Chaos in Cryptography
Chaos in Cryptography. What is Chaos in Cryptography Chaos Functions Application in Cryptography Why it isn’t used. What does it mean?. Use Chaos Functions Pseudo Random Generation One-Time Pad. Chaos Functions. Sensitive to Initial Value Sequence Based on Seed

Chaos in Cryptography
E N D
Presentation Transcript
Chaos in Cryptography • What is Chaos in Cryptography • Chaos Functions • Application in Cryptography • Why it isn’t used
What does it mean? • Use Chaos Functions • Pseudo Random Generation • One-Time Pad
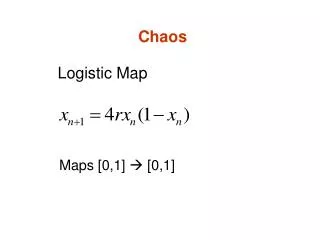
Chaos Functions • Sensitive to Initial Value • Sequence Based on Seed • Non-Computable Generation
The Logistic Map • Xn+1 = R * Xn (1 – Xn) • R = 4 Bifurcation Diagram Diagram shows accuracy based on initial seed.
Application in Cryptography • Seed Unique to Key • Generate One-Time Pad • Symmetric Key System
64 Bit Example • Generate Key • Convert to Seed • Iterate • XOR with Data • Symmetrical Operation
Why it isn’t used • Security Cannot Be Proven • Attractors • Computationally Expensive
References Dr. Ranjan Bose and Amitabha Banerjee. “Implementing Symmetric Cryptography Using Chaos Functions” Wikipedia http://en.wikipedia.org/wiki/Logistic_map M. S. Baptista, “Cryptography with Chaos” Physics Letters A , Vol. 240, Pages 50–54, 1998 Shujun Li, Guanrong Chen, Kwok-Wo Wong, Xuanqin Mou, and Yuanlong Cai. “Baptista-type chaotic cryptosystems: Problems and countermeasures”