IEEE 802.5 Token Ring Standard Overview
220 likes | 630 Vues
Explore the IEEE 802.5 standard covering Token Ring networks, a data link layer protocol in a ring topology using a token-passing method to prevent collisions. Learn how data is transmitted in a ring and acknowledged.

IEEE 802.5 Token Ring Standard Overview
E N D
Presentation Transcript
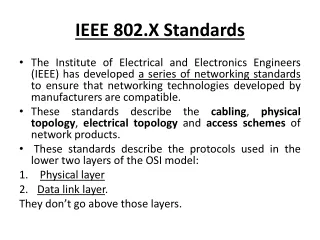
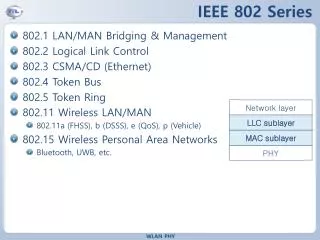
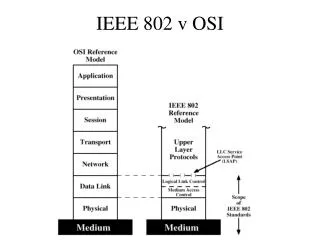
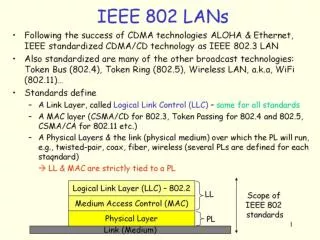
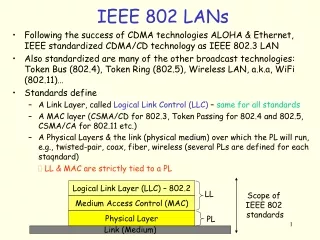
IEEE 802.X Standards • The Institute of Electrical and Electronics Engineers (IEEE) has developed a series of networking standards to ensure that networking technologies developed by manufacturers are compatible. • These standards describe the cabling, physical topology, electrical topology and access schemes of network products. • These standards describe the protocols used in the lower two layers of the OSI model: • Physical layer • Data link layer. They don’t go above those layers.
The committee structure of the IEEE is numbered like the decimal system. • The general committee working on these standards is 802. • Various subcommittees, designed by decimal numbers, have worked on different version of the standards.
IEEE 802.5 • The IEEE 802.5 standard specifies the characteristics for Token Ring networks. • Token Ring was introduced by IBM in the mid-1980s.
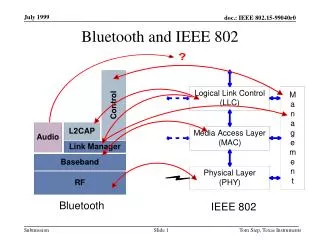
What is token ring LAN? • Token ring LAN technology is a local area network protocol which resides at the data link layer (DLL) of the OSI model. • Stations on a token ring LAN are logically organized in a ring topology with data being transmitted sequentially from one ring station to the next with a token travelling around the ring. • This standard describes a token passing protocol which means that a machine can only use the network when it has control of the “token” • This ensures that there are no collisions because only one machine can use the network at any given time.
Token ring protocol uses a special three-byte frame called a token that travels around the ring. • Token ring frames travel completely around the loop. • Stations that have data frames to transmit must first acquire the token before they can transmit data frames.
When no station is transmitting a data frame, a token frame circles the loop. • This token frame is repeated from station to station until arriving at a station that needs to transmit data. • When a station needs to transmit data, it first has to capture the free Token and replace the data with its own message. • Once the sending station receives its data frame, it converts the frame back into a token. • On 4 Mbit/s Token Ring, only one token may circulate; on 16 Mbit/s Token Ring, there may be multiple tokens.
Operation of Token Ring • At the start, a free Token is circulating on the ring. • If machine 1 wants to send some data to machine 4, so it first has to capture the free Token. • It then writes its data and the recipient's address onto the Token (represented by the yellow flashing screen).
The packet of data is then sent to machine 2 who reads the address, realizes it is not its own, so passes it on to machine 3. • Machine 3 does the same and passes the Token on to machine 4. • This time it is the correct address and so number 4 reads the message (represented by the yellow flashing screen). • Machine 4 cannot, however, release a free Token on to the ring, it must first send the message back to number 1 with an acknowledgement to say that it has received the data (represented by the purple flashing screen).
The receipt is then sent to machine 5 who checks the address, realizes that it is not its own and so forwards it on to the next machine in the ring, number 6. • Machine 6 does the same and forwards the data to number 1, who sent the original message. • Machine 1 recognizes the address, reads the acknowledgement from number 4 (represented by the purple flashing screen) and then releases the free Token back on to the ring ready for the next machine to use.
That's the basics of Token Ring and it shows how data is sent, received and acknowledged.
The following is a list of the specific characteristics specified in the 802.5 standard: • Speed: The 802.5 Token Ring specifies network speeds of 4 and 16Mbps. • Topology: Token Ring networks use a logical ring topology and most often a physical star. • Media: Token Ring networks use unshielded twisted pair cabling or shielded twisted pair. • Access method: 802.5 specify an access method known as token passing.. The token travels around the network looking for computers with data to send. The computer's data is passed along with the token until it gets to the destination computer at which point, the data is removed from the token and the empty token placed back on the ring.
802.3 IEEE Standard • The IEEE 802.3 standard defines the characteristics for Ethernet networks. • The Ethernet specification served as the basis for the IEEE 802.3 standard • What is an Ethernet? • A LAN architecture or telecommunications networking protocol introduced by Xerox Corp. in 1979. • It was developed as an inexpensive way of sending information quickly between offices machines connected together in a single room or building. • The original data rate of 10 megabits per second has been increased to 100 megabits per second for a new standard known as fast Ethernet.
Ethernet uses a bus or star topology and supports data transfer rates of 10 Mbps.
The features for 802.3 are listed here: • Speed: The original IEEE 802.3 standard specified a network transfer rate of 10Mbps. • There have been modifications to the standard, the result being Fast Ethernet (802.3u), which can transmit network data up to 100Mbps and higher, as well as Gigabit Ethernet (802.3z), which can transmit at speeds up to 1000Mbps. • 802.3ae is a very fast 803.3 standard. Known as 10-Gigabit Ethernet.
Topology: • The original Ethernet networks used a bus or star topology because the original 802.3 standard included specifications for both twisted pair and coaxial cabling.
Media • The media refers to the physical cabling used to transmit the signal around the network. • The original 802.3 specifications identified coaxial and twisted pair cabling to be used. • The more modern standards specify twisted pair and fiber-optic cable. • 802.3ae currently only supports fiber media.
Access method • The access method refers to the way that the network media is accessed. • Ethernet networks use a system called Carrier Sense Multiple Access with Collision Detection (CSMA/CD). • The CSMA/CD method is internationally standardized in IEEE 802.3 • CSMA/CD works by monitoring the computers that are sending data on the network.
If two computers transmit data at the same time, a data collision will occur. • To prevent collisions, the systems sending the data will be required to wait a period of time and then retransmit the data to avoid the collision.
Carrier Sense Multiple Access / Collision Detection, a set of rules determining how network devices respond when two devices attempt to use a data channel simultaneously (called a collision). • CSMA/CD is a type of contention protocol i.e. how to handle competition of resources. • The term contention is used especially in networks to describe the situation where two or more nodes attempt to transmit a message across the same wire at the same time.