Memory Management Unit
Memory Management Unit. Mrs. Shilpa S. Paygude. Architecture of 80386DX. 80386DX Features. Flexible 32-Bit Microprocessor 8, 16, 32-Bit Data Types 8 General Purpose 32-Bit Registers Very Large Address Space 4 Gigabyte Physical 64 Terabyte Virtual

Memory Management Unit
E N D
Presentation Transcript
Memory Management Unit Mrs. Shilpa S. Paygude
80386DX Features • Flexible 32-Bit Microprocessor 8, 16, 32-Bit Data Types 8 General Purpose 32-Bit Registers • Very Large Address Space 4 Gigabyte Physical 64 Terabyte Virtual 4 Gigabyte Maximum Segment Size
Contd. • Integrated Memory Management Unit Virtual Memory Support Optional On-Chip Paging 4 Levels of Protection • Virtual 8086 Mode Allows Running of 8086 Software in a Protected and Paged System • Optimized for System Performance Pipelined Instruction Execution On-Chip Address Translation Caches 20, 25 and 33 MHz Clock
Previous members in x86 family • No Memory Management Unit • Application program size limited to available memory (RAM) • Single tasking environment • Segment size maximum 64KB
Requirements of Efficient working Environment • Multitasking • Protection –Restricted Access to Data , Code & Stack • Secure Access to I/O devices • With minimum available memory, execution of application of any size
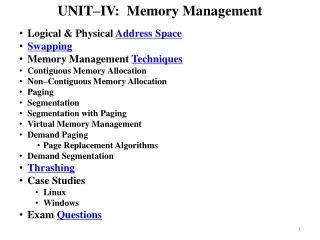
Modes of Operation • Real Address Mode • Protected Mode • Virtual 86 Mode
Protected Mode Features • Multitasking • Protection • Virtual Memory- Demand Paging
Significant Facts • Microprocessor can execute one instruction at a time • Microprocessor works very fast ( in microseconds ) compared to human response time
Components of MMU • Segmentation Unit : Deals with segments of a program . • Paging Unit : Divides programs in fixed size (4KB) blocks.
Segmentation Unit • Defines various types of segments with different attributes and provides segment level protection. • Cannot be Disabled. • It converts Logical Address to Linear Address.
Paging Unit • Divides a program in fixed sized pages(4KB). • Swaps pages between RAM & secondary device as required. • Provides page level protection. • It converts Linear address to Physical address. • Optional -can be enabled or disabled.
Address Translation • Virtual / logical address to Linear Address • CS : IP Base address + IP Linear address • Linear Address to Physical Address Linear Address Base address from page table + offset
Segmentation • Segmentation is one method of memory management. • Segmentation provides the basis for protection. • Segments are used to encapsulate regions of memory which have common attributes. • Segment selectors can be considered the logical “name” of a program module or data structure
What Are Segments? • Segments are variable sized blocks of linear addresses which have certain attributes associated with them • There are two main types of ( non system) segments: code and data • Segments are of variable size - as small as 1 byte or as large as 4 gigabytes • Base address (32bit) + Offset (32bit) Linear Address • Base address defined in the descriptor by system
A segment is described by a structure – Segment Descriptor • Each segment (Code/data/stack) has a unique descriptor in memory • All descriptors are maintained in a table – Descriptor Table
System Tables • GDT (Global Descriptor Table), • IDT (Interrupt Descriptor Table), • LDT (Local Descriptor Table), • TSS (Task State Segment).
Global Descriptor Table (GDT), & GDTR Segment base address (32 bit) GDT Offset (32bit) Segment register + GDTR Linear address (32bit)
Global Descriptor Table • The Global Descriptor Table (GDT) contains descriptors which are possibly available to all of the tasks in a system. • The GDT can contain any type of segment descriptor except for descriptors which are used for servicing interrupts (i.e. interrupt and trap descriptors). • Every Intel386 DX system contains a GDT
Contd. • Generally the GDT contains code and data segments used by the operating systems and task state segments, and descriptors for the LDTs in a system. • GDT contains descriptors for segments which are common to all tasks
Local Descriptor Table • LDTs contain descriptors which are associated with a given task. • Generally, operating systems are designed so that each task has a separate LDT. • The LDT may contain only code, data, stack, task gate, and call gate descriptors. • There can be 0 or many LDTs.
LDTR • The visible portion of the LDT register contains only a 16-bit selector. • This selector refers to a Local Descriptor Table descriptor in the GDT. • LDTs provide a mechanism for isolating a given task's code and data segments from the rest of the operating system
Privilege Level • Privilege Level-One of the four hierarchical privilege levels. • Level 0 is the most privileged level and level 3 is the least privileged. • More privileged levels are numerically smaller than less privileged levels.
Privileged Instructions • System tables are manipulated by the operating system. • Therefore, the load descriptor table instructions are privileged instructions. • The instructions that can be executed at CPL=0 are privileged instructions.
Paging • Paging is another type of memory management useful for virtual memory multitasking operating systems • Freed space of an outgoing task always same as that needed for an incoming task • A page most likely corresponds to only a portion of a module or data structure
Components of the paging mechanism • The page directory • The page tables • The page itself (page frame)
Advantages • A uniform size of 4KB for all of the elements simplifies memory allocation and reallocation schemes, since there is no problem with memory fragmentation. • Protection can further be increased at page level.
Linear Address to Physical Address Linear Address Base address Page PDBR CR3 Page Table Directory Page Table
PAGE DESCRIPTOR BASE REGISTER • CR3 is the Page Directory Physical Base Address Register. It contains the physical starting address of the Page Directory. • Page Directory is always page aligned. • CR2 is the Page Fault Linear Address register. It holds the 32-bit linear address which caused the last page fault detected
PAGE DIRECTORY • The Page Directory is 4K bytes long and allows up to 1024 Page Directory Entries. • Each Page Directory Entry contains the address of the next level of tables, the Page Tables and information about the page table. • Page Directory Entry points to Page Table
PAGE TABLES • Each Page Table is 4K bytes and holds up to 1024 Page Table Entries. • Page Table Entries contain the starting address of the page frame and statistical information about the page • Page tables can be shared between tasks and swapped to disks.
Page Level Protection • The paging mechanism distinguishes between two levels of protection: User which corresponds to level 3 of the segmentation based protection, and supervisor which encompasses all of the other protection levels (0, 1, 2). • Programs executing at Level 0, 1 or 2 bypass the page protection, although segmentation based protection is still enforced by the hardware.
Bits used for Protection • The U/S and R/W bits are used to provide User/Supervisor and Read/Write protection for individual pages or for all pages covered by a Page Table Directory Entry • The U/S and R/W bits in the first level Page Directory Table apply to all pages described by the page table pointed to by that directory entry.
Page Level Protection • The U/S and R/W bits in the second level Page Table Entry apply only to the page described by that entry. • The U/S and R/W bits for a given page are obtained by taking the most restrictive of the U/S and R/W from the Page Directory Table Entries and the Page Table Entries
Translation Lookaside Buffer • Performance would degrade substantially if the processor was required to access two levels of tables for every memory reference. • Intel386 DX keeps a cache of the most recently accessed pages, this cache is called the Translation Lookaside Buffer (TLB).
Translation Lookaside Buffer • The TLB is a four-way set associative 32-entry page table cache. • It automatically keeps the most commonly used Page Table Entries in the processor. • The 32-entry TLB coupled with a 4K page size, results in coverage of 128K bytes of memory addresses.