Technological Prerequisites
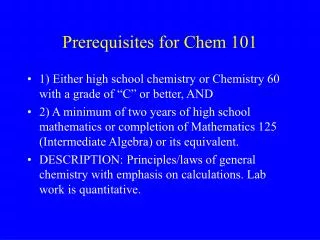
Technological Prerequisites Internet Protocols Internet Addresses Routing Subnetting CIDR Eugenie Staicut <estaicut@linkguide.ici.ro> Research Institute for Informatics Bucharest, Romania CEENet ‘97 3-rd Network Technology Workshop 23-31 August 1997, Zagreb, Croatia INTERNET PROTOCOLS

Technological Prerequisites
E N D
Presentation Transcript
Technological Prerequisites • Internet Protocols • Internet Addresses • Routing • Subnetting • CIDR Eugenie Staicut <estaicut@linkguide.ici.ro> Research Institute for Informatics Bucharest, Romania CEENet ‘97 3-rd Network Technology Workshop 23-31 August 1997, Zagreb, Croatia
INTERNET PROTOCOLS • Internet protocols • can be used for communications between heterogeneous systems; • can be used for communications between systems connected in a LAN (local area network); • can be used for communications between systems connected in a WAN (wide area network); • can be used for communications between a set of interconnected networks; • are specified in documents called RFCs (Requests For Comments), which are reviewd and analyzed by the Internet community; improvements, additions and refinements of protocols are published in new RFCs (see ftp://ftp.rs.internic.net., ftp://ftp.ripe.net/). • Looking at all RFCs, you can see the history of the development of Internet protocols and the people and companies that have contributed to this development • TCP and IP are the best known of the Internet protocols and very often the term TCP/IP refers to the whole family of protocols.
Internet Protocols SNMP NFS RPC FTP RFC 959 RIP RFC 1058 Routing protocols EGP Telnet RFC 854 SMTP RFC 821 DNS RFC 1035 ICMP RFC 792 TCP RFC 793 UDP RFC 768 IP RFC 791 ARP RFC 826 X.25 Ethernet/IEEE 802.3 PPP HDLC SLIP LAPB LAN Public telephone network
SMTP mail exchange as an example There is a protocol for mail that defines a set of commands and messages that one machine sends to the other, for example, a conversation between machines ROEARN and KYOTO-U: ROEARN: HELO roearn.ici.ro KYOTO-U: 250 kyoto-u.ac.jp - HELO, roearn.ici.ro ROEARN: MAIL From:<estaicut@roearn.ici.ro> KYOTO-U: 250 MAIL accepted ROEARN: RCPT To:<tsakai@kyoto-u.ac.jp> KYOTO-U: 250 Recipient accepted ROEARN: DATA KYOTO-U: 354 Start mail input; end with <CTRL>,<CRLF> ROEARN: Date: Sat, 26 Jul 96 14:23:34 +02 ROEARN: From: estaicut@roearn.ici.ro ROEARN: To: tsakai@kyoto-u.ac.jp ROEARN: Subject: helo ROEARN: text of the message ROEARN: . KYOTO-U: 250 OK ROEARN: QUIT KYOTO-U: 221 KYOTO-U.AC.JP Service closing transmission channel The protocol assumes that we have a reliable way of command and message communication
TCP - Transmission Control Protocol • TCP is the protocol layer responsable for making sure that the commanmds and messages are transmitted reliably from one application program running on a machine to another one on the other machine; • A message is transmitted and then a positive acknowledgement is being waited for; • If the positive aknowledgement does not arrive in a certain period of time, the message is retransmitted; • Messages are numbered in sequence so that no one is being lost or duplicated; • Messages are delivered at the destination in the same order they were sent by the source; • If the text of a mail is too large, the TCP protocol wiill split it into several fragments called “datagrams” and it makes sure that all the datagrams arrive correctly at the other end where they are reassembled into the original message; • The TCP protocol layer provides all the functions that are needed for many applications and it is better to put them toghether on a separate protocol rather than being part of each application. • TCP can be viewd as forming a library of routines that many applications can use when they need reliable network communication with an application on another computer; • TCP provides also flow control and congestion control
TCP segment format Source TCP port (16 bits) Destination TCP port (16 bits) Sequence Number (32 bits) Acknowledgement number (32 bits) Offset Reserved (6) Flags (6 bits) Window (16 bits) Header Checksumm (16 bits) Urgent pointer Options Padding Application Data/Command (variable length)
Why do we need IP protocol layer? • Although the services provided by TCP protocol are needed by many applications, there are still some kind of applications that don’t need them; • However, thre are some services that every application needs. • The services that every application needs are put toghether into the IP protocol layer; • IP protocol provides the basic service for the transmission of a datagram from one machine to another machine which do not need to be connected directly; • As a result, TCP calls on the services of IP; • Like TCP, IP protocol layer can be viewd as a library of routines that TCP calls on, but which is also available to applications that don’t use TCP; • IP functions: • send a datagram from a source to a destination node with: • no end-to-end data reliability; • no flow control; • no sequencing; • provide addressing • allow for fragmentation
