a “shell” • Can be any arbitrary file, daemons might have strange ones • One of the original shells was the “Bourne shell”, /bin/sh • The usual shell on Linux systems is the “Bourne Again Shell”, /bin/bash, a superset of /bin/sh
More on /bin/bash • Command line interface to system • Can launch other programs • Can control programs after launch • Comes with built in commands • More or less a complete programming interface • /bin/bash programs called ‘scripts’ "Nobody really knows what the Bourne shell's grammar is. Even examination of the source code is little help." – Tom Duff