Enhancing Audit Mechanisms for Electronic Health Records: Addressing Current Gaps
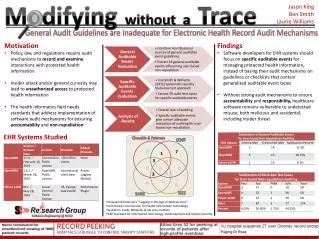
The existing general audit guidelines for electronic health records (EHRs) are inadequate in ensuring the security and integrity of protected health information. This paper argues that regulatory policies necessitate robust audit mechanisms to discourage unauthorized access. It highlights the need for health informatics standards that facilitate the implementation of specialized software audit systems. The authors recommend that EHR developers prioritize specific auditable events rather than relying on generalized guidelines, as these are prone to leaving healthcare systems vulnerable to misuse, intentional or otherwise.


Enhancing Audit Mechanisms for Electronic Health Records: Addressing Current Gaps
E N D
Presentation Transcript
Modifyingwithout a Trace Jason King Ben Smith Laurie Williams 0 0 0 0 0 General Audit Guidelines are Inadequate for Electronic Health Record Audit Mechanisms 0 0 0 0 • Motivation • Policy, law, and regulations require audit mechanisms to record and examine interactions withprotected health information • Insider attack and/or general curiosity may lead to unauthorized access to protected health information • The health informatics field needs standards that address implementation of software audit mechanisms for ensuring accountability and non-repudiation • Findings • Software developers for EHR systems should focus on specific auditable events for managing protected health information, instead of basing their audit mechanisms on guidelines or checklists that contain generalized auditable event types • Without strong audit mechanisms to ensure accountability and responsibility, healthcare software remains vulnerable to undetected misuse, both malicious and accidental, including insider threat Chuvakin & Peterson CCHIT 7 1 5 EHR Systems Studied 3 IEEE SANS • Chuvakin & Peterson’s “Logging in the Age of Web Services” • Certification Commission for Health Information Technology • SysAdmin, Audit, Network, & Security Institute • IEEE Standard for Information Technology: Hardcopy Device & System Security





![[PDF] Free Download Without a Trace By Carissa Ann Lynch](https://cdn4.slideserve.com/8339978/slide1-dt.jpg)