Agile Security Self Organizing Systems of Systems Pattern Project
260 likes | 412 Vues
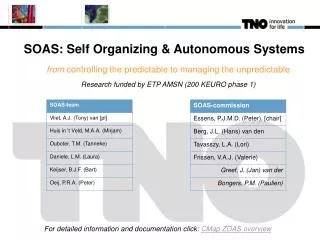
Agile Security Self Organizing Systems of Systems Pattern Project. Possible Masters Project. What Are We Doing?. Questions we seek answers for: What makes SO- SoSes work (achieve, grow, behave properly, evolve, …)? What recurring patterns are seen in various kinds of successful SO- SoSes

Agile Security Self Organizing Systems of Systems Pattern Project
E N D
Presentation Transcript
Agile SecuritySelf Organizing Systems of SystemsPattern Project Possible Masters Project
What Are We Doing? • Questions we seek answers for: • What makes SO-SoSes work (achieve, grow, behave properly, evolve, …)? • What recurring patterns are seen in various kinds of successful SO-SoSes • What are the metrics of SO-SoS success? • What are useful SO-SoSes to observe and analyze for clues? • What knowledge can be utilized now – where and how? • What information can be tested now – where and how? • What data can be experimented with now – where and how? • We are developing a “pattern language” for discourse – we can’t talk about concepts or think about them if we have no words for them, • nor assemble them into meaningful constructions if we don’t have a grammar.
Today, All Systems are Prey. • It matters not their intended purpose and function. Technology is their Achilles heel. They are defenseless in an age of guerrilla warfare, technologically empowered individuals, rapid technology development, do-it-yourself affordability, readily accessible knowledge, global infrastructure networks, and the human hacker inclination to re-purpose a system just because it’s there. • Systems engineering is awesome. We stand in wonder at the good we can build. In time we find that this respect and awe is not shared by all. Some take equal fulfillment in destruction or exploitation, no matter the motivation. The modern response is after-the-breech correction and watchdog shepherding. Even the weapon-bristling naval system is humbled by the rubber-rafted bomb. • In days of old the important systems embedded security in the architecture: fortress cities, castles, booby-trapped tombs. Security had high priority in the system engineering trade-space. Security was rooted in fundamental requirements and values. The technologies of construction and destruction were on a level playing field. With the scientific age the development of technology by those who practiced construction outpaced the efforts of those who focused on destruction. The entry barriers of resource and knowledge favored socially-developed countries and high-visibility activities. Embedded system security was unnecessary, and atrophied as a practice. Now we have come full circle, as technically literate and adept practitioners have again leveled the playing field of construction and destruction, of protection and exploitation. • It is past time that system engineering reclaim and embrace the responsibility for system security. Technology advancement discovers new vulnerability and exploitation faster than systems can respond. Flatfooted, they sit as prey. Stone and mortar castle architecture would not suffice today, nor city fortress emplacement architecture.
System Security is a Prime SO-SoS Learning Opportunity • Observed Asymmetric Advantages of the Artificial-System Adversary • Adversary leads with innovation and evolution • Adversary is a natural system, current security strategy is an artificial system • Adversary self-organizes as a dynamic system-of-systems Architecture: Multi-agent Loosely coupled Self organizing Systems-of-systems Behavior: Swarm intelligence Tight learning loops Fast evolution Dedicated intent Assumptions: All systems are prey. The goal of a “natural” SO-SoS is survival. Fundamental natural strategies for survival are innovation and evolution. Currently the artificial-system predator has superior “natural” strategies. Natural systems have evolved very successful survival patterns. Artificial-system predators have evolved very successful attack patterns. The best Test & Evaluation is confrontation with the intelligent adversary!
