ISP 1
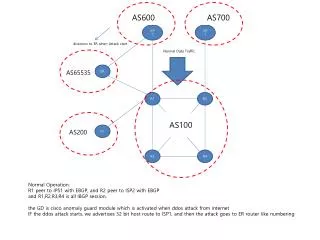
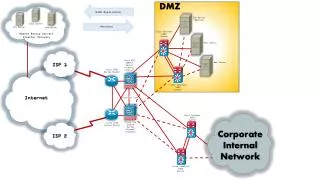
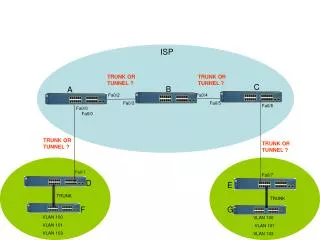
AS600. AS700. ISP 1. ISP 2. diversion to ER when Attack start. Normal Data Traffic. AS65535. ER. R1. R2. AS100. GD. AS200. R3. R4. Normal Operation: R1 peer to IPS1 with EBGP, and R2 peer to ISP2 with EBGP and R1,R2,R3,R4 is all IBGP session.

ISP 1
E N D
Presentation Transcript
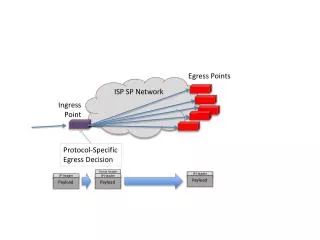
AS600 AS700 ISP1 ISP 2 diversion to ER when Attack start Normal Data Traffic AS65535 ER R1 R2 AS100 GD AS200 R3 R4 Normal Operation: R1 peer to IPS1 with EBGP, and R2 peer to ISP2 with EBGP and R1,R2,R3,R4 is all IBGP session. the GD is cisco anomaly guard module which is activated when ddos attack from internet IF the ddos attack starts, we advertises 32 bit host route to ISP1, and then the attack goes to ER router like numbering
AS600 AS700 ISP1 ISP 2 diversion to ER when Attack start Normal Data Traffic AS65535 ER R1 R2 AS100 GD AS200 R3 R4 I would like to configure GD, R1, ER bgp configuration like below, first, the GD generates 32 bit host route and announce to R1 with community set 100:20 and then R1 is accept only community 100:20 route update from GD, and advertise to ER only 100:20 route which is received from GD, and then ER advertises finally ISP1 host ip address. My question is that I don’t know how configure R1 like above scenario. please check the configuration following next sheet.
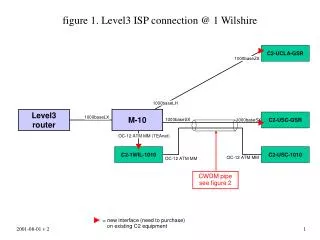
GD R1 ER ! define guard’s RHI route like static access-list 10 permit 203.254.217.68 access-list 10 permit 203.254.217.66 access-list 10 permit 203.254.217.67 ! accept only match 10 and all deny route-map adm-redip permit 10 match ip next-hop 10 route-map adm-redip deny 20 ! set community tag when outgoing to R1 route-map bgp permit 10 match ip next-hop 10 set community 100:10 router bgp 200 neighbor x.x.x.x remote-as 100 neighbor x.x.x.x send-community neighbor x.x.x.x soft-reconfiguration inbound neighbor x.x.x.x next-hop-self neighbor x.x.x.x route-map bgp out redistribute static route-map adm-redip ! ip community-list 1 permit 100:10 ! route-map filter-a permit 10 match community 1 ! router bgp 100 neighbor x.x.x.x remote-as 200 neighbor x.x.x.x send-community neighbor x.x.x.x soft-reconfiguration inbound neighbor x.x.x.x route-map filter-a in neighbor x.x.x.x remote-as 65535 neighbor x.x.x.x send-community neighbor x.x.x.x soft-reconfiguration inbound neighbor x.x.x.x route-map filter-a out ! ip community-list 1 permit 100:10 ! route-map filter-a permit 10 match community 1 ! router bgp 65535 neighbor x.x.x.x remote-as 100 neighbor x.x.x.x send-community neighbor x.x.x.x soft-reconfiguration inbound neighbor x.x.x.x route-map filter-a in neighbor x.x.x.x remote-as 600 neighbor x.x.x.x send-community neighbor x.x.x.x soft-reconfiguration inbound neighbor x.x.x.x route-map bgp out ! route-map bgp permit 10 match ip community 1 set community no-advertise ! the Guard generates 32bit host routing update to MSFC , and redistributed to BGP and then update R1 community tagged 100:10 the R1 received the 32bit host routing from GD tagged 100:10, if the community-tag is 100:10 then accept routing, and update ER tagged 100:10 ER received routing update from R1 tagged 100:10 32bit host route and update ISP1 to set no advertise finally the 32bit host routing goes into ER router