IP datagram format Type of Service (8 bits) Header length Version Total Length (16 bits) Identification (16 bits) 0 D M Fragment Offset Time to Live Protocol Header Checksum Source IP address (32 bits) Destination IP address (32 bits) TCP header Data
Protocol Number • The protocol number identifies the the protocol in the layer above IP to which the data should be passed; • See the file /etc/protocols on a UNIX machine 0 IP pseudo protocol number 1 ICMP 6 TCP 17 UDP
IP Address Structure - Class-full Address format 32 bits Network address Host address Class A network=8 bits 0 Class B network=16 bits 1 0 Class C network=24 bits 1 1 0 Class D (multicast) 1 1 1 0 Clas E (reserved) 1 1 1 1
Internet Addresses • Each host connected to Internet is uniquely idendified by an IP address which is a 32-bit number • IP Address Structure • Class A: x.0.0.0 x=0..127; Contains 16777215 host addresses • Class B: x.y.0.0 x=128..191; y=0..254; Contains 65536 host addresses • Class C: x.y.z.0 x=192..223; y,z=0..254; Contains 256 host addresses • Multicast and reserved addresses: x.0.0.0 x=224..255 • Example of addresses: Class A: 10.0.0.0 Class B: 141.85.0.0 Class C: 192.162.16.0
Some addresses are reserved for special use • Network address 0 (class A) designates the default route (0.0.0.0). The default route is used to simplify the routing information • Network 127 designates the loopback address (127.0.0.1 is the localhost) • The loopback address simplifies network applications by allowing the local host to be addressed in the same manner as a remote host. The address 127.0.0.1 is always used when configuring a host, otherwise unexpected problems appear. • An IP with all bits set to 0 identifies the network itself . • Example: 192.162.16.0 refers to the network 192.162.16 • 141.85.0.0 refers to the network 141.85 (class B) • 10.0.0.0 refers to the network 10 (class A) • An IP with all host bits set to 1 is a broadcast address.
Network access protocols • The medium for communication between two machines directly connected can be: coax, twisted cable, telephone link, radio link, satellite link, etc. The lowest layer of protocols provides functions that manage the data transmission specific to a certain physical medium. Ethernet/IEEE 802.3 • Ethernet was jointly developed by Xerox, Intel and Digital Equipment Corporations • Ethernet was the technological basis for the IEEE 802.3 specification • Both of them specify the CSMA/CD (Carrier Sense Multiple Access with Collision Detection), also refered as “listen while talk” (LWT) • Both are broadcast networks
CSMA/CD • On a CSMA/CD LAN, stations can access the networks any time • Before sending data, the station “listens” to the network to see if it is already in use • If so, the station wishing to transmit waits • If the network is not in use, the station transmits • A collision occurs when two stations listen for network traffic, “hear” none, and transmit simultaneously • In this case both transmissions are damaged and the stations must retransmit at some later time • While it is transmitting, each transceiver monitors the cable to see if another signal interferes with its transmission • When a collision is detected, the host interface aborts transmission, waits for activity to subside, and tries again • To avoid producing a new collision, the sender delays a random time after the first collision, twice as long if a second attempt to transmit also produces a collision, four times as long if a third attempt results in a collision, and so on
Ethernet frame format • The preamble contains an alternating pattern of ones and zeros that tells receiving stations that a frame is coming • The SOF (Start of Frame) ends with two consecutive one bits, which serve to synchronize the frame reception portion of all stations on the LAN • Destination and source addresses: • they are 6 bytes long • they are contained in hardware on the Ethernet/IEEE 802.3 interface cards • the first three bytes are specified by the IEEE on a vendor-dependent basis • the last three bytes are specified by the card vendor • the source address is always a unicast (single mode) • the destination address may be unicast, multicast (group), or broadcast (all nodes) Source Address (48 bits) Preamble (56 bits) CRC (32 bits) Destination Address (48 bits( Type (16 bits) Data (368-1200 bits) SOF (8 bits)
Ethernet frame format (continue) • The type field specifies the upper-layer protocol to receive the data after Ethernet peocessing is complete • The data field contains the actual data which are sent to the upper-layer protocol • The CRC (Cyclic Redundancy check) is created by the sending device and recalculated by the receiving device to check for damage that might have occurred to the frame in transit • The frame length (header, data, and CRC) cannot be smaller than 64 bytes or larger than 1518 bytes Application Data Appl. TCP TCP T Data T Data IP Data I T I T Data IP E I T Data Ethernet E I T Data C C Ethernet Ethernet
