EAP Archie
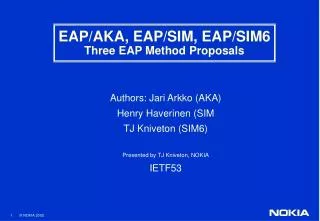
EAP Archie. Jesse Walker, Intel Corporation Russ Housley, Vigil Security. Background. Fact : IETF EAP WG has asked IEEE 802.11 TGi for guidance

EAP Archie
E N D
Presentation Transcript
EAP Archie Jesse Walker, Intel Corporation Russ Housley, Vigil Security Walker & Housley
Background • Fact: IETF EAP WG has asked IEEE 802.11 TGi for guidance • Observation: The mandatory-to-implement EAP authentication method (MD5 Challenge) is unsuitable for 802.11 This increases market confusion around security! • Question: Is there a suitable replacement algorithm? • Answer: Not really Walker & Housley
Goals Design a candidate for a better EAP default: • Based on a long-lived pre-shared secret • Light weight; no public key operations • Mutual authentication • Prevent man-in-the-middle attacks • Protect against dictionary attacks if key is not weak • Guarantee a fresh session key Walker & Housley
SK = Session Key = Archie-PRF(PSK, “Archie session key” | ASNonce | PeerNonce) TLS Master Key Pairwise Key = Archie-PRF(SK, “Archie pairwise key” | BSSID | STA MAC Addr) PMK EAP Archie Key Hierarchy PSK = Long-lived Pre-Shared Key = KCK | KEK | KDK Walker & Housley
Archie PRF Algorithm Archie-PRF Input: Key K, Label L, Nonce N, Output Length OL Output:OL-octet string Out Out = “” fori = 1 to (OL+15)/16 do Out = Out | AES-CBC-MAC(K, L | N | i | OL) return first OL octets out of Out Walker & Housley
Request: AS-ID, ARandom Response: Hash1, STA-ID, SNonce, Binding, MIC1 Confirm: Hash2, Counter2, ANonce, Binding, MIC2 Finish: Hash3, MIC3 The Archie Exchange AS STA PSK PSK Walker & Housley
Archie Features • Hash1 = SHA1(Request) • Hash2 = SHA1(Response) • Hash3 = SHA1(Confirm) • Defeats replay and reflection attacks • Each hash is a simple transaction id • Each hash ties msg to all prior msgs of this session • Explicit binding protects STA from man-in-the-middle attacks in the infrastructure • Derived SK is always fresh Walker & Housley
Status • Draft-jwalker-eap-archie-00.txt to be posted after San Fransisco IETF. • Attempt to stimulate discussion on what TGi needs from EAP WG. Walker & Housley
Feedback? Walker & Housley