Secure Trigger Algorithms for Secret Disclosure: Definitions and Applications
This paper details the concept of secure triggers in the context of information security. A trigger is defined as an algorithm that reveals a secret if certain conditions (predicates) about input data are met. The paper presents examples including simple, multiple strings, and subsequence triggers, and demonstrates their security against polynomial-time attackers. Practical applications discussed include information warfare and software protection. The work outlines generic definitions of security for triggers and provides instantiations that confirm such triggers as secure.

Secure Trigger Algorithms for Secret Disclosure: Definitions and Applications
E N D
Presentation Transcript
Secure Triggers Ariel Futoransky, Emiliano Kargieman, Carlos Sarraute, Ariel Waissbein Core Security Technologies {ek,wata}@coresecurity.com
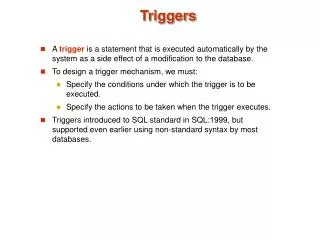
Definitions • Let S be a secret and P={p} a family of predicates.Let p be a predicate in P • Def: A trigger is an algorithm T(S,p) that takes any input x in {0,1}* and returns S iff p(x)=true.Else, it returns nothing. • Def: The trigger T(S,p) is said secure if a polynomial-time attacker, given P, the sampling distribution, and arbitrary access to T(S,p), cannot learn anything about S.
S Examples (1): Simple Trigger • If the input x is equal to a private value y, then the Secret S is released. T(S,“x=y?") ? x = y
S Examples (2): Multiple Strings Trigger • If the input set X={x1,…,xn} includes a private set Y ={y1,…,yt}, then the Secret S is released. T(S,“XY?") x1 ? y1 … … … yn xn
Examples (3): Subsequence Trigger • If xi1 = y1, …, xit = yt, then the secret S is released. • Where both {yj}, and {ik} are private. T(S,“(xjk)=(yk)?") x xi1
Examples (3): Subsequence Trigger • If xi1 = y1, …, xit = yt, then the secret S is released. • Where both {yj}, and {ik} are private. T(S,“(xjk)=(yk)?") x xi1 xi2
Examples (3): Subsequence Trigger • If xi1 = y1, …, xit = yt, then the secret S is released. • Where both {yj}, and {ik} are private. T(S,“(xjk)=(yk)?") x xi1 xi2 … xit
S Examples (3): Subsequence Trigger • If xi1 = y1, …, xit = yt, then the secret S is released. • Where both {yj}, and {ik} are private. T(S,“(xjk)=(yk)?") x x ? xi1 y1 = xi2 y2 = … … xit yt =
Applications of the triggers • Information Warfare WormAttack • Online automated shopping • Other • Software protection • …
Results • Generic definitions of security for Secure Triggers on the UCS framework • Instantiations: • Simple triggers are secure • Multiple strings triggers are secure • Subsequence triggers are secure • Paper submitted for publication,let us know if you want a copy