Example of vendor-dependant Ethernet addresses Prefix Manufacturer 00:00:0C Cisco 00:00:95 Proteon 00:00:A2 Wellfleet 00:00:C0 Western Digital 00:AA:00 Intel 02:60:8C 3Comm 08:00:09 Hewlett-Packard 08:00:10 AT&T 08:00:0B Unisys 08:00:20 Sun 08:00:2B DEC 08:00:46 Sony 08:00:5A IBM AA:00:03 DEC AA:00:04 DEC
Sockets and application programs • On a network server, normally several application programs are run at a time: FTP server, telnet server, mail server, www server, gopher server, etc.; • There should be a possibility that the TCP program will know to which program to deliver the received message; • If you want to connect to the FTP server it is not enough to know the IP address of the server, you have to specify that you want to talk to the FTP server program; • This is done by having “the well-known sockets” - TCP ports - (see the file /etc/services on a UNIX machine): • In a file server session, for example, two different programs are involved: the FTP server program and the FTP client program; • The client program gets commands from the user and paseses them to the FTP server program; • There is no need for the client FTP program to use a well know socket number, because nobody is trying to find it, as opposed to the FTP server program which have to have a well-known socket number, so that people can open connections to it and start sending commands; • The client FTP program asks the network software to assign it a port number that is guaranted to be unique, for example 1236 if that number was free; • A connection is identified by four numbers: IP addresses and port numbers at each end: connection 1: 192.162.16.2, 1236 193.230.3.120, 21 connection 2: 192.162.16.2, 1237 193.230.3.120, 21 • Two connections are different if at least one number is different;
Well-known TCP ports 21 - FTP server 23 - telnet server 25 - SMTP mail server 53 - domain nameserver 109 - POP2 server 110 - POP3 server
UDP - User Datagram Protocol • TCP is responsable for the fragmentation of messages with datagrams on the same computer and reassembling them properly on the destination computer; • Many applications generates messages that fit in a single datagram; • Example: suppose that somebody entered the command: ftp indis.ici.ro • Before establishing the connection between the FTP client program on the source computer and the FTP server program on the destination computer, indis.ici.ro, the network software on the source computer has to find out the IP address of the destin ation computer - indis.isi.ro; • The request is sent to a nameserver which has a database used to translate name addresses into IP addreeses; indis.ici.ro - 192.162.16.30 • This query is very short and it fits in a datagram; • The answer is also very short and it fits in a single datagram too; • So, there is no need to send the query using TCP protocol. • In addition to message fragmentation, TCP provides a reliable message transmission,; • The response can be used as a positive acknowledgement; if the sending process does not get the answer after a few seconds, it will just send the query again; • TCP preserves also the order of the message sent by source; • In case of nameserver queries, if a computer sends a query for www.ibm.com and then for roearn.ici.ro, there will be no problem if it gets at first the answer for roearn.ici.ro and then for www.ibm.com;
UDP - User Datagram Protocol (continue) • For a query that fits in a single datagram, TCP protocol is too complex to be used and provides high overhead; • UDP is the protocol used to send messages that fit in a single datagram, with no need to preserve the sequence and no requirements for a reliable delivery; • UDP header contains UDP port numbers; • UDP port numbers allow that several programs can use UDP at a time; • UDP ports are used like TCP ports: • there are well known port numbers for server programs that use UDP, for example UDP port 53 for nameserver (see the file /etc/services on a UNIX machine) • UDP header is shorter than a TCP header: • it has source and destination ports, lentgh and checksum; • no sequence number, acknowledgement number and window are required; • UDP is an unreliable connectionless protocol; • UDP provides low overhead. • UDP message format Source UDP port (16 bits) Destination port (16 bits) Total length (16 bits) Checksumm Data (variable length)
