NAC-NAP Interoperability
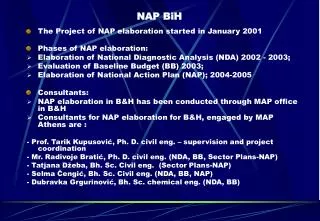
NAC-NAP Interoperability. Michal Remper Systems Engineer mremper@cisco.com. Directory Server. Posture Validation Server(s). Audit Server. Patch Server. Reporting Server. ACS. Who we are ? 4 years NAC experiences …. Decision & Remediation. Subject (Managed or Unmanaged host).

NAC-NAP Interoperability
E N D
Presentation Transcript
NAC-NAP Interoperability Michal Remper Systems Engineer mremper@cisco.com
Directory Server Posture Validation Server(s) Audit Server Patch Server Reporting Server ACS Who we are ? 4 years NAC experiences … Decision &Remediation Subject (Managed or Unmanaged host) Enforcement LAN WAN Remote
How we see Microsoft? • Microsoft owns 97.46% of global desktop operating system market (over 90% in Enterprise) • Microsoft is a strategic component of business operations for nearly all of our customers Any NAC solution must fully support a Microsoft environment
What is the difference between NAC & NAP ? … NAC and NAP have different goals …
What is the difference between NAC & NAP ? NAC ensures that all users and devices coming into the network comply with an endpoint security policy. NAP seeks to guarantee that users and devices connecting to a specific MS server meet an endpoint security policy. Cisco and Microsoft have publicly stated that the two companies will work to integrate these two approaches.
Network Admission Control Network Access Protection History Announcement originally made in October 2004. Since then… • Unveiled at The Security Standard show in Sept 06 including press announcement and live demo • Joint Beta program began in Dec 06 with two customers…no, one is not Cisco IT
Status Today • Joint testing between Cisco and Microsoft including bug fixes is ongoing and includes weekly status calls for tracking • Documentation has been developed which includes presentations, deployment and troubleshooting guides • Beta 1 is wrapping up with Beta 2 slotted for June start. • Beta 1: Inband Posture • Beta 2: Wireless, SSO, Extended States, MAB
Why Did We Create a Joint Solution? • Customer Driven • Cisco and Microsoft interoperability help customers achieve their strategic initiatives • Don’t have to choose between NAC-only or NAP-only solution.
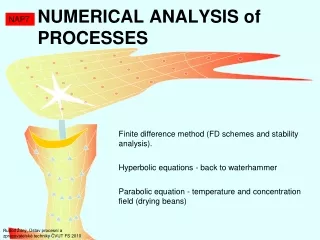
Key: Optional Mandatory 4a Identity 7 Enforcement 5 2 3 Compliant? Credentials 4b Credentials Posture Notification 8 4c 6 Audit Authorization Status 9 NAC Admission Flow Host Attempting Network Access Network Access Devices (NADs) Cisco Secure ACS Policy Server Decision Points & Audit Traffic triggers challenge 1 Directory Server LDAP, OTP Policy Vendor Server (PVS) EAP HCAP RADIUS Audit Server (AS) Cisco Trust Agent (CTA) GAME: HTTPS
Network Admission Control Network Access Protection What is Available in the Joint Solution? 802.1x EoU DHCP IPSEC VPN 802.1x Health Certificates 802.1x EoU
NAC-NAP Architecture MS Partner Components Cisco Components Microsoft Components Microsoft Components Client Partner Policy Server Switches Routers Cisco ACS MS NPS Partner System Health Agents (SHAs) EAPFAST 802.1x or UDP HCAP RADIUS NAP Agent (QA) EAP-FAST EAP Host QEC EAPoUDP 802.1x • We have referred to this as the In-Band (HCAP) Scenario • Access methods include 802.1x and EoU • Authentication is performed on ACS. Posture checking is performed on NPS. • HCAP v2 is the secure transport method for credentials and policy information between ACS and NPS
NAC-NAP Benefits • Interoperability and customer choice:Customers can choose components, infrastructure and technology while implementing a single, coordinated solution • Investment protection: Enables customer reuse and investment protection of their NAC and/or NAP deployments. • Single agent included in Windows Vista: The NAP Agent component as part will be used for both NAP and NAC. • Agent deployment and update support: Microsoft will distribute Cisco EAP modules through Windows Update / Windows Server Update Services • Cross-platform support: To support client operating systems other than Windows, Microsoft will make available the APIs that support both NAP and Cisco NAC and Cisco will continue to support and develop its NAC client (the Cisco Trust Agent) for non-Windows environments.
