Higher Computing Computer Systems
Learn about operating systems - the program controlling your computer's operations and devices. Explore key components like memory management, process management, and file management. Understand utility programs and their roles, from virus checkers to disk editors. Discover how resource allocation and input/output management work. Dive into examples of OS operations and the importance of efficient system management.

Higher Computing Computer Systems
E N D
Presentation Transcript
Higher Computing Computer Systems ComputerSoftware
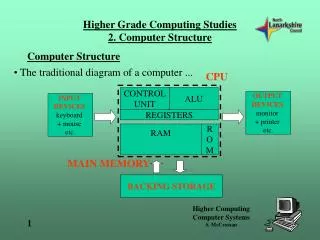
What is an operating system • The operating system is a program that controls the entire operation of the computer and devices which are attached to it • Most of the OS is permanently stored on hard disk and loaded in to RAM when the computer is on
The bootstrap loader • When the computer is switched on the initial part of the OS is loaded from chip (ROM) • The bootstrap loader’s function is to load the rest of the OS from disk
The single user operating system • A SUOS is only capable of being used by one person at a time • The main functions of a SUOS are: • Interpreting users commands (CLI) • File management • Memory management • I/O management • Managing processes • Resource allocation
The Command Language Interpreter • The CLI is the layer with which the user interacts in order to give instructions to the computer – it interprets user commands
File management • The FMS is concerned with the efficient use of the computer’s backing storage devices and media • The FMS holds the details of where each file (or part of) is held on the disk • The FMS is also known as the Disk Operating System
Memory management • The MMS controls where programs and data are placed in main memory • The MMS keeps track of the total amount of main memory available and which programs and data are currently loaded
Input/Output management • The I/OMS communicates directly with the peripheral devices • The I/OMS handles the transfer of data between the peripherals and the processor
Process management – the kernel • The kernel is the part of the OS which is responsible for managing interrupts • e.g. from the printer • The kernel is responsible for managing processes • from the CLI e.g. copy. A process initiated by the CLI may result in an interrupt
Resource allocation • RS is the way of managing which resource is available for use at any one time by a process • Efficient RS ensures that the processor is kept busy, by maintaining a queue of processes that are always ready for the processor • A “scheduler” prioritises the queue
The OS working - an example • Loading the file “myfile” from disk • Using the CLI you issue the command to open a folder • The kernel interrupts the current CLI process and passes the request to the FMS • The FMS requests the I/O system to read the disk’s catalog track and loads a list of file names • The CLI allows the user to choose the filename “myfile” from the list • The FMS passes the physical location of the file to the I/O system • The I/O system loads the file from disk and hands it over to the MMS • The MMS places the file in the main memory and you again have control of the computer
Utility programs • UP’s can be part of the OS or a separate program • Virus checker • Disc editor • Defragmenter • Backup • Emulators • Converters, compressors and expanders • Email and web filters
Virus checker • A virus checker is a utility program which is designed to check a computer system for viruses • A virus checker will then remove the virus • Virus checkers have to be kept up to date in order to be effective against new viruses
Disc editor • A disc editor allows the user to edit data directly on the surface of a disk • DE programs incorporate automatic disk repair and data recovery functions • Newer hard drives “smart drives” have their own software for which monitors the performance of the drive
Defragmenter • Files are often split and saved on different parts of a disk • This increases the time taken to access the file • A defragmenter gathers all the free space on the disk together and reunites all the fragmented files that can be accommodated
Before defragmenting After defragmenting Used block unused block
Backup • Backup software can help to automate the process of making regular backups • Backup software can allow you to synchronise files between two devices or media • When two copies of the same file exist on different media the newer copy will replace the older version
Emulators • An emulator is a program that allows one type of computer to behave as if it was a completely different type • A computer running emulator software will run much slower than the computer it is emulating • Virtual PC allows apple computers to emulate Windows OS computers
Converters, compressors and expanders • Converters change the format of a data file from one application type to another • Compressors reduce the size of a data file • Expanders decompress a compressed data file
Printer drivers • A program that takes the codes in the document and translates them into the appropriate code for the printer in use
Email and web filters • An email filter is software that monitors emails which are sent on a network • The Regulation of Investigatory Powers Act (2000) gives employers the right to monitor employees email • A web filter monitors URLs and the content of web pages be accessed by the user
File formats • Standard file formats have been developed to ease the transfer of data between software developed by different manufacturers e.g. text files - RTF • Each type of application software has its own set of standard file formats e.g. JPEG used in photographic manipulation software