Maslow’s Hierarchy of Needs(for systems that would live one more day) • Its not about Cyber Security …all systems are prey • Its about co-evolving self-organizingsystems of systems, each with first priority onsecuring and maintaining existence. Maslow’s Hierarchy of Needs (5) Discretionary: non-functional performance of existence (community impact) (4) Quality: functional performance of existence (3) Functionality: product of existence (reason for, purpose of) (2) Security: sustains existence (1) Energy: enables existence 2nd Order: As affordable 1st Order: Core necessity
Maslow’s Hierarchy of Needs(for systems that would live one more day) • Its not about Cyber Security …all systems are prey • Its about co-evolving self-organizingsystems of systems, each with first priority onsecuring and maintaining existence. Maslow’s Hierarchy of Needs Harmony (5) Discretionary: non-functional performance of existence (community impact) (4) Quality: functional performance of existence (3) Functionality: product of existence (reason for, purpose of) (2) Security: sustains existence (1) Energy: enables existence 2nd Order: As affordable Performance Functionality 1st Order: Core necessity Security Needs Energy Needs
System-AdversaryObserved Behavior Patterns & Characteristics • Fast learning loops • Resilient • Collaborative • Innovative • Adaptable • Self organizing • Distributed • Evolving • Communities of active practice • Effortful learning • Experimental • Technology repurposing • Disposable resources (Suicide attacks, expendable Al-Q cells, …) • 4th gen war patterns • 5th gen war patterns • …et al. The Adversary is Systemically Agile
Reality • SO-SoS scares people - but SO-SoS are all around us - and the adversary thrives on it • SysEs, SecEs and Decision Makers don’t communicate • Only SysEs can enable next gen SecE: SO-SoS • We need a common language and vision = OBJECTIVE - for SysEs, SecEs, and Decision Makers • Patterns reflected from common understandings • - solve communication problem - solve scary problem - brings shared vision into focus • (Should you care to accept the mission….) • You can be in the vanguard of SO-SoS pattern discovery • - choose patterns useful to your work & knowledge dev. • - suggested pattern concepts can be provided - source reference material can be provided - collaboration will be provided
Objective Met with Stories, Graphics, Metaphors, References Decision Maker Systems Engineer • common • language • concepts • comfort Security Engineer
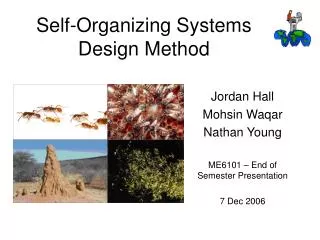
To Start: Mirror the Enemy • Agile system security, as a minimum, must mirror the agile characteristics exhibited by the system attack community: • [S] Self-organizing – with humans embedded in the loop, or with systemic mechanisms. • [A] Adapting to unpredictable situations – with reconfigurable, readily employed resources. • [R] Reactively resilient – able to continue, perhaps with reduced functionality, while recovering. • [E] Evolving in concert with a changing environment – driven by vigilant awareness and fitness evaluation. • [P] Proactively innovative – acting preemptively, perhaps unpredictably, to gain advantage. • [H] Harmonious with system purpose – aiding rather than degrading system and user productivity. www.parshift.com/Files/PsiDocs/Pap100226-AgileSecuritySelfOrganizingCoEvolution-ExtAbst.pdf
Axiom*: SAREPH Minimum CombinationsMinimum = S & (A|E) & (R|P) & H Natural systems exhibit all six characteristics. Artificial self-organizing agile systems will have at least one combination that traces a path from S to H, for a minimum of four characteristics. Self Organization Adaptive Tactics S A Trace any/all paths from S to H S means the system dances at the pace set by situational reality. But by itself, if S provides no value (beat is right but dance is independent of situation), it is useless. If we have S and H, without value (benign result), it is still useless. A good example of S-A-R-H is exhibited by the New York subway control room. S w/o A doesn’t ensure things happen when they must/should. Evolving Strategy Reactive Resilience R E Proactive Innovative Harmonious Operation P H * subject to change
