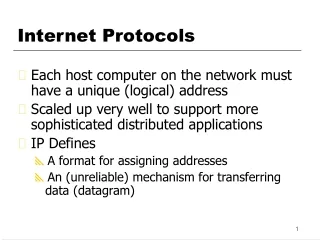
Class 3 Internet Protocols
Class 3 Internet Protocols . CSCI 6433 David C. Roberts. Agenda. Internet Protocol Routing Error and Control Messages. Internet protocol. Internet Services. Much of the Internet’s success is due to the robustness and adaptability of this architecture. Goals for IP.

Class 3 Internet Protocols
E N D
Presentation Transcript
Class 3Internet Protocols CSCI 6433 David C. Roberts
Agenda • Internet Protocol • Routing • Error and Control Messages
Internet Services Much of the Internet’s success is due to the robustness and adaptability of this architecture.
Goals for IP • Universally addressed—IP defines addressing mechanism for the network and uses these addresses for delivery • Independent of underlying protocol—IP is designed to operate over any lower-level protocol that will work with TCP/IP • Connectionless—operates without defined connections • Unreliable—devices just send each datagram and then go on to the next one, don’t wait to check success • No acknowledgement—datagrams are delivered without a “thank you” note
Basic Functions of IP • Addressing: mechanism for unique addressing across the entire Internet • Data Encapsulation and Packaging: accepts data from the transport layer protocols at a higher level, encapsulates them into an IP datagram, and passes them to the lower level for transmission • Fragmentation and reassembly: If the message exceeds maximum frame size, IP fragments it into multiple datagrams, and reassembles them at the destination. If a router along the communication path fragments a datagram, the same reassembly takes place at the destination. • Routing: sends a datagram to a distant network using routers
Why Is IP Successful? • It’s simple • Hardware, software to implement it are simple • Simplicity leads to low cost and high performance
Datagram Encapsulation Datagram can be any length. Desirable for datagram to be carried in a single physical frame. Physical network does not know about datagram header. Different physical networks have different frame sizes, so datagrams must sometimes be fragmented into frames. Routers must accept datagrams up to maximum MTU of the networks they connect to.
IPv4 Fragmentation Fragmentation can occur at any router along the path taken by a datagram. Fragment headers are like datagram header, except for flag that shows that it is a fragment.
IPv6 Fragmentation • Source host required to find minimum MTU along path to the destination • Message is to be sent in datagrams that will fit into minimum MTU on path to the destination • Source host uses path MTU discovery (PMTUD) to find the MTU of the path to the destination • Fragmented IPv6 datagrams use a Fragment Extension Header
Datagram Reassembly • Where are fragments reassembled? • At the destination • When entering network with high enough MTU • Reassembled at destination • Avoids refragmentation and reassembly • Allows each to be separately routed
Direct, Indirect Delivery • Direct delivery • Transmission of a datagram between two machines on a single physical network • Also the final step in indirect delivery • Indirect delivery • Transmission of a datagram between two machines that are not connected to the same network • Sender chooses router, sends datagram to it • Router extracts datagram from message, encapsulates it and sends it to another router
Direct Delivery • Sender encapsulates the datagram in a physical frame • Next-hop address is bound to destination machine’s physical hardware address • Resulting frame is sent directly to the destination machine Question: How does the sending machine know whether to use direct delivery?
Indirect Delivery • Sending host encapsulates datagram in a frame and sends to the nearest router • Router software extracts the encapsulated datagram and IP software selects the next router to receive it (or uses direct delivery) • Datagram is placed into a frame and sent over the second physical network to the next router • This continues until a router is reached that can use direct delivery
Table-Driven Forwarding • Hosts and routers have IP forwarding tables • Forwarding table gives “next hop”—where to send a datagram as its next step toward its destination • Size of forwarding table is an issue • Can’t have information about all possible hosts • IP forwarding is done on a network basis • Default next hop is used for networks not listed in routing table • Host-specific routes are useful for some situations
Next-Hop Forwarding • Next-hop forwarding helps to keep forwarding tables small • Forwarding tables tend to have nearby networks • Forwarding table is a set of pairs (N,R) • N is network prefix for an Internet network • R is the IP address of the “next hop” router to reach N • Each R is a router that is reachable across a single network
Hosts discard datagrams not intended for them; but routers must forward them First, if datagram is for an attached network, then it is sent on the attached network If not, then TTL field is decremented; if it reaches zero, then datagram is discarded Routing table is used to select outgoing network, net hop address Datagram is sent to the next hop IP address Processing Incoming Datagrams
Default Routes • IP forwarding software first looks for the destination network in its forward table • If not found, then the default next-hop address is used • Useful if many networks are reached through a single router
Broadcast and Multicast • Forwarding becomes more complex when broadcast and multicast are included • These will be covered later
Establishing Forwarding Tables • IP forwarding relies on correct information in forwarding tables • These must be correct across the entire Internet • Their maintenance is a significant job • To be discussed later
Summary • Routing is the method used to forward IP datagrams • Choice of where to send datagram is based on destination network address • Routing algorithm chooses next hop for a datagram • With few exceptions, routing is based on destination address only
Question • Suppose a router can’t contact the next hop router to forward a datagram • What should that router do? • Should it contact the router that sent it the datagram?
