Securing Windows Server 2003
Securing Windows Server 2003. Objectives. Understand the use of Group Policy Secure Windows Server 2003 using security policies Manage security by using the Security Templates Snap-in Configure client security by using Windows Server 2003 policies Configure the Encrypting File System.

Securing Windows Server 2003
E N D
Presentation Transcript
Securing Windows Server 2003
Objectives • Understand the use of Group Policy • Secure Windows Server 2003 using security policies • Manage security by using the Security Templates Snap-in • Configure client security by using Windows Server 2003 policies • Configure the Encrypting File System
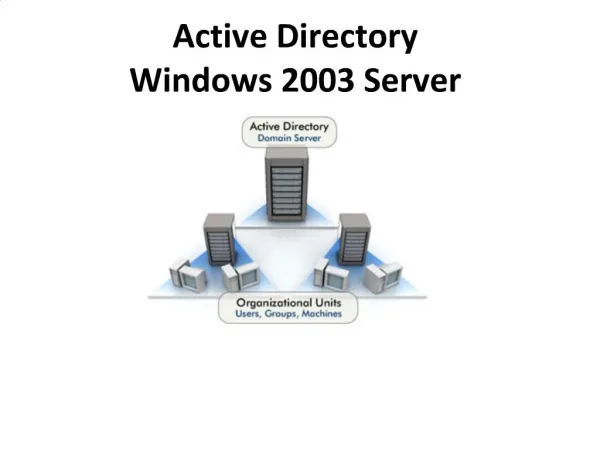
Introduction to Group Policy • Group Policy in Windows Server 2003 allows a standardized working environment for clients and servers • Evolved from the NT Server 4.0 system policy concept • Has more capabilities than system policy • Can extend to cover multiple domains in one site • Set for more environments • More secure because users cannot modify policies • Dynamically updates, and configured to reflect current needs
Group Policy characteristics • Can be set for a site, domain, OU, or local computer • Cannot be set for non-OU folder containers • Policy settings for groups are stored in Group Policy objects (GPOs) • Each GPO has a unique name and GUID • There are local and nonlocal GPOs • When there are multiple GPOs, their effect is incremental • The ordering is local, default domain, site, OUs • Group Policy can be set up to affect user accounts, computers, or both • When Group Policy is updated, old policies are removed or updated for all clients
Securing Windows Server 2003 Using Security Policies • Security policies are a subset of the Group Policy • Some commonly used security policies • Account policies • Audit policy • User rights • Security options • IP Security policies • Can be configured with the following tools • Domain Security Policy tool can be used for domain and local computer • Group Policy Object Editor Snap-in has the most functionality • Active Directory Users and Computers tool can be used for domain or OU
Establishing Account Policies • Account policies are located in the following Group Policy path: • Computer Configuration, Windows Settings, Security Settings • Account policy options • Password security • Account Lockout • Kerberos security
Password Security Options • Enforce password history • Requires users to choose new passwords when they make a password change • Maximum password age • Sets maximum time before password expires • Commonly 45 to 90 days • Minimum password age • Minimum password length • A minimum of seven characters for a “strong password” • Password must meet complexity requirements • Filter of customized password requirements • Store passwords using reversible encryption
Account Lockout Options • Account lockout duration • Permits you to specify in minutes how long the system keeps an account locked out after reaching the specified number of unsuccessful logon attempts • Account lockout threshold • Enables you to set a limit to the number of unsuccessful attempts to log on to an account • Reset account lockout counter after • Enables you to specify the number of minutes between two consecutive unsuccessful logon attempts to make sure that the account is not locked out too soon
Kerberos Security • Involves the use of tickets that are exchanged between the client who requests access and the server or Active Directory that grants access • A key distribution center (DC or server) stores user accounts and passwords • The client computer sends an account name and password to the key distribution center • The key distribution center issues a temporary ticket granting access to the ticket-granting server • The ticket-granting server issues a service ticket for the duration of a logon session
Kerberos Security Options • Enforce user logon restrictions • Turns on Kerberos security, which is the default • Maximum lifetime for a service ticket • Maximum time in minutes that a ticket can access a particular service in one service session • Maximum lifetime for a user ticket • Maximum time in hours that a ticket can be used in one continuous session for access to a computer or domain • Maximum lifetime for user ticket renewal • Maximum number of days that the same Kerberos ticket can be renewed each time a user logs on • Maximum tolerance for computer clock synchronization • Length in minutes a client waits until synchronizing its clock
Establishing Audit Policies • Account management • Directory service and object access • Logon and logoff events for an account and at the local computer • Policy change and privilege use • Process tracking and system events
Configuring User Rights • User rights enable an account or group to perform predefined tasks such as the following: • Access a server • Create accounts • Manage server functions • Assign user rights to groups instead of to individual user accounts • Members of a group inherit the user rights of the group
Configuring Security Options • Over 65 specialized security options in the following categories • Accounts • Audit • Devices • Domain controller • Domain member • Interactive logon • Microsoft network client • Network access
Configuring Security Options (cont.) • Network security • Recovery console • Shutdown • System cryptography • System objects • System settings • Options in each category are specialized to the category
Security Templates Snap-in • Useful when there are multiple Group Policies or multiple OUs that share the same Group Policy • Sets up security for the following • Account and local policies • Event log tracking policies • Group restrictions • Service access security • Registry security • File system security
Configuring Client Security • Provides improvements in security • Ensures a consistent working environment in an organization • When a client logs onto to the server or network, the policies are applied to the client • Examples of use: • Folder redirection for sensitive data • Desktop icon management to start applications the same way for all clients
Manually Configuring Policies for Clients • Use the Group Policy Object Editor Snap-in
Summary • A Group Policy enables you to standardize how people use server and client computers on a network • Security policies are part of a Group Policy and are configured to protect users and resources • Configure account policies to apply to OU, domains, sites, or local computers • Password policies, account lockout policies, and Kerberos authentication policies • Use audit policies to track how resources are accessed, such as folders, files, or user accounts
Summary • User rights policies enable you to create specific security controls over privileges and logon access • Security options are specialized policies for accounts, auditing, devices, domain controllers, logon, clients, network access, network security, and other activities • Use the Security Templates Snap-in to apply default security settings or to create different Group Policy objects for different OUs, domains, or sites • For better control over the activities of clients, manually configure administrative templates or apply preconfigured administrative templates (or both)
Summary • Publish and assign applications to manage how clients use them • Use the Resultant Set of Policy Snap-in to plan and troubleshoot Group Policies • Fine-tune the use of the Encrypting File System by using the cipher command in the Command Prompt window