RSA
RSA. RSA COSC 201 St. Mary’s College of Maryland Fall 2012. Public Key Encryption. Bob wants to send Alice a super secret message. How? Alice generates 2 keys – a public encryption key and a private decryption key. Bob takes the encryption key, encodes the message, then sends it to Alice.

RSA
E N D
Presentation Transcript
RSA RSA COSC 201 St. Mary’s College of Maryland Fall 2012
Public Key Encryption Bob wants to send Alice a super secret message. How? Alice generates 2 keys – a public encryption key and a private decryption key. Bob takes the encryption key, encodes the message, then sends it to Alice. Alice then can decrypt the message. No one else can decrypt the message.
RSA How hard to crack is this kind of encryption – let’s take an example: 94021
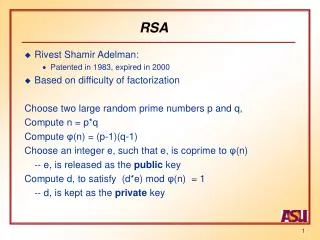
Four Problems • At the core of RSA are four problems: • Modular Exponentiation – compute xn (mod P) • GCD • Multiplicative inverse: solve AX ≡ 1 (mod P) for X • Primality testing
The Algorithm • The receiver chooses two large primes p and q. • p = 127, q = 211 • Compute N = pq and N’ = (p-1)(q-1) • N = 26797, N’ = 26460 • Choose some e > 1 s.t. gcd(e, N’) = 1 • e = 13379 • Compute d, the multiplicative inverse of e, mod N’ • d = 11099 • The receiver then destroys p, q, and N’. Transmit e and N, keep d a secret. • Encrypting – sender computes Me (mod N) and sends. M is the message. • Decrypting – compute Rd (mod N)
Computing Modular Exponentiation Solution 0 – do what it says. Do the exponentiation, then mod it by P. Solution 1 – start with a result, multiply by X, then mod by P – keep going until we’ve done this N times. Solution 2 – observe that if N is even – xn = (x*x)⎣n/2⎦, if N is odd – xn = x * (x*x) ⎣n/2⎦ public static long modpower(longx, long n, long p){ if (n == 0) return 1; long tmp = modpower((x*x) % p, n/2, p); if (n%2 != 0)tmp = (tmp*x) % p; return tmp;}
Computing GCD • Solution 1 – Euclid’s Algorithm – efficient, recursive, and 2300 years old. • Subtract B from A continuously until A becomes less than B, then switch. Continue until B becomes 0. A is the gcd. • Solution 2 – leverage modulus: • public long gcd (long a, long b){ if (b == 0) return a; return gcd(b, a%b);}
Compute Multiplicative Inverse Basically, given A and N, solve for X where AX % N == 1 % NHow to solve – leverage GCD from before! private long x, y;public void fullGCD(long a, long b){ long x1, y1; if (b == 0){x = 1;y = 0; }else{fullGCD(b, a % b); x1 = x; y1 = y;x = y1;y = x1 – (a/b) * y1; }} public long inverse(long a, long n){fullGCD(a, n); return x>0 ? x : x + n;}
Finally, Primality Testing Solution? Randomized Algorithm: Pick a random integer i from 2 to n-1 Compute gcd(i, n). If this is not 1, primality fails. Otherwise, repeat up to k times.