Initial purpose of ICMP was to allow routers to report the cause of delivery errors to hosts Any machine can send an ICMP message to any other machine, although some ICMP messages are sent only by routers ICMP is used to report problems to the source of the datagram Router finding an error cannot report the error to other routers that have processed the datagram Internet Control Message Protocol
Error Reporting, Error Correction • ICMP is an error reporting mechanism • Error correction is the job of machine receiving the message • Source may refer datagram back to the originating application or take other action
ICMP Message Encapsulation ICMP messages are encapsulated inside a datagram, travel the same way as every other datagram. Question: Can an IP datagram carrying an ICMP message, if it causes an error, cause another IP datagram to be sent with an ICMP message about the first ICMP message?
12 Datagram Parameter Problem 13 Timestamp Request 14 Timestamp Reply 15 Information Request 16 Information Reply 17 Address Mask Request 18 Address Mask Reply 0 Echo Reply 3 Destination Unreachable 4 Source Quench 5 Redirect 8 Echo Request 9 Router Advertisement 10 Router Solicitation 11 Datagram Time Exceeded ICMP Message Types Obsolete—formerly used by host to find router address, now replaced by RARP and DHCP
Ping • Echo Request and Echo Reply • Host sends ICMP echo request • Recipient sends ICMP echo reply to original sender • Verifies that major pieces of transport system are working • Host must route the datagram • Routers must operate, route the datagram • Destination machine must respond, its ICMP, IP software must be working • ICMP Echo Request command is often called Ping
Echo Request and Reply Message Format Sender uses IDENTIFIER and SEQ NUMBER to match replies to requests Echo reply sends back the data included in the request ??: When is 8 used and when is 0 used?
Destination Unreachable (3) When router can’t forward or deliver an IP datagram, it sends destination unreachable message back to original source and drops the datagram CODE field further describes the problem, such as network or host unreachable, destination host or network unknown, fragmentation needed and DF set
Congestion—router is overrun with traffic. Router enqueues messages that can’t be processed in memory. If high traffic continues, memory can be exhausted. Sources of congestion: Many computers send datagrams through one router High-speed computer sends many datagrams through a router connected to its network Datagrams can be enqueued in memory temporarily If memory is exhausted, then datagrams are discarded and Source Quench messages are sent Congestion and Flow Control
Source Quench Source quench is a request for the source to slow rate of datagram transmission. Usually router sends one message for every datagram that is discarded Source can identify the datagram that was lost by using the datagram prefix
Circular Routes Time exceeded message says that hop count has reached zero, or message has timed out on arrival of fragments of a datagram.
Parameter Problem Incorrect datagram header prevents delivery, and datagram must be discarded
Clock Synchronization First machine asks for timestamp, second machine sends current time of day Times in milliseconds since midnight, UT. Originate timestamp at time request was sent; receive is time of receipt of request, transmit time of transmission of reply.
Subnet Mask Subnet address mask specifies which part of IP address contains the network ID and which contains the host ID
Router Advertisement ICMP provides a method for a host to discover a router address dynamically, when router advertises its addresses; typically sent every ten minutes Other methods are available (BOOTP, DHCP) that depend on database set up by network administrator.
Router Solicitation New host can’t wait 10 minutes to find a router! Solicitation allows host to request immediate advertisement. Message is sent to all-routers multicast (24.0.0.2), if supported. Otherwise, send to limited broadcast address (i.e., all 1’s for hostid). In response, router sends normal router advertisement.