When a room has a window with a view, it is a focal point: people are attracted to the window and want to look through it. The furniture in the room creates a second focal point: everyone is attracted toward the point the furniture aims them at (the center of the room or a TV). This makes people feel uncomfortable. They want to look out the window, and toward the other focus at the same time. Rearrange the furniture so its focal point becomes the window, and everyone is comfortable. That's a very simple example, and there are literally hundreds more in this book and its sequel. The book's main idea is much more powerful than that. It applies to almost every aspect of life, not just to architecture. When a situation makes us unhappy, it is usually because we have two conflicting goals, and we aren't balancing them properly. Alexander's idea is to identify those ``conflicting forces'', and then find a solution which brings them into harmony. [Leonard R Budney, Amazon Reviewer] (253 patterns) (read this one) This four-volume work is Christopher Alexander's magnum opus of architectural philosophy, and a book on which he has been working for over twenty years. The essence of that view is this: the universe is not made of "things," but of patterns, of complex, interactive geometries. Furthermore, this way of understanding the world can unlock marvelous secrets of nature, and perhaps even make possible a renaissance of human-scale design and technology. [Michael Mehaffy, Amazon Reviewer]
Our Pattern Form Name: Descriptive name for the pattern. Context: Situation that the pattern applies to. Problem: Description of the problem. Forces: Tradeoffs, value contradictions, constraints, key dynamics of tension & balance. Solution: Description of the solution. Graphic: A depiction of response dynamics. Examples: Referenced cases where the pattern is employed. Agility: Evidence of SAREPH characteristics that qualify the pattern as agile. References: Literature access to examples. www.parshift.com/Files/PsiDocs/Pap100317Cser-OnDiscoveryAndDisplayOfAgileSecurityPatterns.pdf
www.parshift.com/Files/PsiDocs/Pap100317Cser-OnDiscoveryAndDisplayOfAgileSecurityPatterns.pdfwww.parshift.com/Files/PsiDocs/Pap100317Cser-OnDiscoveryAndDisplayOfAgileSecurityPatterns.pdf Dove, Rick and Laura Shirey. On Discovery and Display of Agile Security Patterns. 2010. 8th Conference on Systems Engineering Research March 17-19, Hoboken, NJ. www.parshift.com/Files/PsiDocs/Pap100317Cser-OnDiscoveryAndDisplayOfAgileSecurityPatterns.pdf
circa 2011 Pattern: Horizontal Gene/Meme Transfer Intrachromsomal genes Extrachromosomal genes Rules Packaging Transfer Entry Establishment Inheritance Available high varietycellular organisms Two modular gene pools Innovative adaptation and evolution Horizontal gene transfer speeds up innovative short-term adaptation and long-term evolution (Dove, Rick. 2011. Webinar: Toward a Systemic Will to Live –Patterns of Self-Organizing Agile Security. www.parshift.com/Files/PsiDocs/PatternQualificationsForAgileSecurity.pdf )
Pattern: Horizontal Meme Transfer • Examples: • Horizontal gene transfer and evolution. (Woese 2000) & (Smets 2005). • Cross-domain user-behavior-channeling pattern catalog. (Lockton 2009, 2010) • Cross-domain dynamic-system process-pattern project. (Troncale 1978, 2006) • Universal patterns in human activity and insurgent events. (Bohorquez 2009). • Patterns in behavioral ecology and anti-predator behavior. (Blumstein 2010). • Tradeoff between robustness and fragility in evolving complex systems. • [S]elf organization controls the assembly process. • [A]daptation occurs in assemblies that meet