Software Infrastructure for Electronic Commerce Computer Security Principles
Software Infrastructure for Electronic Commerce Computer Security Principles. Professor Fred B. Schneider Dept. of Computer Science Cornell University. Goals. Develop a framework for thinking about computer security. Introduce the vocabulary used by practitioners.

Software Infrastructure for Electronic Commerce Computer Security Principles
E N D
Presentation Transcript
Software Infrastructure forElectronic CommerceComputer Security Principles Professor Fred B. Schneider Dept. of Computer Science Cornell University
Goals • Develop a framework for thinking about computer security. • Introduce the vocabulary used by practitioners. • Understand what existing computer security technology can and cannot accomplish.
Security: Pre-Cyberspace Security is all about ... • value • locks • police and courts • Locks must be good enough to prevent the “bad guys” from breaking in too often. • Some “bad guys” are caught. • Police and courts convict often enough to discourage break-ins.
Locks in the “real world” • Must not be annoying or they won’t be used. • All locks aren’t the same. They are: • Scaled for what they are protecting. • Scaled for their environment. • Police and courts are central---not the locks! We expect security breaches. • Tracking down the “bad guys” is what’s central. • Locks reduce temptation and reduce workload on police and courts.
The big picture • People only pay for security that they think they need. … need is based on personal experience & others experiences. • People avoid annoying locks by buying insurance. • Risk avoidance versus risk management. • Externalities is a wrinkle! • Security is holistic… • Security is only as strong as the weakest link. • Making any link stronger than the weakest link doesn’t much improve security.
Security: In Cyberspace Terminology: vulnerability: Weakness that can be exploited to cause damage. attack: Method of exploiting a vulnerability. threat: Motivated capable adversary who will mount attacks. All systems have vulnerabilities. We must understand the threats and defend against attacks they can mount.
Cyber threats • Operator/user blunders. • Hackers driven by intellectual challenge (or boredom). • Insiders: employees or customers seeking revenge. • Criminals seeking financial gain. • Organized crime seeking gain or hiding criminal activities. • Organized terrorist groups or nation states trying to influence national policy. • Foreign agents seeking information for economic, political, or military purposes. • Tactical countermeasures intended to disrupt military capability. • Large organized terrorist groups or nation-states intent on overthrowing the US government.
What do we protect in cyberspace? Attacks compromise: • Secrecy (confidentiality) causing improper disclosure of information. … But what constitutes a secret, anyway? • Integrity causing improper alteration of information. • Availability causing service outages.
Security: In Cyberspace (con’t) Security is all about ... • value • locks • police and courts • Locks: authorization or access control mechanisms. • Locks have keys. • Keys are authentication mechanisms … something you have, know, or are. • Police and courts: same as before. • Need authentication for audit information.
Computer Security Gold Standard • Authentication • Authorization • Audit (N.B. Au is the chemical symbol for Gold.)
Lock Design • Security mechanisms are an integral part of your systems software. • Difficult to improve or to change. • Technical details are boring. • We discuss principles that underlie all: • Assurance Principles. • Functionality Principles.
Lock Design: Assurance Economy of Mechanism: Use small and simple mechanisms where possible. Consequences: • Fewer errors in implementation because simpler. • Easier to analyze for yourself.
Lock Design:Assurance Principles Open Design: Security of a mechanism should not depend on an attacker’s ignorance of the design. A. Kerckhoffs Principle (1883): The security of a cryptosystem must not depend on keeping the algorithm secret. No security by obscurity. Consequences: • Increased assurance if many critics. • Reduced cost of recovering from key compromise.
Lock Design:Assurance Principles: Open Design? Open Design is controversial. With open design: • Attackers job is easier because design is available. • Analysis tends to concentrate on certain “main code”. Vulnerabilities off the beaten path remain. • Flaws are not always revealed.
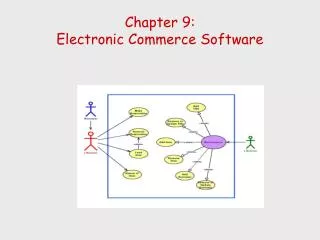
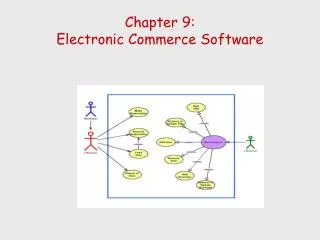
Lock Design:Functionality Principles What should the lock do? Must distinguish policy from mechanism. Desire mechanisms that implement many policies. certificate revocation lists digital signatures access control lists capabilities public key cryptosystem
Some Security Policies Discretionary access control: • Owner controls access to objects. • E.g, Windows NT: Properties>Security>Permissions • Does not rule out “trojan horse” attacks.
Some Security Policies • Mandatory Access Control Allows a subject to: • Read less-classified document. • Write more-classified document. Requires declassification! topsecret secret classified unclassified
Some Security Policies • Clark-Wilson Commercial Policies • Well-formed Transactions: • E.g. double-entry bookkeeping • E.g. log all shipments • Separation of Duty: • E.g. auditor vs controller
Lock Design:Functionality Principles Principle of Least Privilege: A task/process/user is accorded the minimum set of privileges needed to get the job done. Consequences: • Limits Damage that can result from attack or error. • Limits number of programs that can be compromised to effect an attack. • Helps with debugging. Example: super-user or admin privileges.
Lock Design:Functionality Principles Corollary of Principle of Least Privilege: Complete Mediation: Every access to every object is checked. Some implicit assumptions: • Some interface is being monitored. • Mediation mechanism cannot be compromised.
Lock Design:Functionality Principles Corollary of Principle of Least Privilege: Failsafe Defaults: Access decisions are based on the explicit presence of permissions rather than their absence of explicit prohibitions. Safe way to tolerate administrative oversight.
Lock Design:Functionality Principles Corollary of Principle of Least Privilege: Separation of Privilege: Each “lock” should require a separate “key”. Consequences: • Allows fine-grained control and therefore supports PoLP with higher fidelity. • Can be a sys admin nightmare.
Where to Deploy Locks Axiom: Every system has vulnerabilities! Consequently… • Employ multiple lines of defense. … this is just Separation of Privilege! • Employ diversity of mechanism. … diverse mechanisms are unlikely to share vulnerabilities.
Deployment Strategies • [Isolationism] Keep everyone out. • Cyber-security (hard) reduced to physical security (easy). • But… no sharing of information or services.
Deployment Strategies • [Exo-security] Keep bad guys out. • Firewalls. • Code signing. Perimeter defense… but no internal defense: • Insider attacks possible. • B2B e-commerce difficult. • Precludes foreign code/extensible systems.
Deployment Strategies • [Pervasive Security] Prevent anyone who gets in from doing damage. • Need PoLP mechanisms. • Must manage access rights---admin nightmare. • [Retaliatory Security] Let anyone in; recover from any damage. • Need audit: • Intrusion detection. • Need recovery.
Intrusion Detection Monitor for: • Activity/code that matches attack behavior. • Activity that does not match “normal” behavior. • Flawed in theory. • Useful in practice.
In summary … • Q: What’s security all about? • A: Value, locks, police & courts! • Vulnerabilities allow Attacks by Threats • Gold Standard: authentication, authorization, audit. • Policy versus Mechanism! • Important Principles: • Economy of Mechanism (=Keep it simple) • Open Design (=Keep it public) • Complete Mediation (=Keep holding the reins) • Least Privilege (=Keep the reins tight)