Advancements in EAP Security: The EAP-Archie Protocol Proposal
90 likes | 214 Vues
This document discusses the vulnerabilities associated with the MD5 Challenge method used in EAP authentication, which is deemed unsuitable for 802.11 due to heightened security risks. Jesse Walker and Russ Housley propose a new EAP authentication protocol, termed EAP-Archie, focusing on mutual authentication, prevention of man-in-the-middle attacks, and protection against dictionary attacks. The new protocol emphasizes the use of long-lived pre-shared secrets, lightweight operations, and guarantees a fresh session key to enhance overall security in wireless environments.

Advancements in EAP Security: The EAP-Archie Protocol Proposal
E N D
Presentation Transcript
EAP Archiedraft-jwalker-eap-archie-00.txt Jesse Walker, Intel Corporation Russ Housley, Vigil Security Walker & Housley
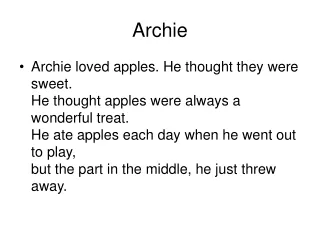
Background • Fact: IETF EAP WG has asked IEEE 802.11 TGi for guidance • Observation: The mandatory-to-implement EAP authentication method (MD5 Challenge) is unsuitable for 802.11 This increases market confusion around security! • Question: Is there a suitable replacement algorithm? • Answer: Not really Walker & Housley
Goals Design a candidate for a better EAP default: • Based on a long-lived pre-shared secret • Light weight; no public key operations • Mutual authentication • Prevent man-in-the-middle attacks • Protect against dictionary attacks if key is not weak • Guarantee a fresh session key Walker & Housley
Request: AS-ID, SessionID Response: Hash1, STA-ID, SNonce, Binding, MIC1 Confirm: Hash2, ANonce, Binding, MIC2 Finish: Hash3, MIC3 The Archie Exchange AS STA PSK PSK Walker & Housley
Next Steps Resolve: • Can MD5 Challenge be deprecated? Augmented? Delimited (so it is banned for wireless?) • Change to make EAP-Archie suitable for PPP? • Interest in evolving EAP-Archie into a standards track protocol? Walker & Housley
Feedback? Walker & Housley
Backup Walker & Housley
Archie PRF Algorithm Archie-PRF Input: Key K, Label L, Nonce N, Output Length OL Output:OL-octet string Out Out = “” fori = 1 to (OL+15)/16 do Out = Out | AES-CBC-MAC(K, L | N | i | OL) return first OL octets out of Out Walker & Housley
SK = Session Key = Archie-PRF(PSK, “Archie session key” | ASNonce | PeerNonce) TLS Master Key Pairwise Key = Archie-PRF(SK, “Archie pairwise key” | BSSID | STA MAC Addr) PMK EAP Archie Key Hierarchy PSK = Long-lived Pre-Shared Key = KCK | KEK | KDK Walker & Housley