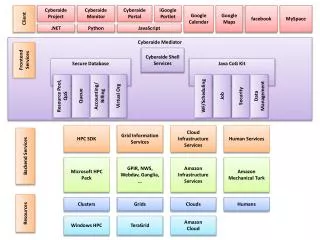
Implicit Self-Registration for KMIP Entities
Learn how to implicitly register entities with KMIP server through TLS certificates and access control methods. No special TTLV required. Easily manage credentials and access.

Implicit Self-Registration for KMIP Entities
E N D
Presentation Transcript
Client Registration Examples Alan Frindell Denis Pochuev 4/26/2011
Certificate Entity: Implicit self-registration • Server implicitly creates Entity record as a side effect of another KMIP request • No special TTLV required – KMIP server extracts needed values from TLS certificate • Client MAY already have a cert signed by a CA trusted by KMIP server • Resulting Object: Entity UUID: ABCD-1234 Credential Credential Type: Transport Certificate Credential Value: Certificate Certificate Type: X.509 Certificate Value: <cert>
Certificate Entity: Explicit self-registration Register Object Type=Entity Template-Attribute Credential Credential Type: Transport Certificate Credential Value: <empty> x-custom1: custom-value1 x-custom2: custom-value2 Entity: <empty> • Certificate fields extracted from TLS
Certificate Entity: Registration Register Object Type=Entity Template-Attribute Credential Credential Type: Transport Certificate Credential Value: Certificate: <certificate> x-custom1: custom-value1 x-custom2: custom-value2 Entity: <empty> • Assumption: Registering Entity has privilege to register Entities
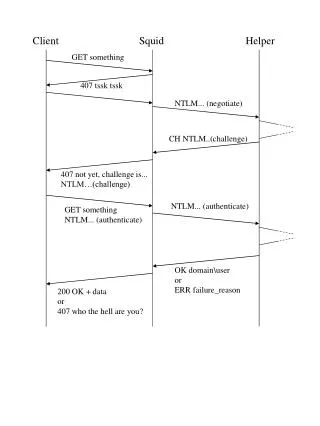
Certificate Entity: Authentication and Access Control Authentication Credential Credential Type: Transport Certificate Credential Value: <empty> • Server looks up Entity based on TLS certificate information • Server policy: may be dynamic mapping or exact match • For access control, server checks authenticated Entity UUID against request object Owner attribute
Username/Password User: Registration Register Object Type=Entity Template-Attribute Credential Credential Type: Username and Password Credential Value: Username: “user1” Password: “password” x-custom1: custom-value1 x-custom2: custom-value2 Entity: <empty>
Username/Password User: Authentication and Access Control • Same as v1.0 Authentication Credential Credential Type: Username and Password Credential Value: Username: “user1” Password: “password” • Server looks up Entity based on Credential (username) • For access control, server checks Entity UUID against request object Owner attribute
Multi-factor Entity: Registration Register Object Type=Entity Template-Attribute Credential Credential Type: Transport Certificate Credential Value: Certificate: <certificate> Credential Credential Type: Username and Password Credential Value: Username: “user1” Password: “password” x-custom1: custom-value1 x-custom2: custom-value2 Entity: <empty>
Multi-factor Entity: Authentication Authentication Credential Credential Type: Transport Certificate Credential Value: <empty> Credential Credential Type: Username and Password Credential Value: Username: “user1” Password: “password” • Server looks up Entity based on each Credential – all must resolve to the same Entity • For access control, server checks Entity UUID against request object Owner attribute
Locate Entity • Find all Entities with Transport Certificate Credentials: Locate Credential Credential Type: Transport Certificate • Find an Entity by its transport certificate: Locate Credential Credential Type: Transport Certificate Credential Value: Certificate: <certificate> • Find yourself: Locate Entity Identifier = Self
Credential Refresh Modify Attribute Attribute: “Credential” Attribute Index: N Attribute Value: Credential Type: Transport Certificate Credential Value: Certificate: <certificate> Modify Attribute Attribute: “Credential” Attribute Index: N Attribute Value: Credential Type: Username and Password Credential Value: Username: “user1” Password: “new-password”
Other operations • Get Entity Info Locate Entity Identifier = Self Get Attributes Attribute Name: “Credential” • Note server is not allowed to return Password values • Destroy Entity Destroy UUID: “ABCD-1234”