Artificial Immune Systems
340 likes | 519 Vues
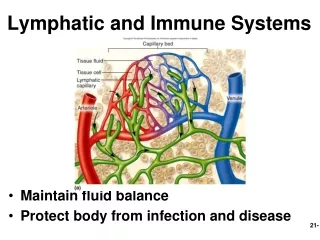
Artificial Immune Systems. Our body’s immune system is a perfect example of a learning system. It is able to distinguish between good cells and potentially harmful ones.

Artificial Immune Systems
E N D
Presentation Transcript
Artificial Immune Systems • Our body’s immune system is a perfect example of a learning system. • It is able to distinguish between good cells and potentially harmful ones. • Artificial Immunes Systems (AISs) are learning and problem solvers based on our own immune systems [Hofmeyr, S., and Forrest, S. (1999). "Immunity by Design: An Artificial Immune System", Proceedings of the 1999 Genetic and Evolutionary Computation Conference, pp. 1289--1296.] • AISs have been used to solve a wide variety of problems including: • Computer Security, • Pattern Recognition, • Mortgage Fraud Detection, • Aircraft control, • Etc.
Artificial Immune Systems • A typical AIS is composed of three type of detectors: • Immature, • Mature, • Memory • Detectors match instances (training and/or test) via a matching rule. • A matching rule that is too general will allow a detector to match many instances; • A matching rule that is too specific will cause the detector to match few instances. • An AIS evolves a population (detector set) over time. • Some immature detectors will be promoted to mature detectors (some immature detectors will die) • Some mature detectors will be promoted to be memory detectors while other mature detectors will die. • Some memory detectors may die due to: • Changes in the problem • Old age.
Artificial Immune SystemsImmature Detectors • Consider a problem where one must categorize an input instance as a member of one of two categories. Let the categories be self and non-self. • Immature detectors are randomly generated and checked to see if they match any instances (in the training set) that are self. • Any immature detectors that match a self instance die (are removed from the detector population) and are replaced with a new, randomly generated immature detector. • Immature detectors that fail to match a timmature time (typically measured in instances) in a row are promoted to being mature detectors. • The above process is referred to as Negative Selection.
Artificial Immune SystemsMature Detectors • Once a detector becomes a mature detector is will usually match _________ instances. • Mature detectors are allow tmatureamount of time to detect (or match) mmature non-self instances. • tmature represents the learning phase of a detector. • Mature detectors that fail the match the required number of anomalies, mmature, within the specified amount of time, tmature, die an are replaced with a randomly generated immature detector. Otherwise the mature detector becomes a memory detector.
Artificial Immune SystemsMemory Detectors • Memory detectors are awarded a much longer time to live, tmemory than immature or mature detectors. • Typically the required number of anomalies they must detect within their life time is mmemory = 1.
Artificial Immune Systems • How will increasing mmature affect the performance of an AIS in terms of False Positives? • What effects could it have on: • The immature detector sub-population, • The mature detector sub-population, and • The memory detector sub-population?
Artificial Immune Systems • What effect would the values assigned to timmature and tmature have on the performance of an AIS. • What effects could they have on: • The immature detector sub-population, • The mature detector sub-population, and • The memory detector sub-population?
Artificial Immune Systems • The representation for the detectors of an AIS may be: • Binary-Coded, or • Real-Coded • For Binary-Coded Representations, an r-contiguous bits matching rule can be used, • For Real-Coded Representations, an any-r intervals matching rule can be used.
Artificial Immune Systems • Consider the following AIS: Detector-1: <00101110> Detector-2: <11001010> Detector-3: <10010010> • And the following input: Input: <10101010> • Using the r-contiguous bits matching rule, which detectors match the input if: • r = 1, 2, 3, 4, and 8
Artificial Immune Systems • By increasing r, we make the match between a detector and an input ________? • By decreasing r, we make the match between a detector and an input ________?
Artificial Immune Systems • Consider the following AIS: Detector-1: <2..7, 10..14, 4..8> Detector-2: <12..15, 8..11, 10..11> Detector-3: <9..13, 3..15, 5..10 > • And the following input: Input: <12, 9, 7> • Using the any-r intervals matching rule, which detectors match the input if: • r = 1, 2, 3
Artificial Immune Systems • When working with real-coded (interval) detectors what other characteristic determines the generality or specificity of a match?