File formats - GIF • Graphics Interchange Format • For low resolution bit-map colour graphics • 256 colours possible • Compressed files • Fast to load and transfer via internet • Interlacing allowed • Animations also possible • GIF uses lossless compression
File formats – JPEG, MPEG • Joint Photographic Experts Group • Standard for still picture compression • 16.7 million colours • Uses lossy compression • Typically achieves 10 to 1 compression with little perceivable loss in image quality • Motion Pictures Expert Group • Standard for moving pictures
File formats - TIFF • Tag(ged) Image File Format • For high resolution bit-map images • Large files unsuitable for WWW • Uncompressed • Used by DTP, book and magazine printing
Matching software to tasks (1) • Production of a multimedia catalogue • Multimedia authoring package e.g. Macromedia Director • Additional software for editing individual elements • Video • Audio • Graphic • Text • And • CD or DVD writing software
Matching software to tasks (2) • Setting up a LAN in a school • Modern OS capable of peer to peer networking • Client server needs network OS software • Database servers need specific software e.g. Microsoft SQL • Database application such as Filemaker Pro are available in single or network versions
Matching software to tasks (3) • Development of a school website • Web page creation software with WYSIWYG page editing • Additional software for editing individual elements • Video • Audio • Graphic • Text • And • Testing using a range of browser software
Software compatibility issues • Software that works on a computer system is said to be compatible • Issues that can affect the compatibility of the software are: • Memory requirements • Storage requirements • OS compatibility
Memory requirements (RAM) • If a system cannot meet the minimum RAM requirements to run the software the software will not run • If there is insufficient RAM to hold the complete program then part of it will be stored on disk, virtual memory • Running programs using VM will slow the program
Storage requirements • Full installation - The amount of backing storage needed to hold the complete program after installation (and decompression) • Minimal installation – The least amount of storage requirement needed to run the program, normally the installation CD is still needed to run the program
OS compatibility • Three main OS used on desktops and laptops • Windows • Unix • Apple OS • Users need the correct version of software for the different OS • Windows OS not always backward compatible
Viruses • A virus is a program which can destroy or cause damage to data stored on a computer system • A virus infects host files and is distributed along with them
Worm • A worm is a virus that can make copies of itself and spread between computers without having to be attached to a file
Trojan horses • A Trojan horse is disguised as another type of file
What viruses infect • A virus may infect different parts of the computer system • File viruses • Boot sector viruses • Macro viruses
File viruses • File viruses attach themselves to files • They add malicious code into the files • Typical files that are infected are Windows OS files with .COM and .EXE extensions
Boot sector viruses • All magnetic disks contain a boot sector • The boot code can become infected with a virus and is loaded when the machine is rebooted • Less common now that floppy discs are no longer in popular use
Macro viruses • A macro virus infects documents e.g. spreadsheets or word processing documents • A macro virus causes a malicious series of events once the document is opened • The macro virus will also infect any new documents created by the same application
Virus code actions • Virus act differently according to how they are programmed • The action the virus may carry out when run include: • Replication • Camouflage • Watching • Delivery
Replication • A worm can make copies of itself this is known as replication
Camouflage • Mixed in with good code • Malicious or false code is changed every time it runs to avoid detection • Disguise the code so that it looks harmless • All these techniques are used to avoid detection by anti-virus programs
Watching • Sleeper virus lays in wait for a particular sign which will activate it • A date or time or action • Time bomb (triggered by a date) • Logic bomb (triggered by an action)
Delivery • The method used by the virus to enter the system • Shared backing storage devices • Connected to the internet • Web pages • Downloads • Emails • Email attachments
Anti-virus detection • Anti-virus software detection techniques include: • Use of checksum • Searching for virus signature • Heuristic detection • Memory resident monitoring
Use of checksum (1) • A checksum is a value calculated for a given set of data • The answer to the calculation is the checksum • It is used to check that data has been transmitted and received correctly
Use of checksum (2) • The checksum is transmitted along with the data • The receiving computer performs the same calculation and checks the sum • If they are the same its ok • If the don’t match the anti-virus software will issue a virus warning
Searching for virus signature • Anti-virus programs can find viruses inside programs by scanning them for virus signatures • A virus signature is a characteristic pattern in a file • These files can then be disinfected • Polymorphic viruses modify their code to avoid virus signature detection
Heuristic detection • Detect viruses a heuristic or rule of thumb method • Imprecise method although useful • If it looks like a virus and behaves like a virus then its probably a virus • Used to detect new viruses
Memory resident monitoring • Anti-virus software that loads in to the computers memory on start up • Monitors all programs and data loaded in to the computers memory • Can slow down the processing speed of a computer as everything is checked for viruses