ICMP - Internet Control Message Protocol • ICMP is not used by the application programs like TCP and UDP; • ICMP is used by TCP/IP software itself for error report or other information relevant to IP processing; • For example, if you attemp to connect to a host (hostA.domain), your system may get back from a router an ICMP message saying “host unreachable” • Like UDP, ICMP handles messages that fit in a single datagram; • The IPCM encapsulates the message with an IP header and then gives it to the IP protocol to deliver it to the destination; • ICMP is simpler than UDP, it does not have ports in its header, since there is no need to allow the use of its services by several application programs at a time; • ICMP messages are processed by the network software not by the application programs; • Nine types of ICMP messages have been defined: • Destination unreachable • Time exceeded • Parameter problem • Source quench • Redirect • Echo • Echo reply • Timestamp • Timestamp reply
General format of ICMP message Type (8 bits) Code (8 bits) Checksum (16 bits) Type (8 bits): specifies the type of ICMP message Code (8 bits): used to specify parameters of the message that can be encoded in a few bits Checksum (16 bits): checksum of the entire ICMP message Parameters (32 bits): used to specify more lengthy parameters Information (variable): provides additional information related to the message • The ECHO and ECHO REPLY messages provide a mechanism for testing that communication is possible between two entities. A host can send the ICMP ECHO message to see if a remote system’s Internet protocol is up and operational. When a system receives an echo message, it send the same packet back to the source host in an ICMP ECHO REPLY message. The ping command uses this message. • A TIME EXCEEDED message is sent by a gateway if the time-to-live (ttl) value of a datagram expires (becomes zero). This facility is used by the traceroute command. Parameters (32 bits) Information (variable)
The ping command - Testing basic connectivity ping • it is a simple function, extremely useful for testing the network connection; • it allows the network administrator to determine whether further testing should be directed toward the network (the lower layers) or the application (the upper layers) • if ping shows that packets can travel to the destination system and back, the problem is probably in the upper layers • If packets can’t make the round-trip, lower protocol layers are probably at fault Basic format ping <host> [<packetsize>] [<count>] <host> The host name or IP address of the remote host being testyed. <packetsize> Defines the size in bytes of the test packets. This field is only required if the count field is going to be used. Default packet size is 56 bytes. <count> The number of packets to be sent in the test. Default number is usually 5.
ping example Examples #ping ftp.ripe.net info.ripe.net is alive # ping -s ftp.ripe.net 100 10 PING info.ripe.net: 100 data bytes 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=0. time=1070. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=1. time=990. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=2. time=990. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=3. time=990. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=4. time=990. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=5. time=990. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=6. time=990. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=7. time=980. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=8. time=990. ms 108 bytes from info.ripe.net (39.13.5.97): icmp_seq=9. time=1000. ms ----info.ripe.net PING Statistics---- 10 packets transmitted, 10 packets received, 0% packet loss round-trip (ms) min/avg/max = 980/998/1070
traceroute - Tracing routes traceroute • is the program that can help the network administrator locate the problem when something is down between the local host and a remote destination • traces the route of UDP packets from the local host to a remote host • prints the name (if it can be determined) and IP address of each gateway along the route to the remote host • uses two techniques: smal ttl (tim-to-live) values and invalid port number
traceroute - Tracing routes Operation • traceroute sends out 3 UDP packets with ttl value set to one • the first gateway decrement ttl and gets the value zero. • The first gateway will send back to the source host an ICMP TIME EXCEEDED message as error message • traceroute displays one line of output for each gateway from which it receives an ICMP TIME EXCEEDED message • traceroute will then increment by one the ttl value and sends again 3 UDP packets • the flow of packets tracing to a host three hops away is illustrated below • When the destination host receives a packet from traceroute, it returns back an ICMP “Unreachable Port” message. This happens becuaue traceroute intentionally uses an invalid port number (33434) to force this error. • When traceroute receives the “Unreachable Port” message, it knows that it has reached the destination host, and it terminates the trace. • In this way, traceroute is able to develop a list of the gateways, starting at one hop away and increasing one hop at a time, until the remote host is reached.
