Simulation-Based Verification
Speaker: Hsiu-Yi Lin. Simulation-Based Verification. Outline. Functional verification: Formal verification Simulation-based Verification Constraint-Based Random Test Generation Mutation-based Technology. Functional Verification. Formal Verification Simulation-based Verification.

Simulation-Based Verification
E N D
Presentation Transcript
Speaker: Hsiu-Yi Lin Simulation-Based Verification
Outline • Functional verification: • Formal verification • Simulation-based Verification • Constraint-Based Random Test Generation • Mutation-based Technology
Functional Verification • Formal Verification • Simulation-based Verification
Formal Verification • Use mathematical techniques to ensure that a design is the same with the specification of function. • Perform exhaustive proof through rigorous logical reasoning • Because the design size , complexity, time-to market pressure increase, it is impracticable to verify the design only by formal methods. • Example: ROBDD, Model checking, equivalence checking
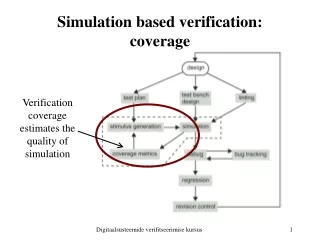
Simulation-based Verification • Require input stimuli. • It is popular way for design validation • It can find the hard-to-hit coverage points • acquire insight into the design and then use this to make decisions about test generation
Example: digital lock state machine • We use input sequence “1-2-3-4” to verify the design
Constraint-Based Random Test Generation(CRTG) • Only legal input values will be generated • Explore a large part of the input space efficiently with minimal user effort • Find bugs early and get good coverage quickly
“Digital lock state machine” example exhaustive input space 1111 1112 …. 2222 2223 …. 3333 3334 …. 4444 4441 ….. All combination
“Digital lock state machine” example exhaustive input space 1234 1111 1112 …. 2222 2223 …. 3333 3334 …. 4444 4441 ….. All combination the inputs of achieving verification closure
“Digital lock state machine” example exhaustive input space 1234 2314 4123 …. 1234 the inputs of achieving verification closure The inputs generated by the CRTG (different digits)
CRTG Flow Constrained random test generator Design Simulation Checker Test-Bench Hard-to-hit coverage points Coverage Analysis Manual inspection
Modification • Acquire insight into the design and then use this to make decisions about test generation
Intelligent Verification Closing the Test Generation Loop Constrained random test generator + information derived from the design Design Simulation Checker Test-Bench simulation result
“Digital lock state machine” example exhaustive input space 1234 1234 2314 4123 …. the inputs of achieving verification closure The inputs generated by the CRTG (different digits)
“Digital lock state machine” example exhaustive input space 1234 1234 2314 4123 …. 1+ 234 1+ 243 the inputs of achieving verification closure The inputs generated by the CRTG (different digits)
Hard-to-hit coverage points • If there are 10000 digits in the lock state machine?
Find the hard-to-hit coverage points Covered by CRTG S1 S5 S2 S4 S3 signal A = 1 S6 Hard-to-hitpoints S7 S8 signal B&C = 1 signal D = 0
Find the hard-to-hit coverage points Covered by CRTG S1 S5 S2 S4 S3 signal A = 1 S6 Hard-to-hitpoints “signal A = 1” is a simulation result and feedbacks to CRTG to generate new constraints S7 S8 signal B&C = 1 signal D = 0
Coverage Measure in Verification • Avoid duplication of verification effort • Direct further effort before verification closure • Mutation-based technology is used in dynamic verification
Mutation-based Technology • Analyze small behavioral change to a software program, and intend to find weakness in the functional testing of a program • Find the weakness in the verification environment • It is similar to fault simulation in VLSI testing
Mutation-based Technology Design (with small behavioral change ) Catch the fault or not? Test input Simulation with the test-bench
Mutation Example • Original program code a = b or c Mutated program a = b and c • Check whether we catch the fault in the simulation result
Future Work • Meeting with Shih-Chieh’s Lab • Study