Functions of the Data Link Layer
110 likes | 308 Vues
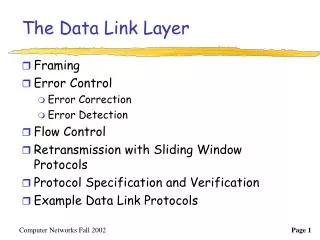
Explore the essential functions of the Data Link Layer including error detection and correction mechanisms and their impact on network communication. Learn about transmission errors, error-correcting codes, Hamming codes, CRC codes, and more.

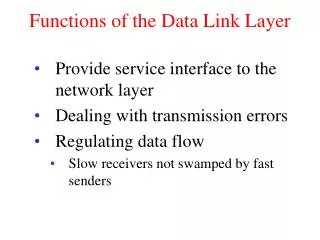
Functions of the Data Link Layer
E N D
Presentation Transcript
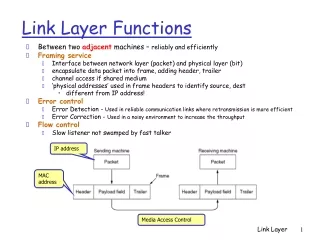
Functions of the Data Link Layer • Provide service interface to the network layer • Dealing with transmission errors • Regulating data flow • Slow receivers not swamped by fast senders
Functions of the Data Link Layer (2) Relationship between packets and frames.
Errors in transmission • Basics of transmission – variation of (amplitude/phase/frequency) • SNR • 10 log ((peak signal/(RMS Noise)^2) • Regenerative Repeaters • Bit Error Ratio (BER) • Optical medium is around 10^-14 • Wireless is around 10^-3 • Copper in between • Gaussian Noise/AWGN • Burst errors
Error Detection and Correction • Error-Correcting, Error-Detecting Codes • Some Basics • Msg (m) + Redundant(r) = Code(n) • Not all codewords are legal • Hamming Distance is the number of positions where two codewords differ • If 2 codewords are distance d apart, then it takes d errors to convert one to the other => • d+1 distance for d error detection • 2d+1 distance for d error correction
Error Detection and Correction • Parity as an EDC • 1 bit parity creates a code with distance 2 • 00 --> 000, 01 --> 011 • Suppose we want to correct all single errors in an m bit message. How efficient can such a code be in terms of length ? • n bit code => n single bit errors => n+1 codes/valid msg • (n+1)2^m <= 2^n or m+r+1 <= 2^r
Hamming Codes • Hamming codes obtain the theoretical lower bounds (perfect parity codes) • In a codeword, powers of 2 are the check bits, and the other bits contain data • The parity of a data bit is checked by several check bits, as directed by the binary representation of its position. • Bit 11s parity is checked by 1+2+8 • Reciever “adds” parity bits in error, and this gives the location of the error bit! • Interleaving to detect burst errors
Error-Correcting Codes Use of a Hamming code to correct burst errors.
Error Detecting Codes • Useful when BERs are low and overhead of ECC is significant compared to Re-Tx. • Still use the interleaving idea to convert burst errors into single bit errors • Polynomial (CRC) codes • A k+1 bit number is represented as a polynomial of degree k in some dummy variable, with leftmost bit being most significnt. • Sender and receiver agree on the “generator” of the code, another polynomial G(x), with 1s in msb and lsb • Polynomial arithmetic is done modulo 2 (no carries or borrows, GF(2))
CRC Codes • Append a “checksum” to the end of the msg • If G(x) is of degree r, then append r 0s to end of the m msg bits. The new number is now x^rM(x) • Divide this by G(x) modulo 2 • Subtract the remainder from X^rM(x) modulo 2, and let this be T(x). This number is now divisible by G(x) • Transmit T(x), and have receiver check if the received data is divisible by G(x) • Suppose T(x)+E(x) arrives. • (T(x)+E(x)/G(x) ) = E(x)/G(x) • Detection whenever E(x)/G(x) != 0
Error detection in CRC • 1 bit error will be caught as long as G has 2 or more terms • For 2 isolated bit errors if G(x) does not divide x^k+1 where k = distance between error bits • CRC-CCITT 1+x^5 +x^12 +x^16 • IEEE 802 (32,26,23,22,16,12,11,10,8,7,5,4,2,1,0) • BCH Codes are GF(2^m). Reed-Solomon are BCH codes with block size 2^m • Convolution codes (Trellis or Viterbi)
Error-Detecting Codes Calculation of the polynomial code checksum.