needs. • [R]eactive resilience occurs with sufficient module mix to meet specific needs. • [E]volution occurs in module and protocol upgrades. • [P]roactive innovation occurs with speculative assemblies for unknown needs. • [H]armony is maintained with a Highly Optimized Tolerance (Carlson 2002) small module and protocol repertoire in the knot. • References: (see reference section, only URLs shown here. All accessed 1Jan2011)) • (Blumstein 2010) www.eeb.ucla.edu/Faculty/Blumstein/pdf%20reprints/Blumstein_2010_BE.pdf • (Bohorquez 2009) www.nature.com/nature/journal/v462/n7275/full/nature08631.html • (Carlson and Doyle 2000) www.pnas.org/content/99/suppl.1/2538.full.pdf+html • (Lockton 2009) http://bura.brunel.ac.uk/bitstream/2438/3664/1/Lockton_SI_paper_disclaimer_added.pdf • (Lockton 2010) http://danlockton.com/dwi/Download_the_cards • (Smets 2005) www.nature.com/nrmicro/journal/v3/n9/pdf/nrmicro1253.pdf • (Troncale 1978) www.allbookstores.com/author/International_Conference_On_Applied_General_Systems_Research_State_Uni.html • (Troncale 2006) http://www3.interscience.wiley.com/journal/112635373/abstract?CRETRY=1&SRETRY=0 • (Woese 2000) www.ncbi.nlm.nih.gov/pmc/articles/PMC26958/pdf/pq008392.pdf From: Pattern Qualifications and Examples of next Generation Agile System-Security Strategies. www.parshift.com/Files/PsiDocs/PatternQualificationsForAgileSecurity.pdf
Pattern: Bow Tie Processor (assembler/generator/mediator) Millions of random infection detectors generated continuously by fixed rules and modules in the “knot” V1 Vn V: 123 Variable segments D: 27 Diverse segments J: 6 Joining segments ~106 VDJ+VJ possible antigen detectorshapes 123 Vs Dn D1 27 Ds Jn J1 increases to ~109 varieties with addition of random nucleotide connections between VDJ & VJjoinings 6 Js 1 random from each + random connect r Dr r Jr Vr Available high varietygenetic DNA input Evolve three fixed V-D-J gene-segment libraries Fixed-rule VDJ assembly with random interconnects Random high variety output with VDJ + VJ assemblies
Pattern: Bow Tie Processor (assembler/generator/mediator) • Example: Immune system--Millions of random infection detectors are generated continuously by fixed rules and modules • Example: For immune system assembly process (Wikipedia 2010). For numbers (Li 2004). • Example: Bow tie architecture for detector generation and sense-making. (Dove 2010). • Example: Bow tie architecture for robust complex networks of many kinds. (Csete 2004). • Example: General bow tie architecture and flexible-standards generation. (Hartzog 2010). • [S]elf organization controls the assembly process. • [A]daptation occurs in assemblies that meet needs. • [R]eactive resilience occurs with sufficient module mix to meet specific needs. • [E]volution occurs in module and protocol upgrades. • [P]roactive innovation occurs with speculative assemblies for unknown needs. • [H]armony is maintained with a Highly Optimized Tolerance (Carlson 2002) small module and protocol repertoire in the knot. • References: (see reference section, only URLs shown here. All accessed 1Jan2011) • (Carlson 2002) http://gabriel.physics.ucsb.edu/~complex/pubs/hot2.pdf • (Csete 2004) http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.173.3019&rep=rep1&type=pdf • (Dove 2011) www.parshift.com/s/110411PatternsForSORNS.pdf • (Hartzog 2010) http://blog.p2pfoundation.net/how-different-is-your-bow-tie/2010/06/21 • (Li 2004) http://bloodjournal.hematologylibrary.org/cgi/reprint/103/12/4602.pdf • (Wikipedia 2011) http://en.wikipedia.org/wiki/V(D)J_recombination From: Pattern Qualifications and Examples of next Generation Agile System-Security Strategies. www.parshift.com/Files/PsiDocs/PatternQualificationsForAgileSecurity.pdf