Solution Details • ACS support for NAC-NAP is in the 4.2 release. This is currently set for Dec 07 • MS Longhorn is required for NAP and NAC-NAP. This will be released at the end of Dec 07. • NAP-only agent is available for XP. • Cisco has no plans to support the NAC-NAP solution for anything prior to Vista • There is no CTA for Vista. The NAP agent handles both NAC and NAP information for Vista
Vista Client Architecture Statement of Health (SoH) aka posture credentials– Encapsulation of endpoint posture sent from an endpoint SHA to its SHV. The SoH is a response to a request for health state. System Health Agents (SHA) aka posture pluggin– SHAs are responsible for reporting on the health state of the client. Each configured SHA reports health state to the NAP Agent. A SHA will also accept statement of health response data and will optionally remediate the client. NAP Agent aka CTA– QA is responsible for collating the statement of health information from the SHAs into a single system statement of health. QA also accepts the System statement of health response, parses it into individual statements of health to be passed to the SHAs. EAP Host– A plug in architecture for Network Authentication components. There will be a partner program where Microsoft will certify components and distribute them through Windows Update. Client Partner System Health Agents (SHAs) NAP Agent (QA) EAP Host QEC EAP-FAST EAPoUDP 802.1x
Microsoft Server and Partner Components • NPS Server (Longhorn) • Replaces IAS • Place to define NAP enforcement and remediation policies. (RADIUS access policies for NAP-only) • Implements HCAP v2 for ACS communication • Support for SHV API and installation of SHVs • MS Partner Program • Very similar to the way the Cisco NAC program is setup • Partners develop interoperability through the SHA and SHV APIs Client Updates Policy Servers Network Policy Server SHA 1 SHA 2 SHV 1 SHV 2 Health policy Remediation Servers Quarantine Agent (QA) QEC 1 QEC 2 Quarantine Server (QS)
Cisco ACS What About Cisco Components • Any Cisco device that works with NAC will work with NAC-NAP !!! • Currently ACS 4.2 will support NAC-NAP. Will support a heterogeneous environment of NAC & NAC-NAP
Access Methods for NAC-NAP Client Switches Routers Cisco ACS Partner System Health Agents (SHAs) RADIUS 802.1x or EoU NAP Agent (QA) EAPFAST EAP Host QEC EAP-FAST EAPoUDP 802.1x • EAP-FAST– The transport method for SoH. The method will be deployable via group policy and downloadable via Windows Server Update Services • EAPoUDP– Layer 3 method similar to the NAC-only deployment. In the NAC- NAP solution EoU relies on EAP-FAST. EoU will also be deployable via group policy and downloadable via WSUS • 802.1x–The Windows Vista 802.1x supplicant will be NAC-NAP enabled and will fully support both wired and wireless access
Client Statement of Health Process Health Validation Events Health State Change – An SHA may notify the NAP Agent if it’s health state change. For example, the Windows firewall is turned off Network State Change – A QEC may notify the NAP Agent that there is a network state change. For example, a wireless client roams to a new network Probation Timer – The probation time expires Partner System Health Agents (SHAs) SoH Creation Process • Health validation event occurs • NAP Agent requests SoH data from all bound SHAs • SHAs respond with SoH data • NAP Agent collects all SHA data and adds system SoH data to create a system SSoH. • NAP Agent forward SoH to the all configured QECs NAP Agent (QA) HC QEC EAP Host QEC
Key Takeaways Main points to keep in mind: • This solution will be available around the end of CY07 when ACS 4.2 and Longhorn Server ships. • NAC-NAP only supported on Vista and Longhorn • Customer can still do NAC only or NAP only • Currently POCs are not available for customers outside of the beta