traceroute example # traceroute ftp.ripe.net traceroute to info.ripe.net (39.13.5.97), 30 hops max, 40 byte packets 1 agsici1.ici.ro (192.162.16.25) 20 ms 10 ms 0 ms 2 Vienna-EBS1.Ebone.NET (192.121.159.97) 870 ms 870 ms 870 ms 3 Paris-EBS2.Ebone.net (192.121.156.17) 900 ms 890 ms 890 ms 4 Stockholm-ebs.ebone.net (192.121.154.21) 920 ms 930 ms 960 ms 5 Amsterdam-ebs.Ebone.NET (192.121.155.13) 970 ms 990 ms 970 ms 6 Amsterdam.ripe.net (193.0.15.130) 1000 ms 970 ms 970 ms 7 info.ripe.net (39.13.5.97) 1040 ms 970 ms 990 ms # traceroute ccfs1.fuw.edu.pl traceroute to ccfs1.fuw.edu.pl (148.81.4.8), 30 hops max, 40 byte packets 1 agsici1.ici.ro (192.162.16.25) 0 ms 0 ms 0 ms 2 Vienna-EBS1.Ebone.NET (192.121.159.97) 870 ms 880 ms 870 ms 3 Poland-gw.nask.pl (192.121.159.34) 1000 ms 910 ms 1010 ms 4 gollum.nask.waw.pl (193.59.201.18) 1100 ms 1110 ms 950 ms 5 gw-bbone.fuw.edu.pl (148.81.4.97) 1150 ms 1030 ms 1080 ms 6 ccfs1.fuw.edu.pl (148.81.4.8) 970 ms 1020 ms 1160 ms
traceroute example # traceroute oak.oakland.edu traceroute to oak.oakland.edu (141.210.10.117), 30 hops max, 40 byte packets 1 agsici1.ici.ro (192.162.16.25) 30 ms 10 ms 0 ms 2 Vienna-EBS1.Ebone.NET (192.121.159.97) 870 ms 870 ms 870 ms 3 Paris-EBS2.Ebone.net (192.121.156.17) 900 ms 890 ms 900 ms 4 icm-dc-2b-S4/0-1984k.icp.net (192.157.65.129) 1040 ms 1000 ms 1040 ms 5 icm-dc-1-F0/0.icp.net (198.67.131.36) 1050 ms 1050 ms 1030 ms 6 icm-mae-e-H1/0-T3.icp.net (198.67.131.9) 1050 ms 1040 ms 1040 ms 7 * cpe2.Washington.mci.net (192.41.177.181) 1050 ms 1050 ms 8 border2-hssi4-0.Washington.mci.net (204.70.57.9) 1040 ms 1060 ms 1020 ms 9 core-fddi-1.Washington.mci.net (204.70.3.1) 1060 ms 1050 ms * 10 core-hssi-3.NewYork.mci.net (204.70.1.6) 1310 ms 1080 ms 1050 ms 11 core-hssi-3.Boston.mci.net (204.70.1.2) 1240 ms 1070 ms 1070 ms 12 core-hssi-4.Chicago.mci.net (204.70.1.46) 1150 ms 1070 ms 1030 ms 13 border2-fddi-0.Chicago.mci.net (204.70.3.82) 1040 ms * 1100 ms 14 merit-michnet-ds3.Chicago.mci.net (204.70.25.10) 1070 ms 1070 ms 1160 ms 15 * fdd0.michnet1.mich.net (192.203.195.4) 1080 ms 1080 ms 16 35.119.16.2 (35.119.16.2) 1180 ms 1250 ms * 17 oak.oakland.edu (141.210.10.117) 1340 ms 1270 ms *
Flow of traceroute packets ping program First router Second router Third router ttl=1 decrements ttl to 0 return error “TIME EXCEEDED” ttl=2 decrements ttl to 1 forward decrements ttl to 0 return error “TIME EXCEEDED” ttl=3 decrements ttl to 2 forward decrements ttl to 1 forward received at destination port unreachable Return error “port unreachable”
ARP - Address resolution Protocol • ARP software maintains a table which translates IP addresses to Ethernet addresses, for example the ARP table for hosA may loo like: hostC.domain (192.162.16.3) at 08:00:5A:23:1A:3D hostD.domain (192.162.16.4) at AA:00:03:12:6B:56 • The ARP table is built dynamically; • Suppose the IP level on hostA (192.162.16.1) receives from a higher level protocol a packet to be sent to hostC (192.162.16.3): • The system hostA will first verify that the destination IP address 192.162.16.3 is on the same Ethernet, so it can send the packet directly via Ethernet; • Then it will lookup 192.162.16.3 into the ARP table, to see if it already knows the Ethernet address; it gets the result 08:00:5A:23:1A:3D, in our case; • Now the IP packet is encapsulated into the Ethernet packet and sent via Ethernet. hostA hostB hostC hostD 192.162.16.2 192.162.16.3 192.162.16.4 192.162.16.1