V--D--J V--J Pattern: Drag-and-Drop Framework and ModulesExample: Adaptable Immune SystemBow-Tie Antigen-Detector Generator detector antibody B-Cell Y cell Modules Integrity Management randomnucleotides 27 D segments 6 J segments 123 V segments Module pools and mix evolution genetic evolution Module inventory condition ??repair mechanisms?? Detector assembly bone marrow and thymus Infrastructure evolution genetic evolution Active longchain longchain longchain shortchain shortchain shortchain Infrastructure Passive detector sequence n+1 detector sequence n detector sequence n+2 Use one each V-J Use one each V-D-J Add random nucleotides Combine two assemblies Assembly Rules From: Pattern Qualifications and Examples of next Generation Agile System-Security Strategies. www.parshift.com/Files/PsiDocs/PatternQualificationsForAgileSecurity.pdf
Pattern: Proactive Anomaly Search Speculative generation and mutation of detectors recognizes new attacks like a biological immune system
Pattern: Proactive Anomaly Search Dove, Rick, Patterns of Self-Organizing Agile Security for Resilient Network Situational Awareness and Sense-Making. 2011. www.parshift.com/Files/PsiDocs/PatternsForResilientNetworks.pdf
Pattern: Hierarchical Sensemaking Four level feed forward/backward sense-making hierarchy modeled on visual cortex
Pattern: Hierarchical Sensemaking Dove, Rick, Patterns of Self-Organizing Agile Security for Resilient Network Situational Awareness and Sense-Making. 2011. www.parshift.com/Files/PsiDocs/PatternsForResilientNetworks.pdf
Previous Pattern References1/2 • Blumstein, Daniel T. 2010. Flush Early and Avoid the Rush: A General Rule of Antipredator Behavior? Behavioral Ecology, 21: 440-442, 26 March. • Bohorquez, Juan Camilo , Sean Gourley, Alexander R. Dixon, Michael Spagat and Neil F. Johnson. 2009. Common Ecology Quantifies Human Insurgency. Nature, 462(7275), 17 December, pp 911-914. • Carlson, Jean and John Doyle. 2000. Highly Optimized Tolerance: Robustness and Design in Complex Systems, Physical Review Letters 84 (11): 2529–2532, 13 March. • Carlson, Jean and John Doyle. 2002. Complexity and Robustness. PNAS 99: 2538–2545, 19 February. • Csete, Marie and John Doyle. 2004. Bow Ties, Metabolism and Disease. TRENDS in Biotechnology 22(9), September. http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.173.3019&rep=rep1&type=pdf • Csete, Marie and John Doyle. 2010. Bow Ties, Metabolism and Disease, TRENDS in Biotechnology 22(9), September 2004. www.cds.caltech.edu/~doyle/CmplxNets/Trends.pdf. • Dixon, Colin, Anderson, Thomas and Krishnamurthy, Arvind, Phalanx: Withstanding Multimillion-Node Botnets, NSDI'08: Proceedings of the 5th USENIX Symposium on Networked Systems Design and Implementation, April 2008. • Dove, Rick and Laura Shirey. 2010. On Discovery and Display of Agile Security Patterns. Conference on Systems Engineering Research, Stevens Institute of Technology, Hoboken, NJ, March 17-19. www.parshift.com/Files/PsiDocs/Pap100317Cser-OnDiscoveryAndDisplayOfAgileSecurityPatterns.pdf • Dove, Rick. 2011. Patterns of Self-Organizing Agile Security for Resilient Network Situational Awareness and Sensemaking. 8th International Conference on Information Technology: New Generations (ITNG), April 11-13, Las Vegas, NV. www.parshift.com/s/110411PatternsForSORNS.pdf • Edge, Kenneth S., Gary B. Lamont, and Richard A. Raines, Multi-Objective Mobile Network Anomaly Intrusion, International Journal of Computer Science and Network Security, 6(3b):187-192, March, 2006. • Forrest, S., S. Hofmeyr and A. Somayaji. 2008. The evolution of system-call monitoring. Proceedings of the 2008 Annual Computer Security Applications Conference, pp. 418-430. • George, Deleep. 2008. How the Brain Might Work: A Hierarchical and Temporal Model for Learning and Recognition, PhD thesis, Stanford University. www.numenta.com/htm-overview/education/DileepThesis.pdf • Hambling, Dave, Drone Swarm for Maximum Harm, Defense Tech. April 10, 2006. • Haack, Jereme N., Glenn A. Fink, Wendy M. Maiden, David McKinnon, and Errin W. Fulp. 2009. Mixed-Initiative Cyber Security: Putting Humans in the Right Loop. www.cs.wfu.edu/~fulp/Papers/mims09f.pdf • Hartzog, Paul. 2010. How Different is Your Bow Tie? Blog at P2P Foundation, 21 June 2010. http://blog.p2pfoundation.net/how-different-is-your-bow-tie/2010/06/21. • Hightower, R. , S. Forrest and A.S.Perelson. 1996. The Baldwin effect in the immune system: Learning by somatic hypermutation. In Adaptive Individuals in Evolving Populations, R. K. Belew and M. Mitchell, (eds.), Addison-Wesley, Reading, MA, pp. 159-167. http://cs.unm.edu/~forrest/publications/baldwin.pdf