Artificial Immune Systems • What would a Binary-Coded Detector for this problem look like? • What would a Real-Coded (Interval) Detector for this problem look like?
Artificial Immune Systems • How would we develop an AIS for this problem?
Vulnerability Analysis of Immunity-Based Intrusion Detection Systems Using Evolutionary Hackers Gerry Dozier Auburn University Douglas Brown Clark-Atlanta University John Hurley Boeing Krystal Cain Clark-Atlanta University
Overview • Motivation • The AIS-Based IDS • The Genetic and Swarm-Based Red Teams • Training and Test Sets for the IDS • The Experiment • Results and Conclusions
Motivation • Intrusion Detection Systems based on machine learning techniques have two types of errors: • False Positives (Type-I Error) • False Negatives (Type-II Errors) • Concerning Type-II Errors (Holes): • Does one try to identify and/or patch holes in advance? (Proactive Approach) • Does one allow the hackers to identify the holes first? (Reactive Approach)
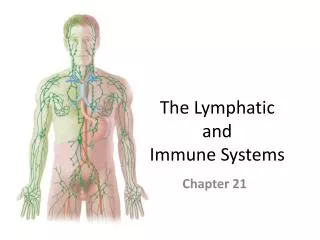
Our AIS-Based IDS • Our AIS-Based IDS is based on the work of Steven Hofmeyr & Stephanie Forrest (Hofmeyr & Forrest 1999). • It distinguishes between: • self (normal traffic) • non-self (abnormal traffic)
Our AIS-Based IDS • Our AIS-based IDS is composed of a set of detectors. • There are three types of detectors • Immature Detectors • Mature Detectors • Memory Detectors • Negative Selection is used to evolve mature detectors.
Our AIS-Based IDS • The AIS receives packets in the form of data triples: • <ip_address, port, src> • src = 0 (incoming packet) • src = 1 (outgoing packet) • Constraint-Based Detectors • (lb0..ub0, lb1..ub1, lb2..ub2, lb3..ub3, lbport..ubport, src) • An Any-3 interval matching rule is used. • If an immature detector fails to match 200 self data triples, then it becomes a mature detector.
The Genetic and Swarm Based Red Teams • The Genetic Red Team • Steady-State (μ+1) GA • Population Size = 300 ‘red’ data triples • BLX-0.5 Recombination (Eshelman & Schaffer, 1992)
The Genetic and Swarm-Based Red Teams • The Particle Swarm Optimizer Used: • Asynchronous Update of V and X • vid = vid + 1*rnd()*(pid-xid) + 2*rnd()*(pgd-xid); • xid = xid + vid; • Where i is the particle, • 1=2.3,2=1.8 are learning rates governing the cognition and social components • Where g represents the index of the particle with the best p-fitness, and • Where d is the dth dimension.
The Genetic and Swarm-Based Red Teams • The Swarm-Based Red Teams
Training and Test Sets for the AIS-Based IDS • 1998 MIT Lincoln Lab Data • 35 days of Simulated Network Traffic • Class B Network • Extracted packets involving host 172.16.112.50 • Removed packets involving port 80 • Mapped remaining packets to 70 distinct ports based on the work Hofmeyr and Forrest.
Training and Test Sets for the AIS-Based IDS • Extracted normal traffic for training set (112 self data triples). • Trained on 80% of the self data triples. • Used the other 20% to test for the Type-I (false positive) error rate. • Test set consisted of 1604 malicious packets (all attacks launched at the host during the 35 day period).
The Experiment • A Comparison of the 7 Red Teams • AIS-Based IDS used a population size of 400 detectors • After the AIS was trained, each Red Team, using a population size of 300, was allowed a total of 5000 ‘red’ data triple evaluations. This was repeated 10 times. • The AIS-Based IDS had: • a detection rate of 0.747 • a false positive rate of 0.4
The Experiment • A ‘red’ data triple of a Red Team was evaluated as follows: • If a ‘red’ data triple was a member of the self-set, then it received a fitness of zero. • If a `red’ data triple was not a member of self, it was assigned the percentage of the detector set that it evaded. • Data triples that evaded 100% of the AIS detector set and were not members of the self-set are consider holes (Type-II Errors)
Results • The swarms with the local neighborhood performed better that those with global neighborhoods • In terms of PT, those that used PT found a greater number of holes and had a greater number of duplicates. • RB did not provide any performance improvement. • The visualization of SW0+ and SW0 lead to the development of an improved detector represenatation.