ARP - Address resolution Protocol (continue) • Now, suppose that hostA (192.162.16.1) needs to send a message to hostB (192.162.16.2): • The system hostA will not find the address 192.162.16.2 in the ARP table, so it will not get the Ethernet address of the host B; • The packet cannot be sent to hostB, because its Ethernet address is needed; • hostA will use now the ARP protocol to find out the Ethernet address of host B; • host A sends an ARP request, which is a broadcast message, sent to all the computers on teh LAN, asking the Ethernet address of the hosts which has the IP address 192.162.16.2; • Every system on the LAN listens to ARP requests; • Only the hostB will identify the address 192.162.16.2 specified in the ARP request as being hios own address and it will send an ARP reply message to hostA, saying that the Ethernet address associated to TP 192.162.16.2 is 08:00:20:36:AB:3C • After receiving the reply, the hostA will make a new entry in ths ARP table associated with hostB, so from now on it will know to which Ethernet address to send the packets with the destination 192.162.16.2.
arp command • arp command can be used to display the content of the ARP table; • Formats: • arp -a ! displays all the entries in the ARP tabl;e • arp <hostname> ! displays the entry for <hostname> specified • arp -d <hostname> ! deletes an entry for <hostname> • arp -s <hastname> <ether-address> ! adds a new entry
ROUTING The source and the destination hosts are on the same LAN • There is no decission for routing; • The packet is transmitted on the cable (coax, twisted cable, optical fiber); • Every computer connected to the LAN will receive it. • That computer which finds that the destination Ethernet address in the header is equal to his Ethernet address will get the message, the others will discard it. • Note that the address of each computer on the LAN begins with the same network number • Routing table for hostA:
Connecting two LANs A B C E F • A host on LAN1 can send to any host on LAN1 directly via Ethernet; • A host on LAN2 can send to any host on LAN2 directly via Ethernet; • If the source host A (192.162.16.1) is on LAN1 and the destination host F (193.230.3.3) is on LAN2, the host A sends the datagram to the router D at first, which is connected to both networks, then the router D will send the datagram to the destination host F. D G .1 .2 .3 .4 router .1 .2 .3 .4 eth0 ec0 ec1 LAN1 192.162.16. LAN2 193.230.3..
A more complex configuration Routing tables net gw int. M: 193.230.5 none eth0 193.230.6.2 sl0 193.230.4 193.230.5.1 eth0 193.230.3 193.230.5.1 eth0 192.162.16 193.230.5.1 eth0 default 193.230.6.2 sl0 I 193.230.5 none eth0 193.230.4.1 sl0 193.230.3 193.230.4.1 sl0 192.162.16 193.230.4.1 sl0 default 193.230.5.5 eth0 H 193.230.3 none ec0 193,230.4.2 sl0 192.162.16 193.230.1 ec0 default 193.230.4.2 sl0 A 192.162.16 none eth0 default 192.162.16.4 eth0 A .1 D G .4 .4 .1 ec0 eth0 eth0 193.230.3. ec1 ec0 192.162.16. .2 .1 H sl0 193.230.4. sl0 .2 .1 L .4 K .3 J .2 I eth0 193.230.5. .5 .1 M sl0 193.230.6. backbone network with Internet connectivity sl0 .2 N
Routing table initialization and updating • Initialization of routing table • Normally at startup time by executing script command files; • Static routes route add <network-address> <gw-address> <metric> route add 192.162.16.0 192.162.16.4 1 route add 193.230.3.0 192.162.16.4 1 route add default 192.162.16.4 1 • The command netstat -rn displays the routing table on a UNIX machine • Static routes have the disadvantage that they do not adapt to the changes in the network topology • Dinamic routing protocols are run to update the routing table so that they reflect the changes in topology • Router classes • dedicated routers - special purpose equipment • Cisco, Wellfleet, Proteon, Telebit • cheap router sollution: - public domain software for PCs • ka9q, PCROUTE, Linux, Free BSD
Routing protocols • Types of routing protocols • Routing within an AS - Interior Gateway Protocol (IGP) • RIP, IGRP, OSPF, Hello • Routing between ASs - Exterior routing Protocol (EGP) • BGP3/4, EGP AS1 AS2 EGP IGP IGP