Previous Pattern References2/2 • Hofmeyr , S. and S. Forrest. 2000. Architecture for an Artificial Immune System." Evolutionary Computation 7(1), Morgan-Kaufmann, San Francisco, CA, pp. 1289-1296. http://cs.unm.edu/~forrest/publications/hofmeyr_forrest.pdf • Khurana, Himanshu, Jim Basney, MehediBakht, Mike Freemon, Von Welch, Randy Butler. 2009. Palantir: A Framework for Collaborative Incident Response and Investigation. In Symposium on Identity and Trust on the Internet (IDTrust), Gaithersburg, MD, April 14-16. http://netfiles.uiuc.edu/hkhurana/www/IDTrust20091.pdf • Li, Aihong, et al. 2004. Utilization of Ig Heavy Chain Variable, Diversity, and Joining Gene Segments in Children with B-lineage Acute Lymphoblastic Leukemia: Implications for the Mechanisms of VDJ Recombination and for Pathogenesis. Blood, 103(12) 4602-4609, 15 June. • Lockton, Dan with Davis Harrison and Neville A. Stanton. 2010. Design With Intent - 101 Patterns for Influencing Behaviour Through Design. Equifine. April. Available at http://www.danlockton.com/dwi/Download_the_cards. • Lockton, Dan and David Harrison. 2009. Design for Sustainable Behaviour: Investigating Design Methods for Influencing User Behaviour. Sustainable Innovation 09: Towards a Low Carbon Innovation Revolution, 14th International Conference, Farnham Castle, UK, 26-27 October. • Mahimkar, A. , Dange, J., Shmatikov, V., Vin, H. and Zhang, Y., dFence: Transparent Network-Based Denial of Service Mitigation, in Proceedings of 4th USENIX Symposium on Networked Systems Design and Implementation (NSDI 2007), Cambridge, MA, April, 2007. • Serre, T., Learning a Dictionary of Shape-Components in Visual Cortex: Comparison with Neurons, Humans and Machines, Ph. D Dissertation, Massachusetts Institute of Technology, June, 2006. http://cvcl.mit.edu/Papers/SerreOlivaPoggioPNAS07.pdf • Smets, Barth F. and Tamar Barkay. 2005. Horizontal gene transfer: perspectives at a crossroads of scientific disciplines. Nature Reviews Microbiology 3, 675-678 (September 2005). • Troncale, L. 1978. Linkage Propositions Between Fifty Principal Systems Concepts. in Applied General Systems Research: Recent Developments and Trends : N.A.T.O. Conference Series II, Systems Science, G. J. Klir, (Ed.), Plenum Press, pp 29-52. • Troncale, L. 2006. Towards A Science of Systems. Systems Research and Behavioral Science, Special Journal Edition on J.G. Miller, Founding Editor (G.A. Swanson, Ed.) 23(3): 301-321. • Wilkinson, Sophie, Plants to Bugs: Buzz Off!, Chemical and Engineering News, June 30, 2001. • Woese, Carl. 2000. Interpreting the universal phylogenetic tree. PNAS. 97(15):8392-6. www.ncbi.nlm.nih.gov/pmc/articles/PMC26958/pdf/pq008392.pdf • Zhang, C., Zhang, J., Liu, S., and Liu, Y., Network Intrusion Active Defense Model Based on Artificial Immune System. Fourth International Conference on Natural Computation, Jinan, China, October 18-20, 2008.
Core Patterns of Biological Systems(currently half-baked hypothesis, maybe a framework for a Pattern Language) autocatalysis (self-reproductive life itself) (Early pattern work exists for the green area, nothing yet for yellow) horizontalmemetransfer geneticalgorithm modules and framework fractal architecturalreflection hierarchical sensemaking negativeselectionanomalydetection bow tie processor active infrastructure (will to live, ego, personality) This is only a current conjecture, and subject to radical evolution