Autonomous System Number • An Autonomous System Number (AS) is a set of routers under a single technical administration, using an interior gateway protocol and an exterior gateway protocol to route packets to other ASs. • An AS is a connected group of IP networks run by one or more network operators which has a single and defined routing policy. • AS number is a 16 bit number (65535 unique AS numbers). • It is a finite amount of address space. • Sometimes, the term AS is misunderstood and used for grouping together a set of prefixes which belong under the same administrative umbrella. • AS number are assigned by RIPE in Europe
Example for routing static IGRP National Academic Network IGRP IGRP IGRP BGP4 BGP4 EUROPANET EBONE Access to Internet
Subnetting • One class address (either B or C) space could be too large for a given organization, or for a certain site of the organization. • Subnetting divides a single network address into many subnet addresses, so that each subnetwork can have its own unique address. • A subnet is defined by applying a bit mask (the subnet mask) to the IP address. • If a bit is 1 in the mask, the equivalent bit in the address is interpreted as a network bit. • If a bit in the mask is 0, the bit belongs to the host part of the address. • Ex: mask to divide the 193.226.2.0 address into 4 subnets: 11111111 11111111 11111111 11000000
Subnetting -example network number host Class-full addressing Class C 192.162.16.0 11000000 10100010 00010000 00000000 11111111 11111111 11111111 00000000 Implicit network mask 0 255 255 255 11111111 11111111 11111111 11000000 Subnetting host subnet Network mask 255 255 255 192
Subnetting - example LAN1: 192.162.16.0-63 LAN3: 192.162.16.128-191 LAN2: 192.162.16.64-127 LAN4: 192.162.16.192-255 sl0 sl1 LAN3 - remote LAN4 - remote router sl2 LAN2 LAN1 ec0 ec1 192.162.16.16.0 255.255.255.128 192.162.16.16.128 255.255.255.128 Router configuration: route add 192.162.16.0/26 ec0 route add 192.162.16.64/26 ec1 route add 192.162.16.128/26 sl1 route add 192.162.16.192/26 sl2 route add default sl0 The subnet is only known locaklly by the routerconnecting the subnets, it is not known to the rest of the Internet
CIDR - Classless Inter-Domain Routing Internet • Example: Internet Service Provider customers 193.230.3.0 193.230.0.0 193.230.1.0 193.230.02.0 host Class-full representation network 193.230.0.0 11000001 00000000 00000000 11100110 00000000 11000001 11100110 00000001 193.230.1.0 193.230.2.0 11000001 11100110 00000010 00000000 1110010 00000011 00000000 193.230.3.0 11000001 Host Prefix Classless representation
Example of CIDR configuration (supernetting) Using BGP4 routing protocol, all the 4 C class addresses (193.230.0.0, 193.230.1.0, 193.230.2.0, 193.230.3.0) can be advertized like one entry in the routing table: router bgp 3233 agregate-address 193.230.0.0 255.255.252.0 summary-only neighbor 192,121,159,97 remote-as 1755 neighbor 193.226.27.86 remote-as 2614 Using BGP4 routing protocols, all the 256 C addresses of the block 193.230.0.0 - 193.230.255.255 can be advertized like one entry in the routing table: router bgp 3233 agregate-address 193.230.0.0 255.255.0.0 summary-only neighbor 192,121,159,97 remote-as 1755 neighbor 193.226.27.86 remote-as 2614
REFERENCES • Craig Hunt, “TCP/IP Network Administration, O’Reilly & Associates, Inc., Sebastopol, 1993 • Internetworking Technology Overview, Cisco Systems, Inc., 1993 • Kevin Dowd, “Getting Connected, Internet at 56K and Up”, O’Reilly & Associates, Inc., Bonn, 1996. • E. Comer, “Internetworking with TCP/IP”, Vol I, Principles, Protocols and Architecture, Prentice Hall, Englewood Cliffs, New Jersey, 1991. • William Stallings, Data and Computer Communications, Macmillan Publishing Company, New York, 1985. • Booktexts of the 4th Network Seminar and Intensive Course for Scientists and Network Managers from Central Europe, Feb. 1993, Vienna University Computer Center • Booktexts of Network Technology Workshop, National Network Management Track, Honolulu, June 1995